NEWYou can now listen to Fox News articles!
Apple’s big annual event on Tuesday delivered a polished and tightly produced showcase. The company’s CEO, Tim Cook, led the presentation with sweeping visuals, confident pacing and a clear message: Apple is still betting big on premium innovation. But the real headline wasn’t so much the tech; it was the prices.
Earlier this year, President Donald Trump granted Apple a tariff break. Still, the company raised prices across its iPhone lineup. The new ultra-thin iPhone 17 Air, which Apple positioned as a reinvention of last year’s iPhone 16 Plus, jumps to $999. The iPhone 17 Pro begins at $1,099, while the Pro Max tops out at $1,199. The entry-level iPhone 17 starts at $799.
Apple positioned the price hikes as a reflection of breakthrough innovation. The company spotlighted the iPhone Air’s sleek redesign, the powerful A19 chip and major camera upgrades. Yet the takeaway was clear: tariff relief didn’t lead to consumer savings. Instead, Apple leaned into its premium identity, signaling that cutting-edge tech now comes with a steeper price tag.
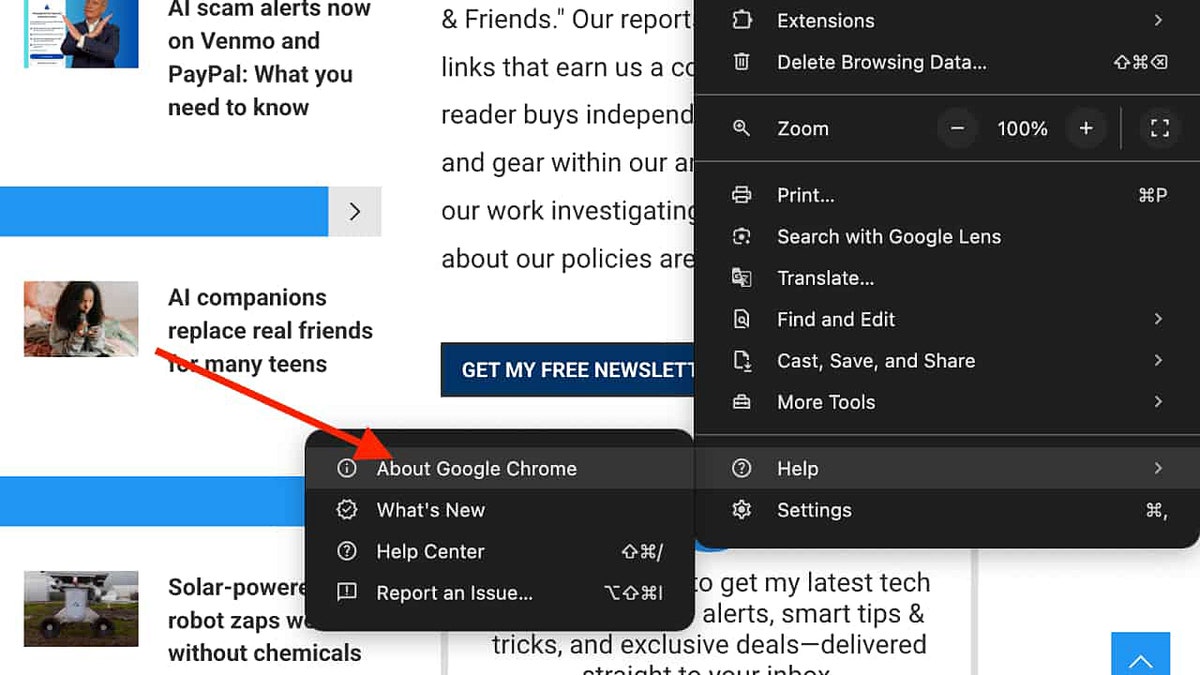
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
GOOGLE PIXEL 10 EVENT BRINGS NEW PHONES, SMARTWATCH, EARBUDS AND AI
Apple CEO Tim Cook holds an iPhone 17 Pro and an iPhone Air, on its campus in Cupertino, California, Sept. 9, 2025. (REUTERS/Manuel Orbegozo)
iPhone 17 Air: the thinnest iPhone ever
Apple unveiled the iPhone 17 Air, its slimmest model yet at 5.6mm and 165 grams, built with recycled aluminum, glass and titanium. (Apple)
Apple calls the iPhone 17 Air a game-changer. At just 5.6mm thin and weighing around 165 grams, it stands as the slimmest iPhone the company has ever made. The design uses recycled aluminum, glass and titanium to reduce weight while staying durable. Engineers reinforced the frame and applied new drop-test algorithms to make sure it holds up in daily use.
The Air debuts silicon anode battery technology, which allows Apple to shrink the device without cutting power. During the presentation, Apple promised “all-day battery life,” but never gave an exact hour count. That vague description raised questions. Moments later, Apple introduced a new low-profile MagSafe battery accessory. When paired with the iPhone 17 Air, Apple says the combo delivers up to 40 hours of video playback. The timing of that announcement made it clear that battery life could still be a concern.
Apple also pushed the Air forward with a new ultra-wide 48MP fusion camera system, which uses advanced image processing to improve detail and low-light performance. The display gained a ProMotion 120Hz refresh rate that makes scrolling and animations feel smoother. Outdoor use should also improve, thanks to 3,000 nits of peak brightness, making it easier to see in direct sunlight. On the durability side, the Air features Ceramic Shield 2 coating, which Apple claims resists scratches and accidental drops better than before.
The iPhone 17 Air starts at $999 with 256GB of storage. That price is $100 higher than last year’s thinnest model, marking another step up in Apple’s pricing strategy.
iPhone 17 Pro: design and performance overhaul
The iPhone 17 Pro starts at $1,099 and comes with 256GB of base storage. (Apple)
The iPhone 17 Pro introduces a striking unibody design that relies on laser-welded vapor chamber cooling to keep performance steady even under heavy use. Apple gave the back a ceramic shield finish, while the front now features its upgraded seven-layer coating. That change reduces glare both indoors and outdoors, making the display easier on the eyes in all conditions.
At the core of the Pro sits the new A19 Bionic chip built on 3nm architecture. Apple paired it with a 16-core Neural Engine and an updated display engine to push speed and efficiency even further. The company claims this is the most power-efficient iPhone yet and promises the longest battery life ever offered in a Pro model.
Apple also turned its attention to the camera system. The Pro camera lineup includes a 48MP main sensor and a 12MP ultra-wide, with ProRes support for high-quality video recording. It even offers Genlock syncing, which professionals can use to line up multiple cameras in studio and live production setups.
To complement the new design, Apple introduced TechWoven cases that feel more like premium accessories than traditional covers. Some versions include optional cross-body straps, a nod to the growing trend of blending technology with fashion.
Apple also revealed three new finishes for the Pro models: deep blue, cosmic orange and silver, adding a fresh look to the lineup.
The iPhone 17 Pro comes with 256GB of base storage and starts at $1,099, keeping its place as Apple’s most balanced high-end option between the Air and the Max.
WWDC 2025: IOS 26, LIQUID GLASS DESIGN AND APPLE’S AI SHORTFALL
iPhone 17 Pro Max: bigger, brighter, more expensive
Apple unveiled the iPhone 17 Pro Max as its top model, featuring the biggest display ever on an iPhone. (Apple)
Apple positioned the iPhone 17 Pro Max as the ultimate model in the lineup. It shares the same unibody design, ceramic shield finish and seven-layer front coating as the Pro, but it stretches everything to a larger scale. The Pro Max delivers the biggest display Apple has ever put on an iPhone, paired with enhanced brightness that makes it more usable outdoors and in direct sunlight.
Inside, it runs on the same A19 Bionic chip with the 16-core Neural Engine, so performance and efficiency mirror the Pro. What sets the Max apart is its endurance. Apple claims it offers the best battery life of any iPhone to date, making it the go-to choice for people who rely heavily on their phone throughout the day.
The Pro Max also carries the full Pro camera system, including the 48MP main sensor and advanced video features like ProRes and Genlock. With its extra size, it appeals most to creators, gamers and anyone who wants the biggest screen possible in an iPhone.
Like the Pro, the Max is available in deep blue, cosmic orange and silver finishes.
Pricing starts at $1,199 with 256GB of storage, marking the highest entry point yet for an iPhone and reinforcing Apple’s steady climb in premium pricing.
iPhone 17: Apple’s new starting point
iPhone 17 starts at $799 with 256GB of storage. (Apple)
The standard iPhone 17 rounds out the lineup and now serves as Apple’s new baseline model. It starts at $799 with 256GB of storage.
The iPhone 17 inherits many of the Pro’s features. It comes in five colors and has a thinner profile that feels more refined in hand. The display includes the upgraded coating to cut glare, and the front camera has a square AI-driven sensor with Center Stage for better video calls.
The main camera system also makes a leap forward. The iPhone 17 now carries a 48MP main sensor, supported by Apple’s fusion technology to improve clarity and low-light results. Combined with the updated display engine and improved durability from Ceramic Shield 2, the iPhone 17 delivers a more polished experience than previous entry models.
Beyond iPhones: Apple’s big updates for AirPods and Watch
Apple didn’t stop with iPhones. The company used its event to refresh its wearables and audio lineup, bringing new features to AirPods and multiple Apple Watch models. Each product builds on familiar designs while adding functions aimed at health, fitness and convenience.
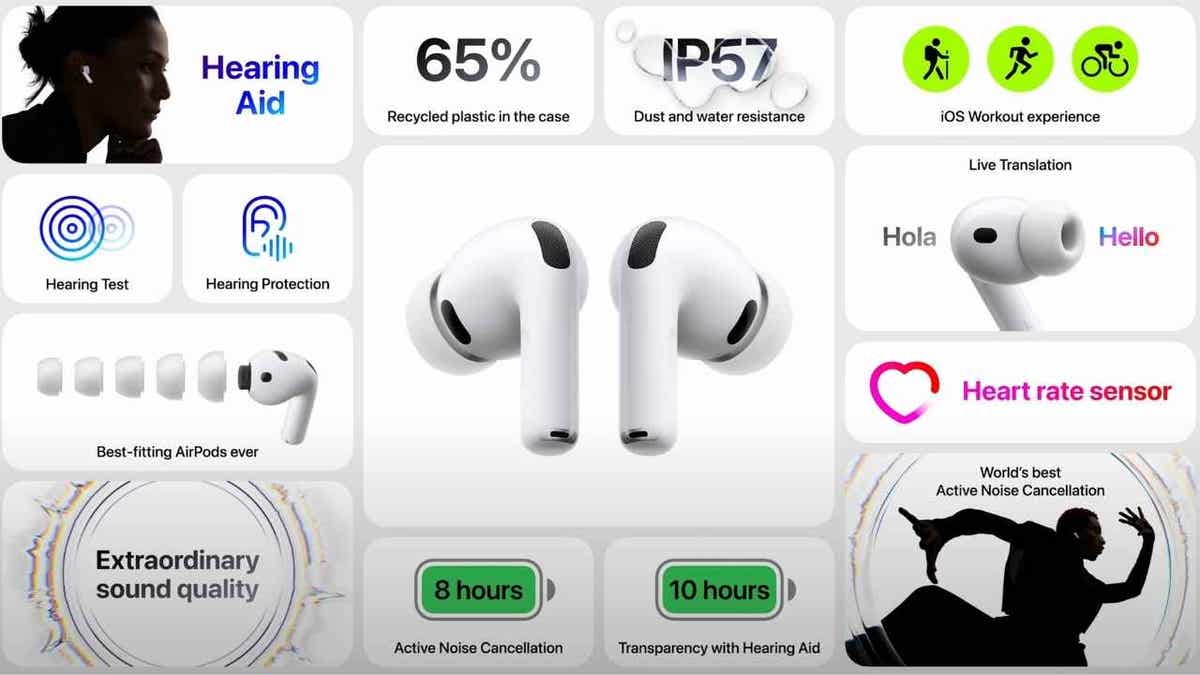
AirPods Pro 3: smarter sound and live translation
The new AirPods Pro 3 deliver up to eight hours of listening time on a single charge. (Apple)
Apple unveiled the third-generation AirPods Pro, priced at $249, and available starting Sept. 19. The design keeps the iconic stem but introduces foam-infused ear tips that come in five sizes. Apple said it studied 100,000 ear shapes to make them fit more securely.
The new AirPods Pro 3 extend listening time, offering up to eight hours on a single charge, compared with six hours in the previous generation. With the charging case, total listening time stretches to 10 hours with hearing-AI features enabled.
One of the standout additions is heart rate sensing, which turns the AirPods into another health-tracking accessory in Apple’s ecosystem. The earbuds also use AI-driven hearing enhancements to improve clarity in noisy environments. Apple said the AirPods Pro 3 now deliver up to four times stronger active noise cancellation (ANC) than the originals, making them far more effective in crowded or loud spaces.
For workouts, users can also track over 50 activity types with the Fitness app on iPhone while wearing them. Perhaps most notably, Apple added live translation. When two people wear AirPods Pro 3 paired with iPhones, conversations can be translated in real time, breaking language barriers in a way that once seemed impossible.
Apple Watch Series 11: health at the forefront
Apple Watch Series 11 expands the company’s push into advanced health technology. (Apple)
The Apple Watch Series 11 continues Apple’s push into health technology. It runs on watchOS 26 and introduces monitoring for possible hypertension and sleep apnea, with alerts designed to prompt users to seek medical care. Apple noted that FDA clearance is still pending for hypertension notifications, but the company clearly sees the watch as a serious medical tool.
The watch also includes Sleep Score, which breaks down sleep stages such as core, deep and awake to give users a clearer picture of rest quality. Battery life reaches up to 24 hours, and the watch remains efficient even with 5G connectivity.
Apple built the Series 11 with 100% recycled aluminum and titanium cases, expanding its sustainability pledge. Color options bring a refreshed look, while pricing starts around $399, depending on configuration.
APPLE WINS BLOOD OXYGEN BATTLE FOR WATCH OWNERS
Apple Watch SE 3: affordable and fast
Apple Watch SE 3 remains the lowest-priced entry into the lineup at $249. (Apple)
Apple also refreshed its budget-friendly model, the Apple Watch SE 3. At $249, it remains the lowest-priced entry into the lineup. The SE 3 uses the new S10 chip, giving it faster performance and support for Apple’s expanding gesture controls.
It also delivers sleep apnea notifications, a feature previously limited to more expensive models. Charging is now up to two times faster, ensuring the watch is ready to go with less downtime. Apple added more health and convenience tools, including wrist temperature sensing for deeper insights in the Vitals app, retrospective ovulation estimates and an Always-On display. It also supports double-tap and wrist flick gestures, plus on-device Siri. Available in two colors, the SE 3 carries forward Apple’s strategy of making core health features more accessible.
Apple Watch Ultra 3: the powerhouse upgrade
Apple Watch Ultra 3 debuts with the largest and brightest display ever on a Watch. (Apple)
At the top end, Apple introduced the Apple Watch Ultra 3, starting at $799 and shipping September 19. This model pushes the limits of durability and outdoor performance. The Ultra 3 features the largest and brightest display ever put on an Apple Watch, making it easier to read data during workouts or in direct sunlight.
It includes a redesigned radio and antenna system capable of connecting with satellites orbiting 800 miles above Earth. That means users can send messages or use Find My features even without cell service, making it a true companion for extreme adventures.
The Ultra 3 packs a larger battery that runs up to 42 hours on a single charge. With Low Power Mode enabled, Apple says the battery can extend to as much as 72 hours, making it the longest-lasting Apple Watch to date. It also introduces new Workout Buddy tools for training and enhanced hypertension notifications, further pushing Apple’s reputation in health tech. Available in black or natural titanium, the Ultra 3 blends rugged design with cutting-edge features.
iPhone 17 accessories: small add-ons with big impact
Apple showcased new accessories for its iPhones, including a low-profile MagSafe battery pack. (Apple)
Apple used the event to highlight a series of accessories that show how the company expects people to use its new iPhones. The most talked about was the low-profile MagSafe battery pack, created to address the iPhone 17 Air’s biggest weakness: vague “all-day” battery claims. When attached, the Air can stretch to 40 hours of video playback, turning what could have been a limitation into a selling point for Apple’s ecosystem.
To complement the Air’s slim profile, Apple also revealed a new translucent case and a lightweight bumper. The translucent case keeps the 5.6mm design visible while still protecting it, while the bumper adds shock resistance around the edges without adding bulk. Both aim to reassure buyers who worry that the thinnest iPhone yet might be more fragile.
For the Pro and Pro Max models, Apple introduced TechWoven cases made from a durable fabric blend. What stood out was the addition of an optional cross-body strap, giving users a hands-free way to carry their phones. Apple leaned into the idea of the iPhone as not just a device but also a lifestyle accessory that blends technology with personal style.
Together, the MagSafe battery, translucent Air case, protective bumper and fashion-forward TechWoven cases with cross-body straps showed Apple’s strategy clearly. Accessories are no longer secondary; they are central to how Apple expects customers to protect, power and personalize their iPhones.
CLICK HERE TO GET THE FOX NEWS APP
Kurt’s key takeaways
Apple’s iPhone 17 lineup pushes innovation forward with a blend of sleek design and powerful features. The iPhone 17 Air impresses with its ultra-thin profile and new battery technology. Meanwhile, the Pro and Pro Max models deliver unmatched performance and durability for demanding users. Additionally, Apple enhances its ecosystem with upgraded AirPods and Apple Watch models that emphasize health and convenience. Overall, Apple continues to balance style, functionality and user experience, setting a strong foundation for the year ahead.
Which Apple device are you most excited to buy, and why?
Kurt “CyberGuy” Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on “FOX & Friends.” Got a tech question? Get Kurt’s free CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.