[ad_1]
NEWYou can now listen to Fox News articles!
Scammers are constantly finding new ways to trick people. While older tactics like phishing emails and impersonating government agencies to steal credentials are becoming easier to spot, bad actors are now turning to more alarming methods. One of the latest involves impersonating local authorities.
People have reported receiving phone calls claiming they missed jury duty and now face a warrant for their arrest. This kind of impersonation scam is harder to spot because it’s highly personalized, but that doesn’t mean you’re defenseless. Let’s break it down.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
DON’T FALL FOR THIS BANK PHISHING SCAM TRICK
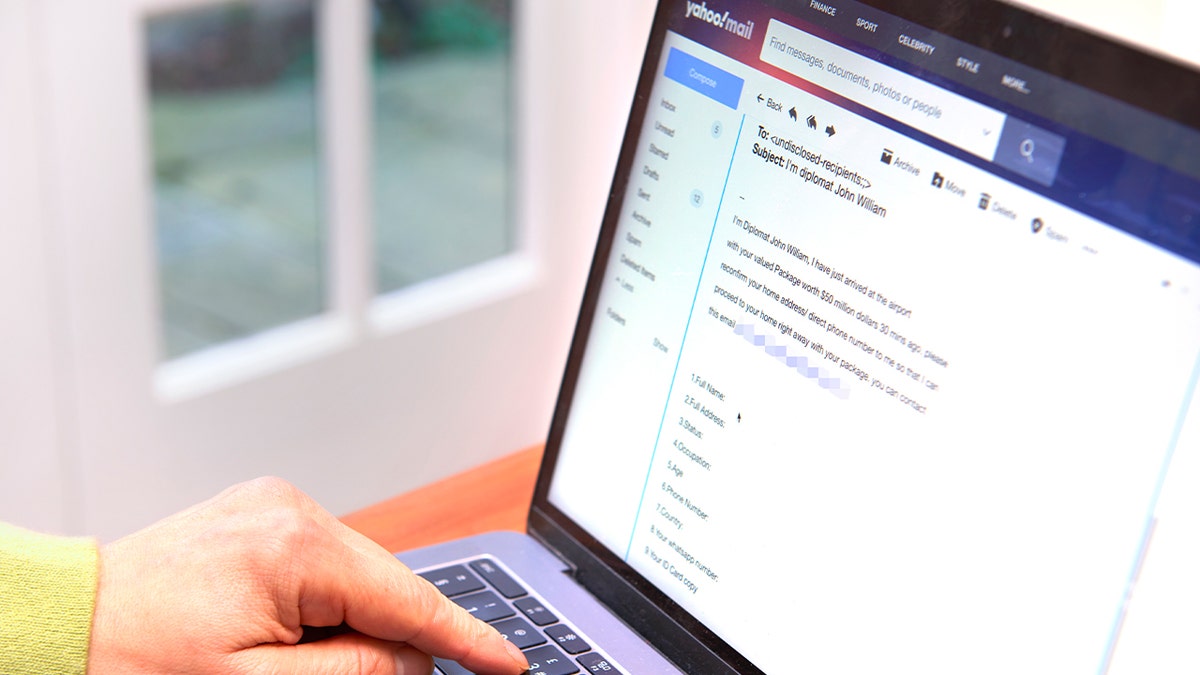
Scammers impersonating local authorities are on the rise, telling victims they missed jury duty and must pay to avoid legal trouble. (Kurt “CyberGuy” Knutsson)
What jury duty scam victims need to know
Scammers posing as court officials are targeting individuals with false claims about missed jury duty, prompting warnings from law enforcement. The fraud typically begins with a call from a blocked or unknown number, alleging that the recipient has missed jury duty and is facing an arrest warrant. The scammers then demand payment, usually through wire transfers or gift cards.
A key warning sign is being asked to pay money to avoid arrest or legal trouble. It is important never to give money or personal information to unknown callers.
These scams often target older or more vulnerable individuals, although younger people have also reported close calls. In one example, a person received repeated calls from an unidentified number before answering. The caller, claiming to be from a local sheriff’s department and equipped with the individual’s full name and address, insisted they had failed to appear for jury duty and faced multiple citations.
HOW FAKE MICROSOFT ALERTS TRICK YOU INTO PHISHING SCAMS

Victims can spot jury duty impersonation scams by verifying suspicious calls before taking action and reducing their digital footprint. (Kurt “CyberGuy” Knutsson)
How to spot jury duty impersonation scams
- No jury duty arrest warrants: Missing jury duty doesn’t lead to criminal citations or warrants.
- Blocked or spoofed numbers: Real law enforcement won’t hide their identity.
- Unusual payment methods: No government agency will ask for gift cards or crypto.
- Aggressive threats: Threats of arrest or contempt of court are a scare tactic.
Legitimate jury summonses are delivered by mail, not through threatening phone calls.
6 ways to protect yourself from jury duty scam calls
If you get a suspicious call about missed jury duty, don’t panic. Follow these steps to stay safe and protect your personal information.
1) Don’t trust calls from unknown numbers
This might sound obvious, but don’t trust any unknown caller, especially if they demand money. Legitimate authorities will never ask for payment over the phone, especially not through gift cards, wire transfers, or cryptocurrency. If someone threatens you with arrest or legal action unless you pay immediately, it’s almost certainly a scam. Hang up and call your local court or police department using an official number.
HOW TO HAND OFF DATA PRIVACY RESPONSIBILITIES FOR OLDER ADULTS TO A TRUSTED LOVED ONE
2) Verify suspicious calls before taking action
If you receive a suspicious call, take a breath and fact-check. Court summonses are always delivered by mail, not over the phone. Even if the caller has personal information like your name or address, that doesn’t make them credible. Scammers often use leaked or publicly available data to appear convincing.
Be extra cautious, even if the scam comes through text messages or email. Do not click on any suspicious links, as they can install malware on your device and steal your personal data.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android & iOS devices at CyberGuy.com.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
3) Reduce your digital footprint to stop scammers
The truth is, your data is already out there, from old social media profiles to past breaches. That’s often how scammers get enough personal details to sound legitimate. Investing in a data removal service can help reduce your digital footprint by scrubbing your information from people-search sites and data brokers.
While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com.
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com.

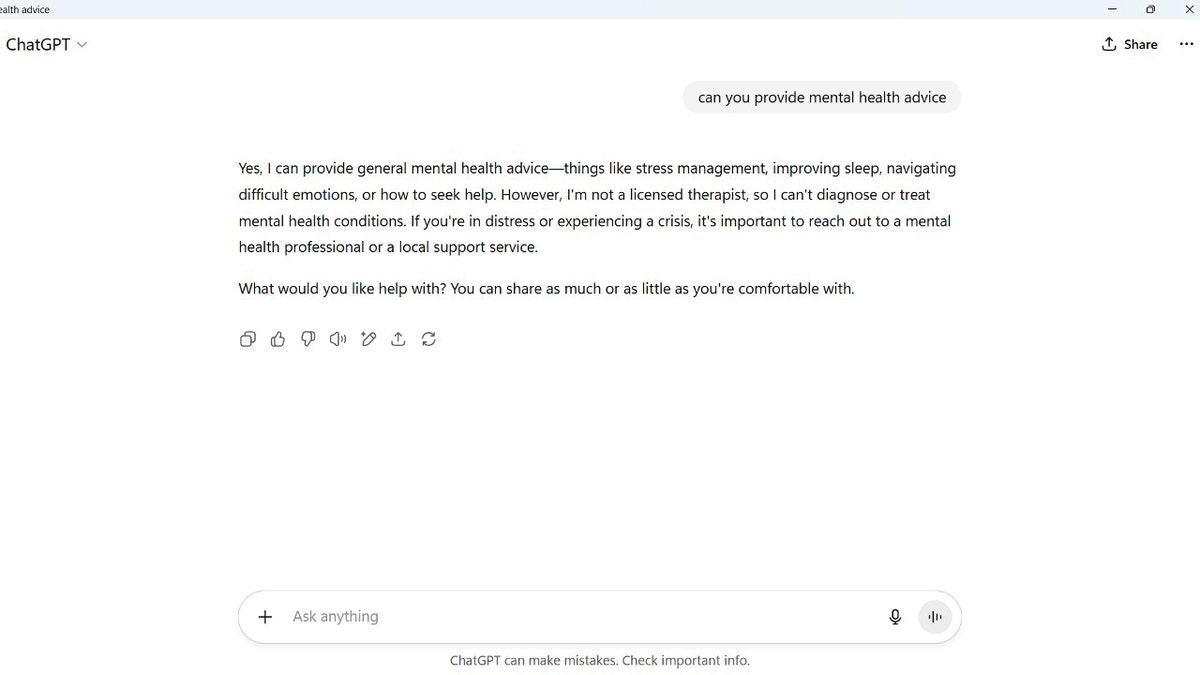
Victims of jury duty phone scams can block and report suspicious numbers to local law enforcement or fraud reporting agencies. (Kurt “CyberGuy” Knutsson)
4) Block and report scam numbers
If you receive a scam call, report it to local law enforcement or your country’s fraud reporting agency. After hanging up, block the number on your phone and report it to:
- FTC (USA): reportfraud.ftc.gov
- Local police or sheriff’s office
- Your phone carrier’s scam call reporting option
Many carriers allow you to forward scam texts to 7726 (SPAM).
5) Use call screening or spam protection apps
Apps like Truecaller, Hiya, and built-in features like Google Call Screen or Silence Unknown Callers on iPhones can detect and block fake calls automatically.
Pro Tip: Enable your phone’s “silence unknown callers” feature for extra protection.
6) Talk to vulnerable family members
Older adults are frequent targets. Sit down with your parents, grandparents, or neighbors to explain how these scams work and what to watch for. A simple heads-up could stop a costly mistake.
What this means for you
Scammers are getting bolder and more convincing, but you can stay a step ahead. Knowing the signs of a jury duty phone scam, using smart tools like antivirus and call blockers and limiting your digital footprint can dramatically reduce your risk. Empower yourself and your loved ones with this knowledge.
CLICK HERE TO GET THE FOX NEWS APP
Kurt’s key takeaway
Instead of relying on faceless phishing emails, scammers are now using hyper-personalized and emotionally charged phone calls. By impersonating local authorities and referencing civic duties like jury duty, they exploit both fear and a sense of responsibility. What makes this especially dangerous is how plausible it sounds, drawing on real processes that many people don’t fully understand.
Do you think law enforcement and government agencies are doing enough to educate the public about these scams? Let us know by writing to us at Cyberguy.com.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
[ad_2]