[ad_1]
NEWYou can now listen to Fox News articles!
Over the past few years, data breaches targeting schools, healthcare providers, and childcare services have been making headlines, exposing sensitive personal information and leaving families vulnerable. Now, a new breach has come to light that targets a nursery chain. Kido, which operates in the U.S., U.K., China and India, has reportedly had sensitive data stolen from thousands of children. Names, photos, addresses, birthdates, parental details and even safeguarding notes and medical records were allegedly accessed by a hacker group called Radiant.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts, and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CyberGuy.com/Newsletter
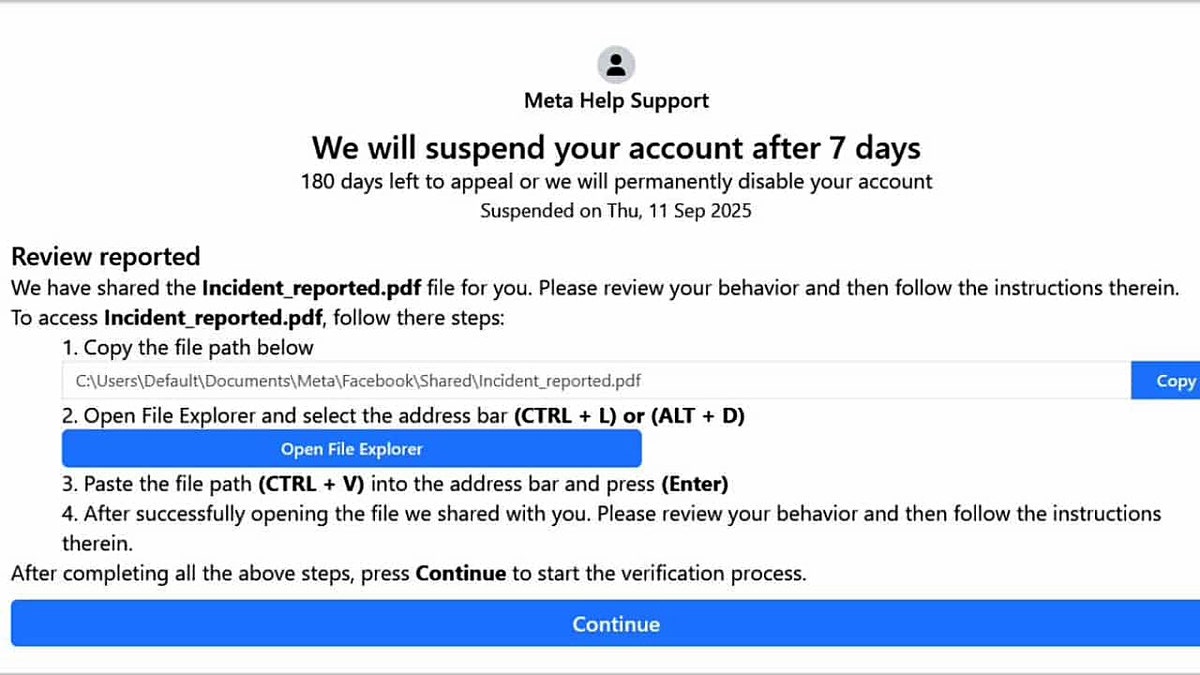
The incident highlights how stolen data threatens not just privacy but also long-term child safety. (Kurt “CyberGuy” Knutsson)
What you need to know about nursery breach
According to reports, the hacker group Radiant claims to have stolen data related to around 8,000 children. To prove possession, they posted samples, including pictures and profiles of ten children, on a darknet website. They then issued a ransom demand, threatening to release more sensitive information unless Kido paid. In addition to targeting the nursery chain directly, Radiant reportedly called some of the children’s parents, pressuring them to push Kido into paying the ransom.
FBI WARNS ABOUT NEW EXTORTION SCAM TARGETING SENSITIVE DATA
When questioned about their actions, the group defended their tactics as a form of “penetration testing” for which they supposedly deserved compensation. This defense is misleading, as such testing requires explicit permission from the organization being targeted or participation in an official bug bounty program. Without that consent, these actions are illegal and deeply unethical.

Hackers exploited children’s data in the Kido breach, exposing families to serious risks. (Kurt “CyberGuy” Knutsson)
Why is this attack so disturbing?
The Kido breach is alarming for multiple reasons. First, it involves children’s data, which is particularly sensitive and legally protected in most countries. Second, the attackers combined traditional data theft with intimidation tactics, reaching out to parents directly. History suggests that once criminals gain access to such information, the attacks can escalate.
Breaches like this highlight how personal and digital security are intertwined. The potential misuse of data extends beyond simple identity theft. It can impact children’s safety, family privacy and long-term well-being. With attackers leveraging both the stolen data and psychological pressure on parents, the threat is particularly potent and long-lasting.

Parents reported being directly contacted by attackers, showing how intimidation adds to the harm. (Kurt “CyberGuy” Knutsson)
7 steps parents can take to protect their child’s data
Even though the investigation into the Kido breach is ongoing, parents and schools can take immediate action to protect children’s data and reduce the risk of further exploitation. Here’s a detailed guide:
1) Monitor your child’s online accounts regularly
Log in to email, school portals and cloud storage accounts linked to your child. Look for unusual activity such as unrecognized logins, changes to passwords or new connected devices. Set up notifications for account activity whenever possible so you are alerted instantly if something suspicious happens.
2) Enable two-factor authentication (2FA) on all accounts
Adding 2FA creates an extra layer of security. Even if a hacker has a password, they won’t be able to access the account without the second verification step. Most email providers, school portals and messaging platforms support this, and it’s a simple step that dramatically improves security.
3) Consider a personal data removal service
Data broker sites often collect names, addresses and other personal details that hackers can use. Services that remove your child’s information from these databases can make it harder for attackers to find and exploit sensitive data.
While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting CyberGuy.com/Delete
Get a free scan to find out if your personal information is already out on the web: CyberGuy.com/FreeScan
THINK YOU’RE SAFE? IDENTITY THEFT COULD WIPE OUT YOUR ENTIRE LIFE’S SAVINGS
4) Use identity theft protection services
These services can continuously scan for your child’s personal information online and alert you if their data appears on suspicious websites or the dark web. This early warning allows you to take action before criminals attempt to exploit it.
Identity theft companies can monitor personal information like your Social Security Number (SSN), phone number and email address, and alert you if it is being sold on the dark web or being used to open an account. They can also assist you in freezing your bank and credit card accounts to prevent further unauthorized use by criminals.
See my tips and best picks on how to protect yourself from identity theft at CyberGuy.com/IdentityTheft
5) Install antivirus software on all devices
A strong antivirus program protects devices from malware, phishing scams, and suspicious scripts. It is particularly important on devices that children use to access school portals or personal accounts. This ensures that if a hacker tries to use malware to get deeper access, it is blocked.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android & iOS devices at CyberGuy.com/LockUpYourTech
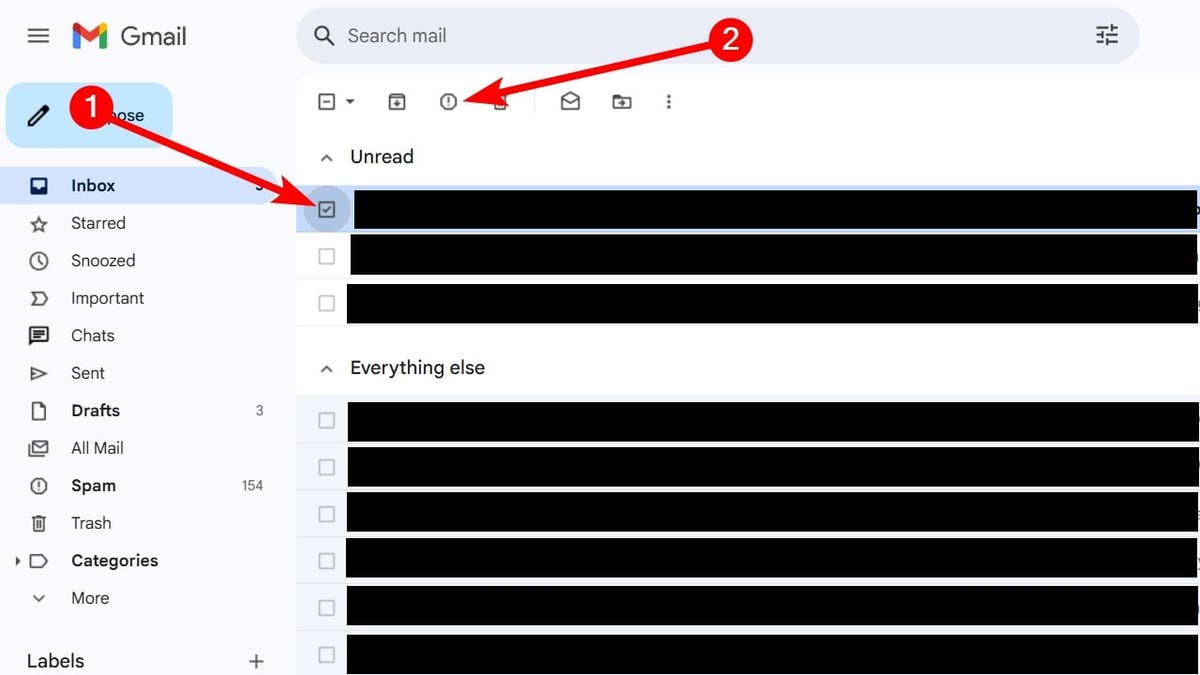
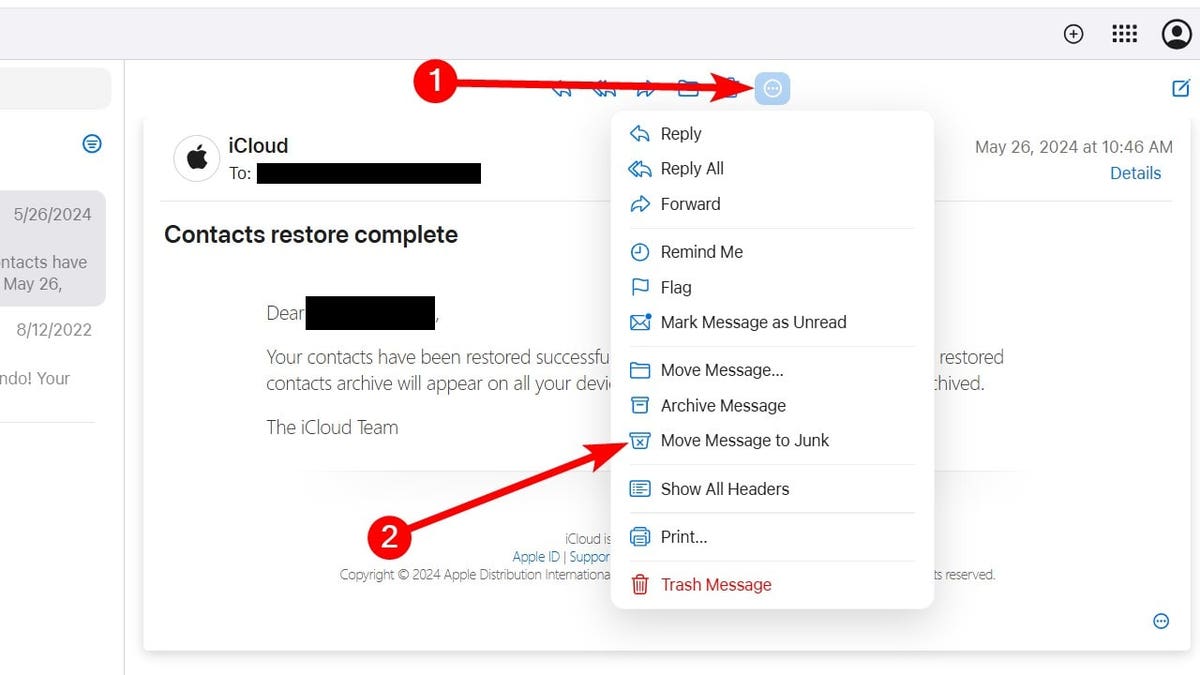
6) Use a secure mail provider for sensitive communications
For communications with schools, healthcare providers or any service handling sensitive information about children, consider using an email service that offers strong encryption and built-in protection against spoofing. This makes it harder for attackers to impersonate a school or parent.
For recommendations on private and secure email providers that offer alias addresses, visit CyberGuy.com/Mail
7) Educate your children about online safety
Teach children not to share personal information online, including photos, addresses or school details. Encourage them to report anything suspicious and explain why it’s important to keep login information private.
CLICK HERE TO GET THE FOX NEWS APP
Kurt’s key takeaway
Data breaches targeting children are particularly concerning because they can have long-lasting consequences. The Kido incident is a stark reminder of the importance of proactive digital security measures for families. While organizations bear responsibility for protecting sensitive data, parents can take significant steps to monitor, secure and respond to potential threats.
Have you ever reviewed what personal information about your child is online? Let us know by writing to us at CyberGuy.com/Contact
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts, and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CyberGuy.com/Newsletter
Copyright 2025 CyberGuy.com. All rights reserved.
[ad_2]