NEWYou can now listen to Fox News articles!
YouTube is arguably the most popular and most visited platform for entertainment, education and tutorials. There’s a video for everything on YouTube, whether you want to learn how to cook, ride a bike or need help with work or school. But recent research by Check Point reveals a darker side: a sprawling malware distribution network quietly operating within the platform. Hackers are using compromised accounts, fake engagement and clever social engineering to spread information-stealing malware disguised in more than 3,000 software cracks and game hack videos.
Most victims begin by searching for free or cracked software, cheat tools or game hacks, which is the root of the infection chain. This curiosity for “free” software opens the door to the Ghost Network’s traps.
META ACCOUNT SUSPENSION SCAM HIDES FILEFIX MALWARE
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts, and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CyberGuy.com newsletter.
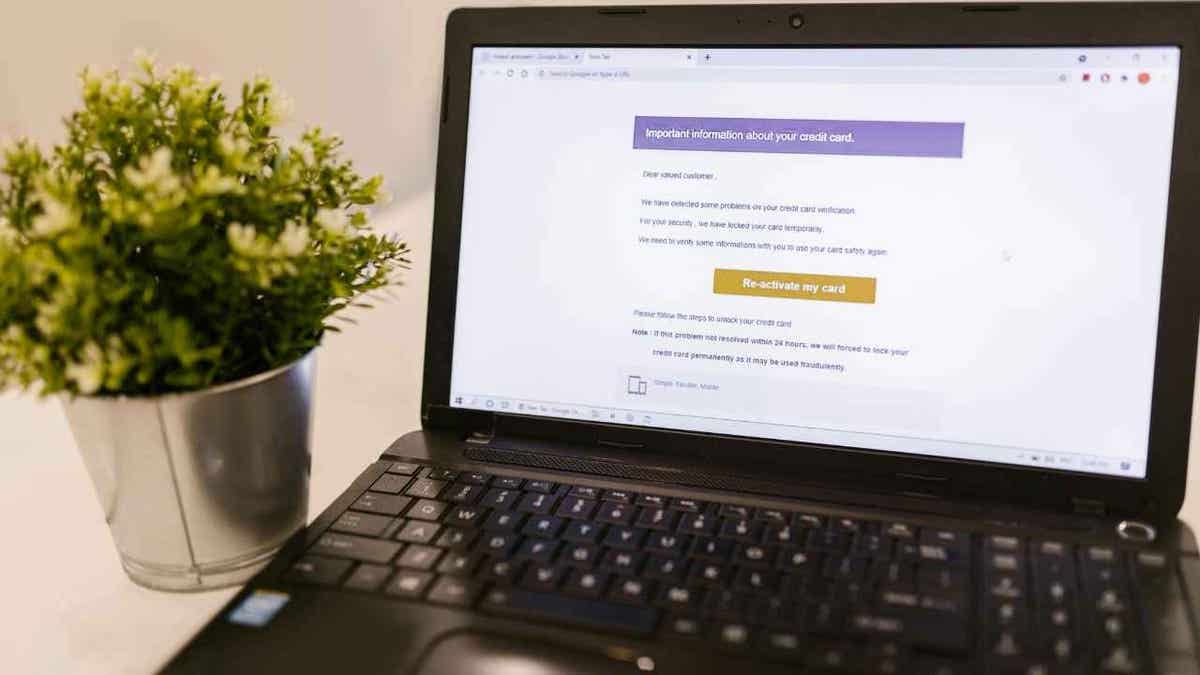
Cybercriminals are exploiting YouTube’s massive reach by disguising malware inside fake “how-to” and “free software” videos. (Kurt “CyberGuy” Knutsson)
All about YouTube’s ghost network
According to Check Point Research, the YouTube Ghost Network has been active since 2021, with activity surging threefold in 2025. It’s built around a simple but effective formula, which blends social manipulation with technical stealth. The network’s primary targets are people searching for “Game Hacks/Cheats” and “Software Cracks/Piracy.”
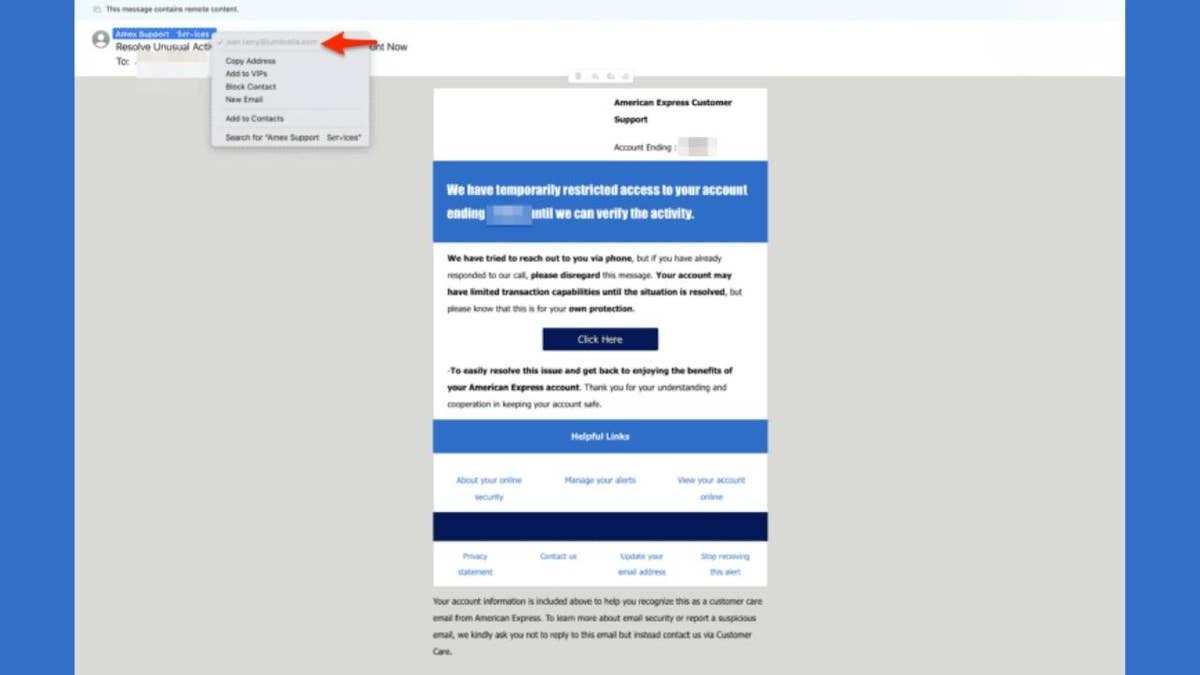
Researchers discovered that these videos often feature positive comments, likes and community posts from compromised or fake accounts. This coordinated engagement gives potential victims a false sense of safety.
The fake social proof and fabricated likes, comments and subscriber activity play a key psychological role. They trick viewers into believing the content is legitimate and widely trusted, allowing the operation to persist even when YouTube removes individual videos or channels. The network’s modular structure and constant replacement of banned accounts make takedowns only temporarily effective.
Once a user clicks the provided links, they’re usually taken to file-sharing services or phishing sites hosted on Google Sites, MediaFire, Dropbox or similar platforms. The linked files are often password-protected archives, making them harder for antivirus tools to scan. Victims are then asked to disable Windows Defender before installation, effectively disarming their own protection before running the malware.
Check Point found that the majority of these attacks deliver information-stealing malware such as Lumma Stealer, Rhadamanthys, StealC and RedLine. These programs harvest passwords, browser data and other sensitive information, sending it back to the attacker’s command and control servers.
What makes the network particularly resilient is its role-based structure. Each compromised YouTube account serves a function; some upload malicious videos, others post download links and a third group boosts credibility by commenting and liking content. When an account gets banned, it’s quickly replaced, allowing the operation to continue largely uninterrupted.
A single click on a malicious link can disable your defenses and install information-stealing malware in seconds. (Kurt “CyberGuy” Knutsson)
Inside the malicious campaigns
Two major campaigns stood out in Check Point’s investigation. The first involved the Rhadamanthys infostealer, spread through a compromised YouTube channel named @Sound_Writer, which had nearly 10,000 subscribers.
The attackers uploaded fake cryptocurrency-related videos and used phishing pages on Google Sites to distribute malicious archives. These pages instructed viewers to “turn off Windows Defender temporarily,” assuring them it was a false alert. The archives contained executable files that quietly installed the Rhadamanthys malware, which connected to multiple control servers to exfiltrate stolen data.
The second campaign, involving HijackLoader and Rhadamanthys, leveraged a much larger channel, @Afonesio1, with around 129,000 subscribers. Here, attackers uploaded videos offering cracked versions of Adobe Photoshop, Premiere Pro, and FL Studio.
MICROSOFT SOUNDS ALARM AS HACKERS TURN TEAMS PLATFORM INTO ‘REAL-WORLD DANGERS’ FOR USERS
One of these videos gained over 291,000 views and dozens of glowing comments claiming the software worked perfectly. The malware was hidden inside a password-protected archive linked through a community post. The installer used HijackLoader to drop the Rhadamanthys payload, which then connected to rotating control servers every few days to avoid detection.
Even if you never complete the installation, you can still be at risk. Simply visiting the phishing or file-hosting sites may expose you to malicious scripts or credential theft prompts disguised as “verification” steps. Clicking the wrong link can compromise login data before any software is even installed.
Strong passwords, two-factor authentication, and regular security scans are your best defense against YouTube’s Ghost Network. (Cyberguy.com)
7 steps you can take to stay safe from YouTube’s ghost network
The Ghost Network succeeds by exploiting curiosity and trust. It disguises malware as “free software” or “game hacks,” relying on users to click before thinking. Protecting yourself means adopting habits that make it harder for attackers to fool you. Here are seven steps to stay safe:
1) Avoid cracked software and cheat downloads
Most infections start with people trying to download pirated or modified programs. These files are often hosted on unregulated file-sharing websites where anyone can upload malicious content. Even if a YouTube video looks polished or filled with positive comments, that doesn’t mean it’s safe. Official software developers and gaming studios never distribute downloads through YouTube links or third-party sites.
Besides being dangerous, downloading cracked software also poses legal risks. Piracy violates copyright law and can lead to serious consequences, while giving cybercriminals a perfect delivery channel for malware.
2) Use a strong antivirus
Make sure you have a trusted antivirus solution installed and always running. Real-time protection can detect suspicious downloads and block harmful files before they do any damage. Schedule regular system scans and keep your antivirus updated so it can recognize the latest threats.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android & iOS devices at Cyberguy.com
WHAT REALLY HAPPENS ON THE DARK WEB, AND HOW TO STAY SAFE
3) Never disable your antivirus or Windows Defender
If a tutorial or installer tells you to disable your security software, that’s a red flag. Malware creators use this trick to bypass detection. There’s no legitimate reason to turn off protection, even temporarily. The moment a file asks you to do so, delete it immediately.
4) Be cautious with YouTube links and download sources
Always inspect links before clicking. Hover over them to check the destination and avoid shortened or redirected URLs that hide their true target. Downloads hosted on unfamiliar domains or file-sharing sites should be treated as unsafe. If you need software, get it directly from the official website or trusted open-source communities.
5) Use a password manager and enable two-factor authentication (2FA)
Turning on 2FA for important accounts adds another layer of protection, ensuring that even if someone gets your password, they can’t access your account. Malware often aims to steal saved passwords and browser data. Storing credentials in a password manager keeps them encrypted and separate from your browser, making them harder to steal. Consider using a password manager, which securely stores and generates complex passwords, reducing the risk of password reuse.
Next, see if your email has been exposed in past breaches. Our #1 password manager (see CyberGuy.com) pick includes a built-in breach scanner that checks whether your email address or passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at CyberGuy.com
6) Keep your operating system and apps updated
Software updates don’t just bring new features, but they also fix security flaws that malware can exploit. Enable automatic updates for your system, browser, and commonly used applications. Staying up to date is one of the simplest ways to prevent infections.
7) Use a trusted data removal service
Even after securing your system, your personal information might already be circulating online from past breaches. A reliable data removal service can continuously scan and request deletion of your data from people-search and broker sites, making it harder for cybercriminals to exploit your exposed information.
While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting CyberGuy.com
Get a free scan to find out if your personal information is already out on the web: CyberGuy.com
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
Kurt’s key takeaway
Cybercriminals have evolved beyond traditional phishing and email scams. By exploiting a platform built on trust and engagement, they have created a scalable, self-sustaining system for malware distribution. Frequent file updates, password-protected payloads, and shifting control servers make these campaigns difficult for both YouTube and security vendors to detect and shut down.
Do you think YouTube is doing enough to stop malware distribution on its platform? Let us know by writing to us at CyberGuy.com
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts, and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CyberGuy.com newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt “CyberGuy” Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on “FOX & Friends.” Got a tech question? Get Kurt’s free CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.