NEWYou can now listen to Fox News articles!
The holiday season is the happiest and riskiest time of year to be online. As millions of us gear up for Black Friday and Cyber Monday deals, scammers do the same.
Every year, they target holiday shoppers with fake websites, “too-good-to-be-true” deals and scam emails that look identical to legitimate retailers. But here’s the part most people miss: scammers don’t just rely on luck. They already have your personal data before you even click “add to cart.”
From leaked email addresses to exposed phone numbers and home addresses, your personal information is being bought and sold by data brokers, companies that collect and resell detailed profiles about you. Those profiles are exactly what scammers use to send realistic “order confirmations,” fake delivery alerts and “urgent payment” texts during this holiday period and beyond.
Let’s unpack how this works and what you can do now to stay safe before the holiday chaos begins.
RETIREES LOSE MILLIONS TO FAKE HOLIDAY CHARITIES AS SCAMMERS EXPLOIT SEASONAL GENEROSITY
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM newsletter.
Scammers ramp up fake websites and emails during the holiday shopping rush. (iStock)
Why scammers love the holiday season
November through December is a goldmine for cybercriminals. According to the CISA, reports of online shopping scams spike during this time of year and vary in their approaches. The reason? We let our guard down when we’re rushed, distracted or excited by a deal. Staying alert during the holiday season can help you avoid data exposure and financial losses. Here are some of the most common scams you should be aware of.
Phantom stores
The surge of promotions during the holiday season is the perfect time for “phantom stores” to thrive. It’s a fraudulent store that mimics the interface and products of a well-known brand. Once you purchase from such a website, you’ll never receive your order as the store doesn’t actually exist.
Real-world example: Fake IKEA websites appeared with URLs spelled “ikeaa-sale.com” and “ikea-blackfriday.shop,” mimicking the official ikea.com interface with copied product images, logos and discount banners.
They lured shoppers with huge discounts and clearance offers to steal credit card data. Eventually, they were reported and taken down, but the damage has been done.
What to do? Always check the URL of the store you shop at and only click links from the store’s official website or social media.
Delivery scams
According to recent research, some of the most popular shopping apps like Temu are selling your location data to third parties. It’s no surprise that you might receive fake delivery texts.
Your leaked data fuels realistic “order” and “delivery” scams online. (iStock)
MAJOR COMPANIES, INCLUDING GOOGLE AND DIOR, HIT BY MASSIVE SALESFORCE DATA BREACH
Real-world example: Temu is a popular app for scammers to mimic. They can easily find your contact information and order details to text “Your order couldn’t be delivered.” Each text contains a phishing link that can install malware on your device or steal your personal information. That’s why Temu warns its users about the couriers they partner with.
What to do? Make sure the texts you receive come from a legit courier service and double-check it on the store’s website.
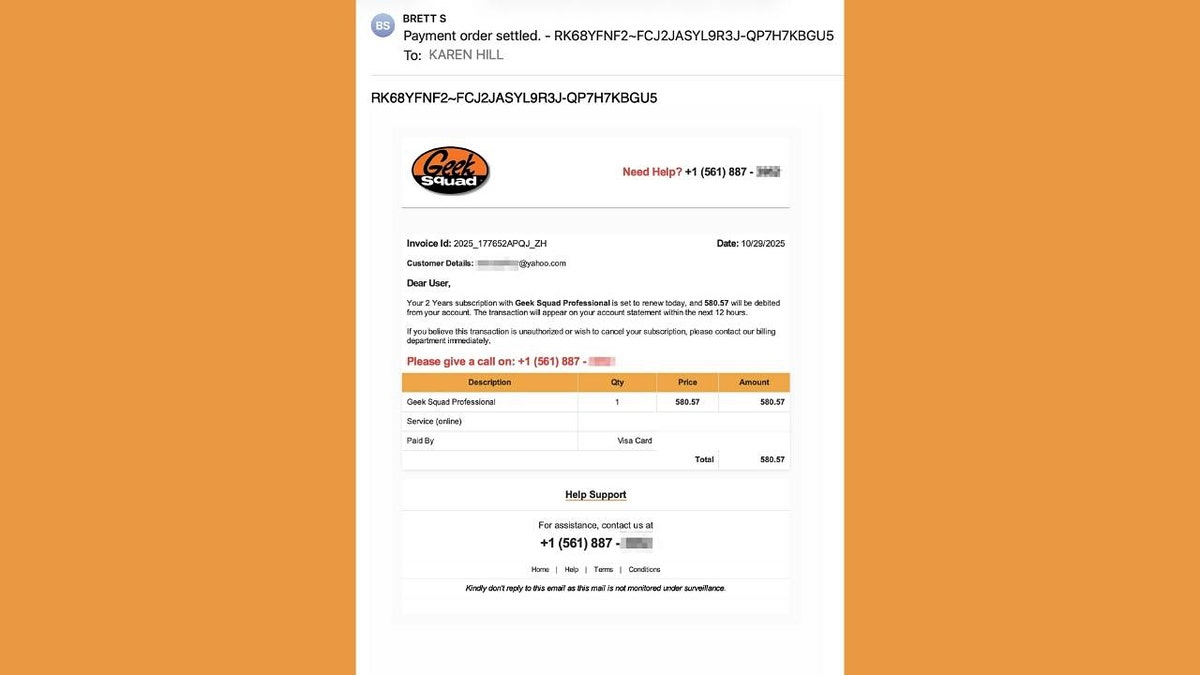
Fake order emails
Some scammers use sophisticated phishing tactics to lure victims. They engineer emails from well-known brands, use an urgent tone, place malicious links and urge you to click on your order status. In reality, there is no order status – they’re stealing your data.
Real-world example: Amazon is one of the biggest online retailers worldwide, and that makes the brand easy to mimic. Scammers send emails on behalf of Amazon to try to steal customers’ personal data because it’s highly likely that their victims have used Amazon, making it less suspicious. However, phishing emails have some telltale signs you can look out for.
What to do? Never click on any suspicious links and always check the sender’s contact information.
Unwanted data exposure
When you shop online, you should be aware of the data you share, including your contact information, shopping habits, credit card details and more. All stores collect some type of data about you. However, some companies collect more than you think.
Real-world example: The infamous Target controversy in 2012 revealed how big retailers use data analysis to predict your shopping behavior. The company collected shopping data and managed to produce a predictive model for soon-to-be mothers.
They sent out brochures with baby clothes, vouchers for baby formula and more before the customers even knew they were pregnant. Thankfully, modern shopping looks a bit different. You can opt out of certain data collection and exercise your right to remove personal information from websites that collect it.
What to do? Check what data the stores collect about you and request the removal of any private information you don’t want them to have.
THE TRUTH BEHIND THOSE MYSTERIOUS SHIPMENT EMAILS IN YOUR INBOX
How scammers find you
Imagine you’re browsing for gifts online. Within minutes, your activity generates data points – device info, IP address, browsing habits that feed into online databases. At the same time, data brokers already have your full profile: age, income, address history, family members and even shopping behavior. These profiles are sold to marketers and often leak into criminal databases.
That’s why scam calls, texts and emails often feel so “real.” They use your name, the right retailer, even your city. They’re not guessing. They’ve bought your digital footprint.
The “holiday cleanup” your data needs
Most people clear their browser cookies or delete old emails to “stay private.” But that’s like locking your front door while leaving all your personal documents on the lawn.
If you want to stop scammers from targeting you this holiday season, you need to remove your personal data from the source, the data broker databases that feed these scams.
That’s where a data removal service comes in. While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com.
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com.
Practical steps before you shop
To make sure your online shopping season stays stress-free and scam-free, here’s what CyberGuy recommends doing this week:
INSIDE A SCAMMER’S DAY AND HOW THEY TARGET YOU
1) Run a privacy scan with a data removal service
Before the holiday rush, remove your exposed data from data brokers. You’ll reduce the number of scam calls, emails and texts you get this season and protect your financial info before it’s too late.
Take control by removing personal data from broker databases before you shop. (iStock)
2) Secure your email
Use strong, unique passwords for each online store or service. Consider a password manager to simplify this.
Next, see if your email has been exposed in past breaches. Our No. 1 password manager pick includes a built-in breach scanner that checks whether your email address or passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at Cyberguy.com.
3) Check for fake stores
Before clicking a social media ad or email, hover over the link. Legit retailers use secure “https://” URLs and their exact brand name – no extra words or letters.
4) Avoid public Wi-Fi
Don’t shop or enter payment info over public Wi-Fi in an airport, café or mall, for example. Scammers can easily intercept unencrypted traffic.
5) Use credit cards or PayPal – not debit cards
HACKERS TARGET ONLINE STORES WITH NEW ATTACK
Credit cards have stronger fraud protection and make it easier to dispute unauthorized charges.
6) Enable two-factor authentication (2FA)
Turn on 2FA for your email, bank and shopping accounts. Even if scammers get your password, they can’t log in without your second verification step.
7) Keep your software and apps updated
Cybercriminals often exploit outdated browsers or apps. Update your phone, computer and shopping apps before the holiday rush to close those security holes.
8) Monitor your bank and credit statements
Check your accounts daily during the shopping season. The faster you spot a suspicious charge, the easier it is to reverse and protect your funds.
Kurt’s key takeaways
Black Friday through Cyber Monday is the peak time for data harvesting. Every purchase, coupon code and sign-up adds to the profile that marketers and data brokers hold on you. That information can linger online for years, long after the sales end. The good news? It’s easier than ever to reclaim your privacy. By taking just a few minutes today, you can enjoy the holidays knowing your personal data is no longer on the open market.
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
How confident are you that your personal data isn’t already fueling a scam this holiday season? Let us know by writing to us at Cyberguy.com.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt “CyberGuy” Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on “FOX & Friends.” Got a tech question? Get Kurt’s free CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.