Russians team up with young, English-speaking hackers for cyberattacks | 60 Minutes…
Browsing Tag
Cybercrime
116 posts
UK government set to link China government-affiliated hackers to a cyberattack on election watchdog
LONDON — Britain’s government is expected to blame a string of cyberattacks…
The French government says it’s being targeted by unusual intense cyberattacks
FILE – French Prime Minister Gabriel Attal gestures as he speaks during…
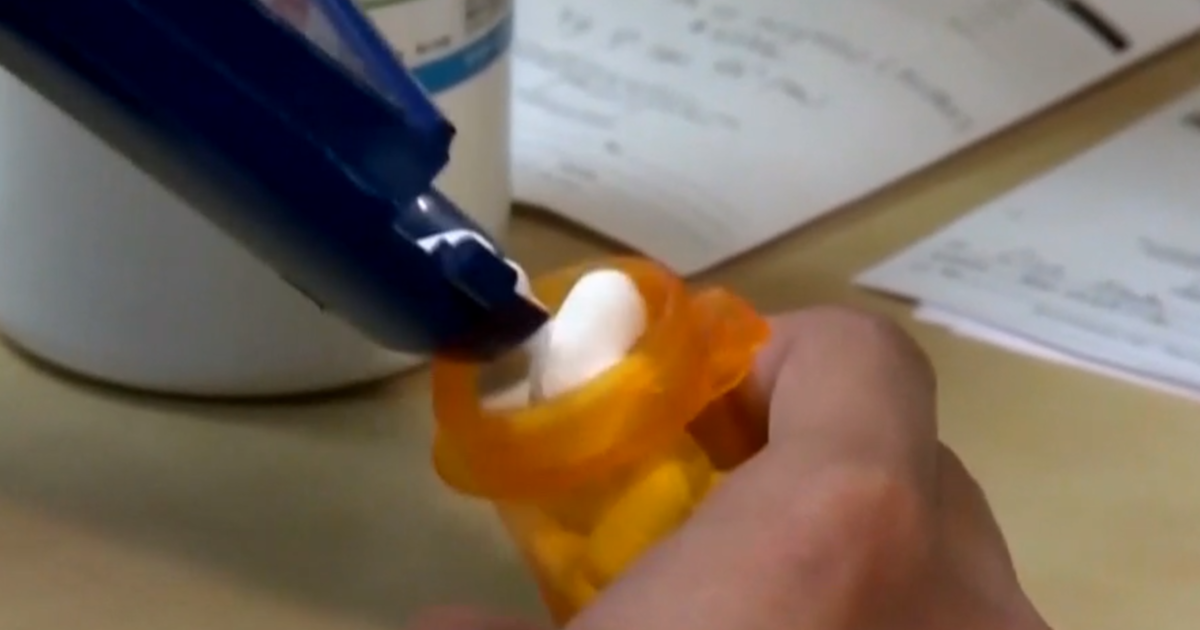
Cyberattack on UnitedHealth still impacting prescription access:
Washington — A cyberattack on the health technology provider Change Healthcare is…
Why are ransomware gangs making so much money? | TechCrunch
For many organizations and startups, 2023 was a rough year financially, with…
2/12: Prime Time with John Dickerson
2/12: Prime Time with John Dickerson – CBS News Watch CBS News…
Did a Hacker Gang Create a Botnet Out of 3 Million Electric Toothbrushes?
The answer is: No, but you’d be forgiven for having believed that…
EU capitals fear Russian retaliation and cyberattacks after asset freezes
The EU’s unrelated effort to funnel cash to Ukraine from its central…
Journalists, lawyers and activists hacked with Pegasus spyware in Jordan, forensic probe finds
Israeli-made Pegasus spyware was used in Jordan to hack the cellphones of…
Tech leaders to testify on social media safety for kids
Tech leaders to testify on social media safety for kids – CBS…
Russian hacking group accessed Microsoft executive emails, company says
Microsoft Corp. said Friday a Russian hacking group illegally gained access to some…
1/17: CBS Evening News
1/17: CBS Evening News – CBS News Watch CBS News Dangerous cold…
GTA Hacker Gets Life Sentence for Stealing $10 Million Data | Entrepreneur
Arion Kurtaj’s joyride as a Grand Theft Auto (GTA) criminal appears to…
A suspected cyberattack paralyzes the majority of gas stations across Iran
TEHRAN, Iran — Nearly 70% of Iran’s gas stations went out of…
Kansas courts' computer systems are starting to come back online, 2 months after cyberattack
TOPEKA, Kan. — The court system in Kansas has started bringing its…
Inside the police force scouring the internet to save abused children
EUROPOL HEADQUARTERS, THE HAGUE — “Please knock. Do not enter,” said the…
Top White House cyber aide says recent Iran hack on water system is call to tighten cybersecurity
WASHINGTON — A top White House national security official said recent cyber…
Cybersecurity Attacks Are On the Rise — Is Your Business Prepared? | Entrepreneur
Opinions expressed by Entrepreneur contributors are their own. In the ever-evolving landscape…
Deepfakes are Lurking in 2024 — Here's How to Unmask Them | Entrepreneur
Opinions expressed by Entrepreneur contributors are their own. As artificial intelligence (AI)…
23andMe says hackers accessed 'significant number' of files about users' ancestry | TechCrunch
Genetic testing company 23andMe announced on Friday that hackers accessed around 14,000…