NEWYou can now listen to Fox News articles!
You might have noticed that in the past few months, many companies have disclosed data breaches, including Google, Dior and Allianz, and one name that appeared in most cases was Salesforce. Hackers did not breach company networks directly or exploit vulnerabilities in Salesforce’s core software. Instead, they targeted the tools and people around it by tricking employees into granting access, compromising third-party apps and abusing overly broad permissions.
Once inside, they siphoned sensitive data from Salesforce environments on an unprecedented scale. Nearly a billion records were stolen across dozens of organizations, and now cybercriminals are extorting victims by threatening to publish the data unless hefty ransoms are paid. Let’s look at the recent Salesforce incidents in detail and why this is such a big deal.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM/NEWSLETTER
JEEP AND CHRYSLER PARENT STELLANTIS CONFIRMS DATA BREACH
Hackers are weaponizing stolen Salesforce credentials to access company secrets. (REUTERS/Brendan McDermid)
Why Salesforce is the perfect target
Salesforce is not just another cloud platform. It is the backbone of how thousands of companies manage relationships with their customers. The platform powers everything from sales pipelines and marketing campaigns to support tickets and partner communications. Banks use it to track client accounts, airlines rely on it to manage frequent flyer programs, and retailers store customer purchase histories and loyalty data inside it. In many organizations, Salesforce sits at the center of daily operations, acting as a single system that touches sensitive information across departments.
That is why the scale of these breaches is so significant. A successful attack on a Salesforce instance becomes a window into a company’s customers, business strategy and internal processes. For cybercriminals, the potential payoff is enormous, and the recent incidents showed just how much damage they can cause without ever breaking into a company’s primary network.
The breaches hit companies across sectors, from Adidas and Allianz to Qantas, Google and Pandora Jewelry. Attackers often use voice-phishing calls or realistic fake apps to manipulate Salesforce administrators into installing malicious software. This allowed them to steal OAuth tokens and query data directly from CRM systems, a technique linked to groups like ShinyHunters.
Other attacks originated in compromised third-party integrations. One of the most damaging involved a chatbot tool called Drift, where stolen tokens gave attackers access to Salesforce instances at hundreds of companies.
The fallout was enormous. Coca-Cola’s European division lost more than 23 million CRM records, while Farmers Insurance and Allianz Life reported breaches affecting over a million customers each. Even Google admitted that attackers accessed a Salesforce database used for advertising leads.
TRANSUNION BECOMES LATEST VICTIM IN MAJOR WAVE OF SALESFORCE-LINKED CYBERATTACKS, 4.4M AMERICANS AFFECTED
Major brands like Google, Dior and Allianz are among those caught in the data fallout. (Kurt “CyberGuy” Knutsson)
Exploiting weak links in the ecosystem
It’s hard to break through firewalls or exploit technical vulnerabilities, but it’s much easier to manipulate people. Attackers have figured this out, and they are now focusing their efforts on human behavior and the less-protected edges of cloud ecosystems. Employees with administrative privileges were often tricked into authorizing malicious apps, while default permission settings allowed those apps to operate undetected.
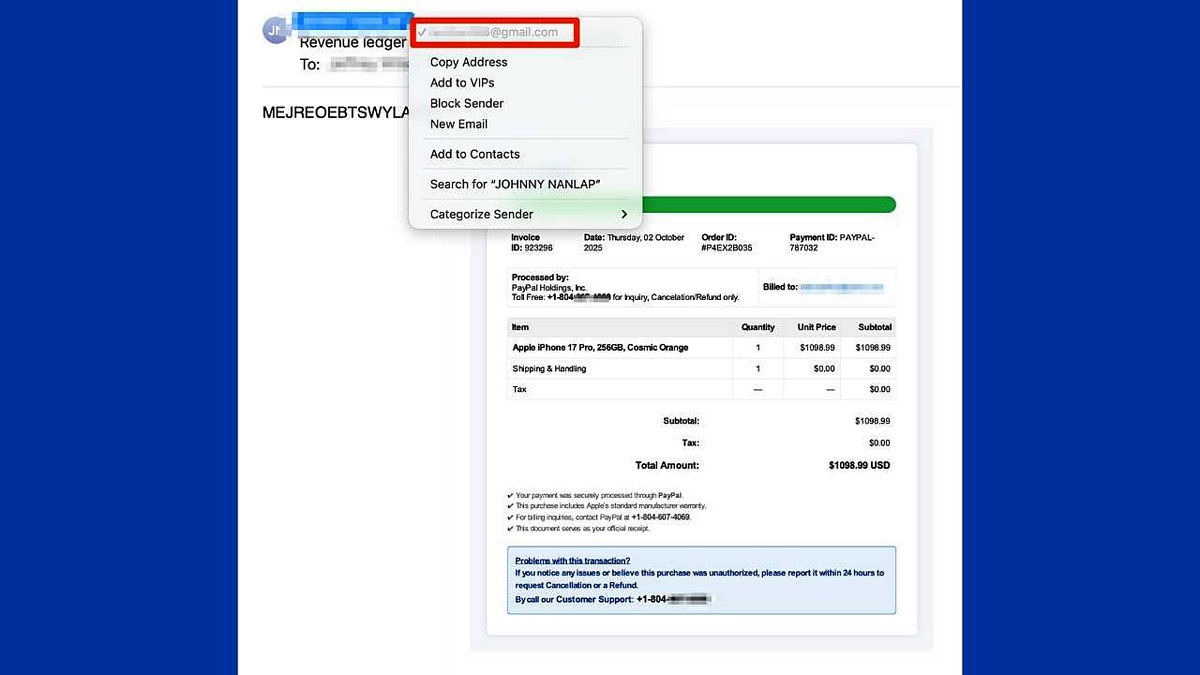
Once they obtained the data, the hackers did not simply try to sell it. They used it as leverage. Earlier this month, a loosely organized cybercrime group known by names such as Lapsus$, Scattered Spider and ShinyHunters launched a dedicated data leak site on the dark web, threatening to publish sensitive information unless victims paid a ransom.
As reported, the site is designed to pressure companies into paying to prevent their stolen data from being made public. “Contact us to regain control of your data governance and prevent public disclosure,” reads one message on the site. “Do not be the next headline. All communications require strict verification and will be handled with discretion.”
The leak site lists several alleged victims, including FedEx, Hulu (owned by Disney) and Toyota Motors. It is also unclear whether some of the organizations known to have been breached but not listed on the site have paid ransoms to keep their data from being released.
FARMERS INSURANCE DATA BREACH EXPOSES 1.1M AMERICANS
Cybercriminals are now extorting victims online, threatening to leak billions of stolen records. (Kurt “CyberGuy” Knutsson)
Salesforce’s response
Salesforce told Cyberguy that it is “aware of recent extortion attempts by threat actors” and will not engage with, negotiate with, or pay any extortion demands. A company spokesperson provided the following statement:
“We are aware of recent extortion attempts by threat actors, which we have investigated in partnership with external experts and authorities. Our findings indicate these attempts relate to past or unsubstantiated incidents, and we remain engaged with affected customers to provide support. At this time, there is no indication that the Salesforce platform has been compromised, nor is this activity related to any known vulnerability in our technology.”
6 steps you can take to protect your data
You might think a breach like this is a company problem, something for IT teams and cybersecurity experts to deal with. However, when attackers gain access to platforms like Salesforce, the data they are after is usually not the company’s. It is yours. Your contact details, purchase history, support tickets and even private conversations can end up in the wrong hands. And once that happens, the risks do not stay confined to one company. That is why it is worth taking a few proactive steps now, even if the company has not contacted you about an incident yet.
1) Lock down your accounts now
If you have interacted with any of the companies mentioned in the breach, or suspect your data might be part of it, change your passwords for those services immediately. Better yet, use a password manager to generate strong, unique passwords for every site. A good tool will also alert you if any of your credentials appear in future data leaks.
Next, see if your email has been exposed in past breaches. Our No. 1 password manager pick includes a built-in breach scanner that checks whether your email address or passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at Cyberguy.com.
2) Turn on two-factor authentication
Even if a password is stolen, two-factor authentication (2FA) adds a crucial extra layer of security. Enable it for your email, banking apps, cloud storage and any service that offers it. It is one of the simplest ways to block attackers from hijacking your accounts with stolen credentials.
3) Use a personal data removal service
Even if your data was part of a breach, you can still limit how much of it is floating around online. Personal data removal services scan and delete your personal information from data broker websites that sell or share your details without consent. These brokers often trade in names, addresses, phone numbers and even purchase histories, the same type of data leaked in Salesforce-related breaches.
By removing your records from these public databases, you make it far harder for scammers, identity thieves and marketers to find or misuse your information. Many services, like Incogni, handle the entire opt-out process automatically and keep monitoring to ensure your data stays removed.
While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com.
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com.
4) Spot and stop targeted phishing attacks
Attackers who have CRM data often know more about you than a typical scammer. They might reference past purchases, support cases, or other personal details to make their messages sound legitimate. Treat unexpected emails, texts, or phone calls with suspicion, especially if they involve links or requests for payment.
The best way to safeguard yourself from malicious links is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices at Cyberguy.com.
5) Use identity monitoring tools
Data breaches do not always result in immediate damage. Sometimes, criminals sit on stolen data for months before using it. These services can continuously monitor the dark web for your personal information and notify you if your data appears in new leaks. That gives you time to act before problems snowball.
Identity Theft companies can monitor personal information like your Social Security number (SSN), phone number and email address, and alert you if it is being sold on the dark web or being used to open an account. They can also assist you in freezing your bank and credit card accounts to prevent further unauthorized use by criminals.
See my tips and best picks on how to protect yourself from identity theft at Cyberguy.com.
6) Know your rights
If you think your data was exposed, companies are legally obligated in most regions to inform you. Do not hesitate to contact them directly and ask for details on what was stolen and what steps they are taking to protect affected customers. The more pressure users apply, the more likely companies are to tighten security practices.
CLICK HERE TO GET THE FOX NEWS APP
Kurt’s key takeaway
Attackers can expose your personal data even if you are careful. They gain access to corporate cloud environments and can see customer names, emails, purchase histories and other sensitive details. For users, this means it is crucial to stay vigilant. Criminal groups use this stolen information to launch targeted phishing attacks, open fake accounts, or impersonate you elsewhere. Some even cross-reference leaked Salesforce data with information from previous breaches to build disturbingly complete profiles of their victims.
Should companies face stricter penalties when sensitive customer data is stolen? Let us know by writing to us at Cyberguy.com.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt “CyberGuy” Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on “FOX & Friends.” Got a tech question? Get Kurt’s free CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.