NEWYou can now listen to Fox News articles!
Keeping your computer secure is more important than ever. Cyberattacks target computers, accounts and sensitive data daily. Traditional passwords have long been the cornerstone of security, but they come with real challenges. Many of us reuse passwords across sites, and even strong passwords can be compromised in data breaches.
Passkeys offer a safer and more convenient way to authenticate. However, they’re still relatively new, and many of us are still trying to figure out how they work. For example, Peter recently reached out asking, “How do I get a passkey from a PC desktop that doesn’t have a camera or fingerprint device?”
That’s a great question, Peter, and you’re not alone in wondering about this. The good news is that passkeys are designed to work on virtually any device, whether or not it has biometric hardware like a fingerprint reader or camera. Let’s explore what passkeys are, why they’re worth using and how to set them up on both Windows and Mac, regardless of your hardware setup.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM newsletter.
10 WAYS TO SECURE YOUR OLDER MAC FROM THREATS AND MALWARE
Passkeys make signing in faster and safer by replacing traditional passwords with encrypted keys. (Kurt “CyberGuy” Knutsson)
What are passkeys?
Passkeys use cryptography to prove who you are. When you create a passkey, your device makes two keys, one public and one private. The public key goes to the website, and your private key stays on your device. During login, your device confirms your identity with the private key. The website never sees or stores it.
This process blocks phishing and password theft. It also makes sign-in faster. You don’t need to remember or type long passwords anymore.
While passkeys simplify authentication, they don’t eliminate the need for a secure password manager. Password managers can safely store and sync your passkeys, just as they do with passwords, allowing you to access your credentials across devices and browsers — even if those devices don’t natively sync passkeys, such as between Windows and Apple systems. Using a password manager alongside passkeys creates a bridge between platforms and provides an additional layer of security and convenience.
Can you use passkeys without biometrics?
Yes, you can. A PC or Mac without a camera or fingerprint reader can still use passkeys. On Windows, you unlock them with your Windows Hello PIN. On Apple devices, you can use Touch ID, Face ID or your passcode. The key is having an updated operating system and browser that support passkeys.
If you manage multiple accounts or devices, a password manager that supports passkeys can act as your central vault. This lets you use passkeys even on systems that don’t directly support syncing through iCloud or Google Password Manager. It’s an easy way to ensure you always have access to your credentials, no matter what kind of device you use.
Why you still need passwords
Not every website supports passkeys yet. Some services still rely on passwords. Keep strong, unique passwords for those accounts. Passwords also serve as backup if you lose a device or can’t use your passkey. Over time, more sites will support password-free logins.
This is where password managers continue to play an important role. They bridge the gap between old and new authentication methods, allowing you to store both traditional passwords and passkeys in one secure place. Until the web is fully passkey-ready, combining the two provides both convenience and resilience, giving you a seamless experience across multiple devices and services.
Passkeys also prevent phishing because your private key never leaves your device during sign-in. (Kurt “CyberGuy” Knutsson)
Passkey support by platform
Windows
- Works on Windows 10 and 11.
- Windows 11 version 22H2 (KB5030310+) includes passkey management.
- Unlock with Windows Hello PIN, face, or fingerprint.
If your browser or operating system doesn’t yet sync passkeys automatically, a third-party password manager with passkey support can store them for cross-platform access.
macOS and iOS
- Works on macOS 13 Ventura or later and iOS/iPadOS 16 or later.
- Passkeys sync through iCloud Keychain with end-to-end encryption.
- Two-factor authentication must be turned on.
- Use Touch ID, Face ID or your device passcode to confirm logins.
While Apple’s iCloud Keychain handles passkeys securely within its ecosystem, using a password manager that supports passkeys provides extra flexibility, letting you securely access the same credentials on non-Apple devices or browsers outside Safari.
Android
- Available on Android 9 and later.
- Android 14 adds third-party passkey manager support.
- Passkeys sync through Google Password Manager by default.
Alternatively, password managers now integrate passkey syncing, letting you use your passkeys seamlessly on both desktop and mobile devices.
Browsers
- Chrome, Edge, Safari and Firefox all support passkeys.
- Keep your browser updated for the best compatibility.
Browser-based password managers can also sync passkeys, adding flexibility if you switch between devices or operating systems.
Major services that support passkeys
As of publishing, these major services offer passkey sign-in:
- Google
- Microsoft
- Apple
- Amazon
- PayPal
- GitHub
- Uber
- eBay
- WhatsApp
- Facebook
Support continues to expand every month. Most new accounts on these platforms can now use passkeys.
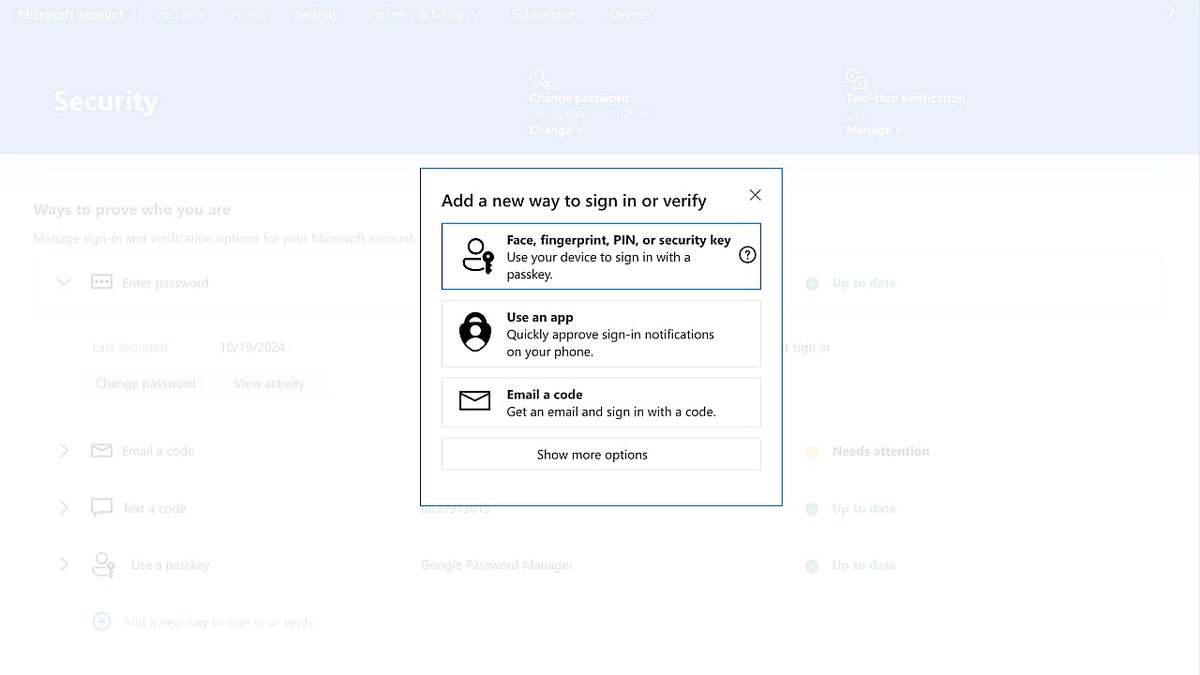
How to set up passkeys on Windows
- Open Settings → Accounts → Sign-in options.
- Set up Windows Hello PIN or biometrics.
- Visit a site that supports passkeys.
- Choose Create a passkey and confirm with your PIN or biometric.
- Manage passkeys later under Settings → Accounts → Passkeys on Windows 11.
If your PC lacks biometrics, you can still approve sign-ins using your phone nearby or a synced password manager that supports passkeys.
(Kurt “CyberGuy” Knutsson)
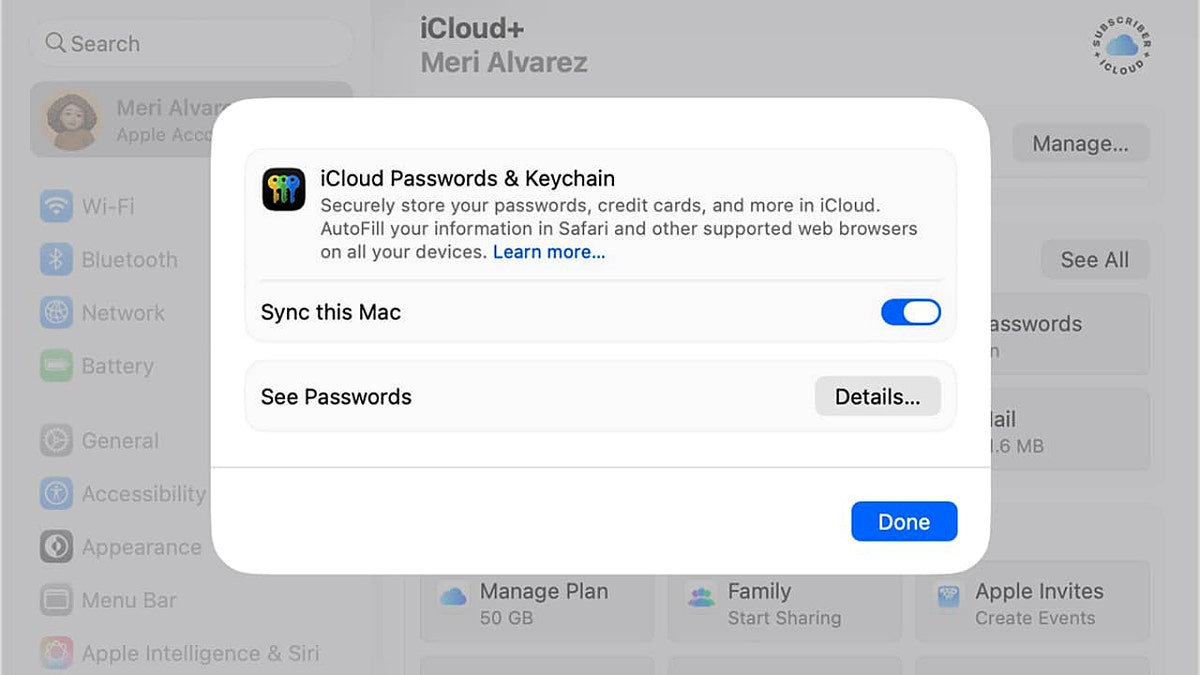
How to set up passkeys on Mac
Apple devices also provide a simple and secure way to use passkeys through iCloud Keychain. There’s no separate setup for passkeys if you have iCloud Keychain enabled. Once it’s on, an eligible app or service will ask you to create a passkey at the time of login, and you’ll be able to do so by following the instructions on the screen. Below is how you can enable iCloud Keychain.
- Go to Apple menu → System Settings → your name → iCloud.
- Click Passwords and turn on Passwords & Keychain and enable syncing.
- Visit a site that supports passkeys.
- Select Create a passkey and confirm with Touch ID or your passcode.
- Passkeys will sync to your other Apple devices through iCloud Keychain.
You can also approve logins on a non-Apple device using your iPhone nearby, or access them through a password manager that stores both your passkeys and passwords in one place.
On Windows, you can use passkeys with a simple Hello PIN, even without a camera or fingerprint reader. (Kurt “CyberGuy” Knutsson)
Common questions about passkeys
Can I move passkeys between devices?
Yes. iCloud and Google Password Manager sync passkeys securely. For more flexibility, password managers now support passkey portability across different ecosystems, perfect if you use both Mac and Windows, or Android and iPhone.
What if I lose my device?
You can recover passkeys from iCloud, Google or your password manager. Always keep a backup login method and 2FA enabled. Storing your passkeys in a secure password manager ensures recovery even if you lose access to one platform’s ecosystem.
Are passkeys fully replacing passwords?
Not yet. Many major platforms support them, but full adoption will take time. Until then, password managers remain an essential bridge technology, providing secure storage, synchronization and transition support as passkeys continue to expand.
MICROSOFT SOUNDS ALARM AS HACKERS TURN TEAMS PLATFORM INTO ‘REAL-WORLD DANGERS’ FOR USERS
5 additional steps you can take to keep your computer safe
Even with passkeys and strong passwords, there are other steps you can take to enhance the security of your computer.
1) Use a password manager
Password managers help generate and store strong, unique passwords for every account. This reduces the risk of password reuse and ensures that your backup passwords are secure. Now that many password managers support passkeys, they also act as your universal credential vault, letting you log in with either method depending on what a website supports.
Next, see if your email has been exposed in past breaches. Our #1 password manager (see CyberGuy.com) pick includes a built-in breach scanner that checks whether your email address or passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at CyberGuy.com.
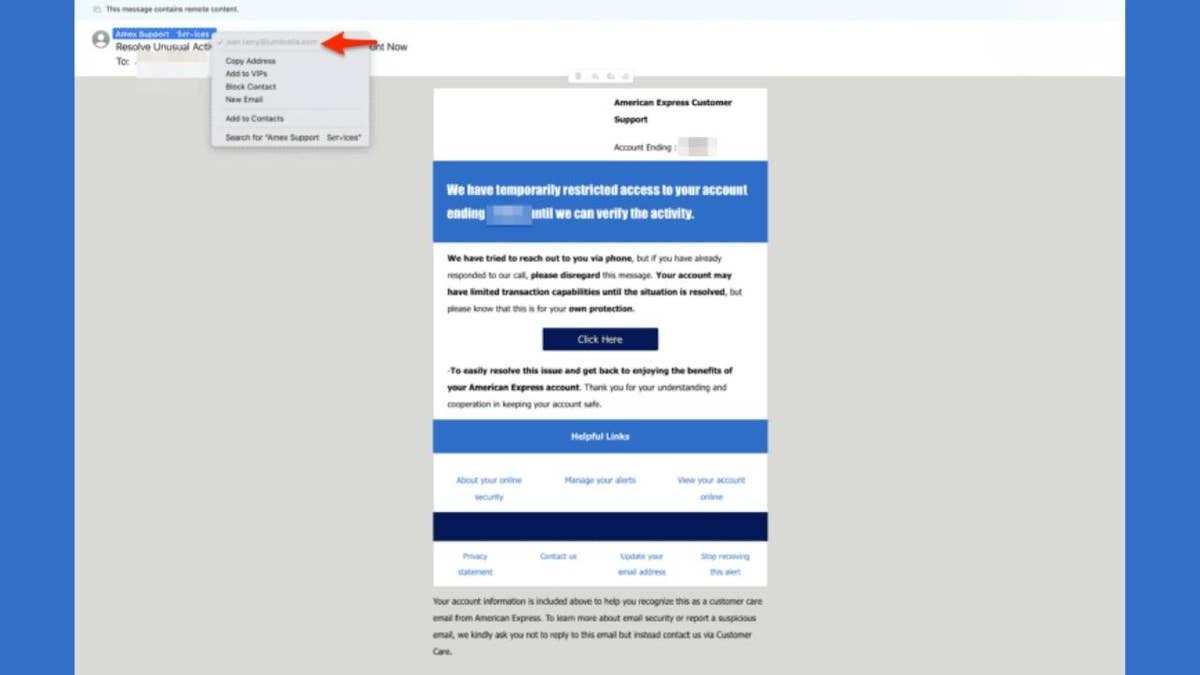
2) Install strong antivirus software
Strong antivirus software protects against malware, ransomware and other threats. The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices at CyberGuy.com.
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
3) Keep your system updated
Regular updates fix security vulnerabilities in your operating system and software. Enable automatic updates whenever possible to stay protected.
4) Enable two-factor authentication
Two-factor authentication (2FA) adds a second verification step, usually through a code sent to your phone or email, or through an authentication app. This makes it harder for attackers to access your accounts even if your password or passkey is compromised.
5) Backup your data
Regularly backing up your Mac or PC to a secure cloud service or external drive ensures that you can recover important data in case of hardware failure, malware attack, or accidental deletion.
Kurt’s key takeaway
Passkeys are a major upgrade over traditional passwords, but we’re not living in an all-passkey world just yet. Many sites still rely on passwords, and you’ll need backups if something happens to your device. Supplementing passkeys with a password manager is the best move right now; it lets you store, sync and protect both passkeys and passwords under one roof. The good news is that setting up passkeys takes just a few minutes, and once they’re enabled, logging in becomes faster and more secure.
Have you tried using passkeys yet? Let us know by writing to us at CyberGuy.com.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt “CyberGuy” Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on “FOX & Friends.” Got a tech question? Get Kurt’s free CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.