[ad_1]
NEWYou can now listen to Fox News articles!
If you’re over 50 and maxing out your 401(k), there’s a big change coming in 2026 that could affect how much tax you pay on your “catch-up contributions.” While it’s mostly about taxes and retirement planning, there’s an unexpected side effect: scammers are circling. Every time your financial habits or personal data become public, it’s a chance for fraudsters to try to exploit you. Here’s what’s changing, why it matters, and how to protect yourself before the scammers come knocking.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts, and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter
What’s changing with 401(k) catch-up contributions
REMOVE YOUR DATA TO PROTECT YOUR RETIREMENT FROM SCAMMERS
Right now, if you’re over 50, you can make extra contributions to your 401(k) on top of the standard annual limit ($23,500 in 2025). These “catch-up” contributions are typically tax-deferred, meaning the money comes out of your paycheck before tax and grows tax-free until retirement.
But starting in 2026, for anyone earning more than $145,000 in the previous year, these catch-up contributions will no longer be tax-deferred. Instead, they’ll become like the Roth 401(k), meaning you pay taxes on the money now, but it grows tax-free and can be withdrawn tax-free in retirement.
That sounds simple, but it creates a ripple effect:
- High earners will see less take-home pay now.
- Tax planning gets trickier, and some people may consider restructuring their accounts or investment strategies.
- And, most importantly for CyberGuy readers: these changes create new opportunities for scammers.
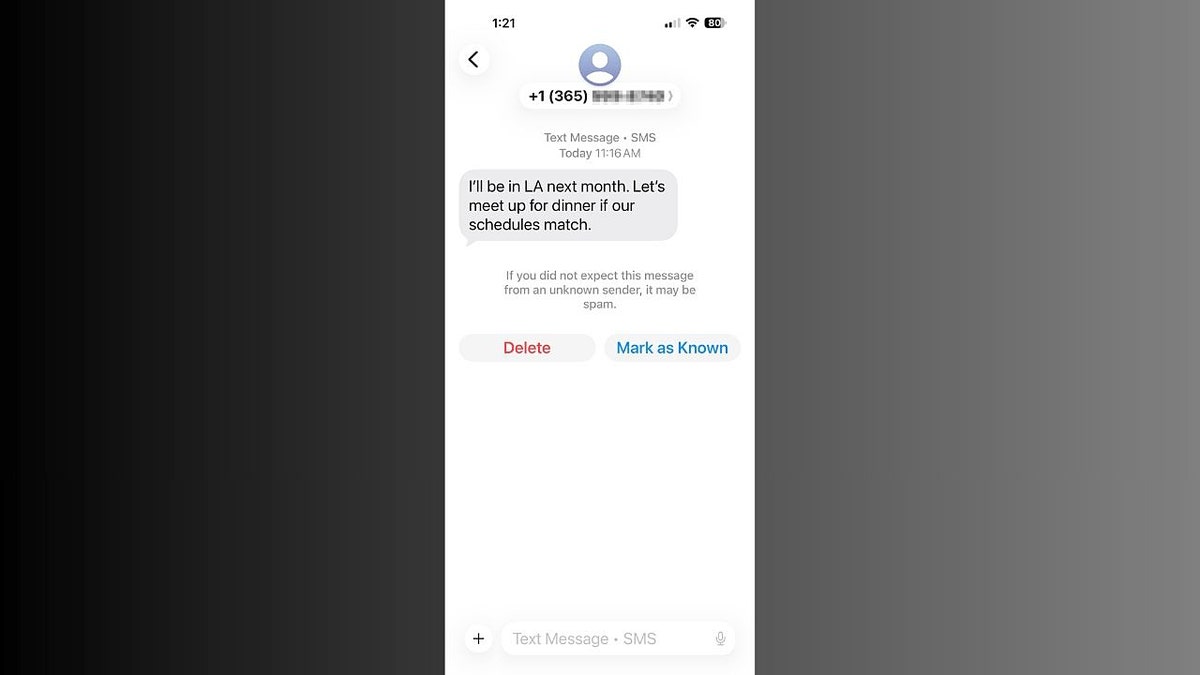
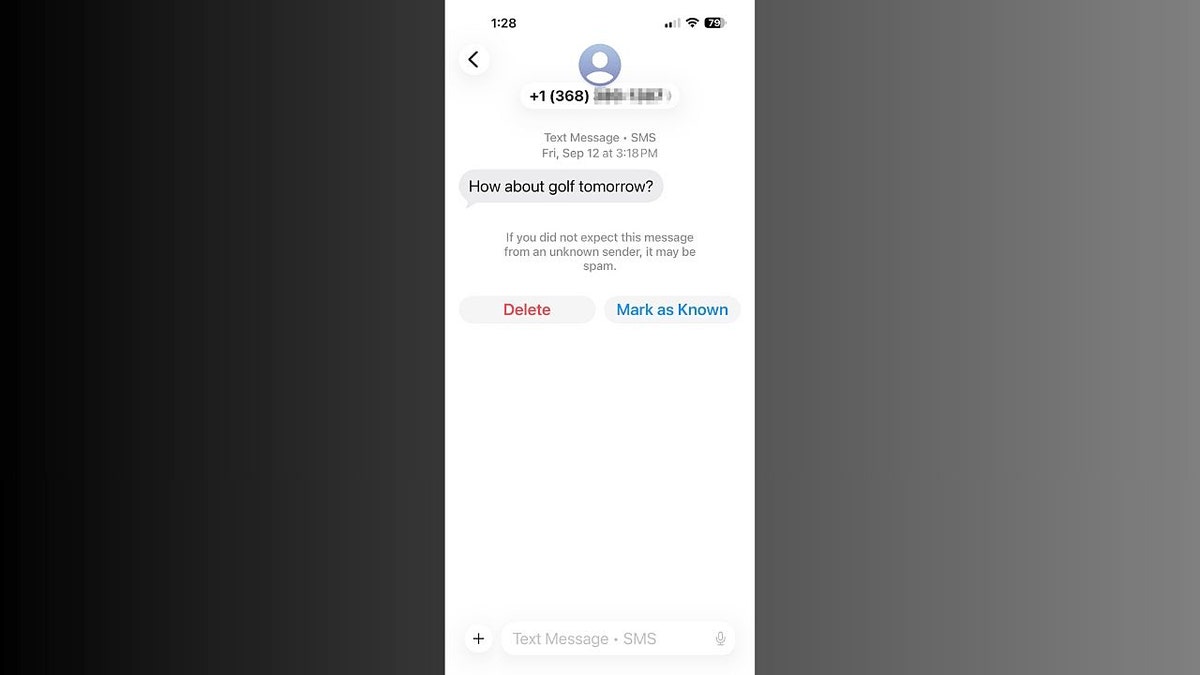
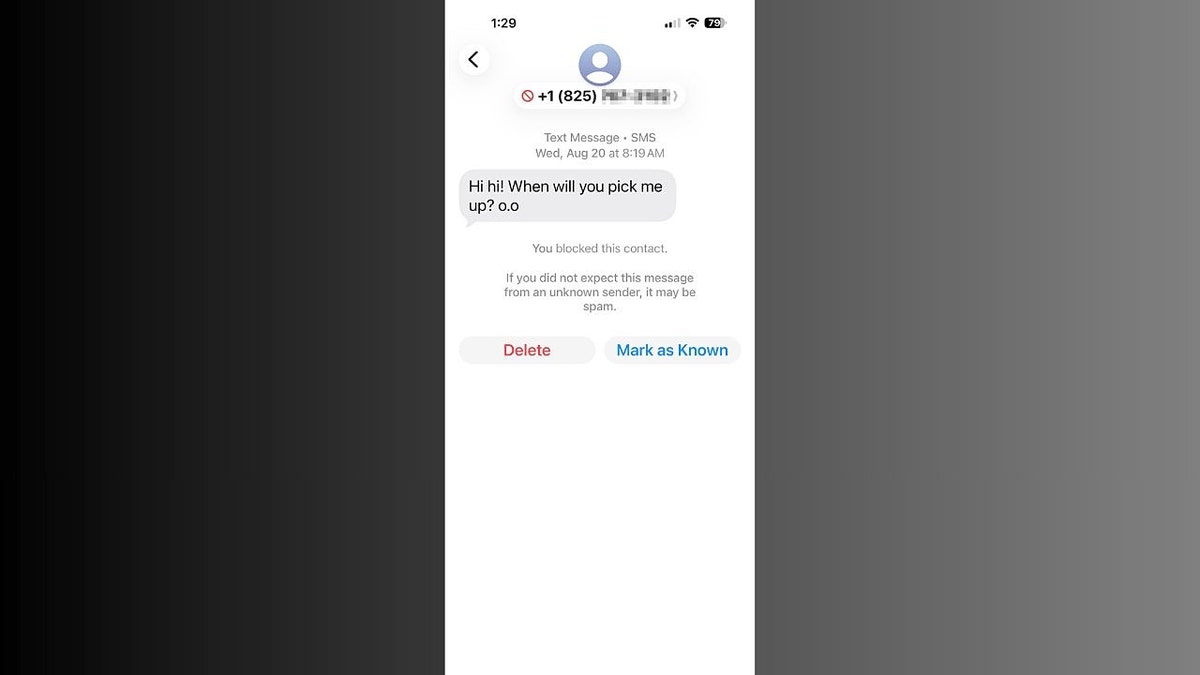
Big 401(k) changes in 2026 could leave retirees exposed to new scam risks. (Cyberguy.com)
Why the new rules could attract scammers
FBI WARNS SENIORS ABOUT BILLION-DOLLAR SCAM DRAINING RETIREMENT FUNDS, EXPERT SAYS AI DRIVING IT
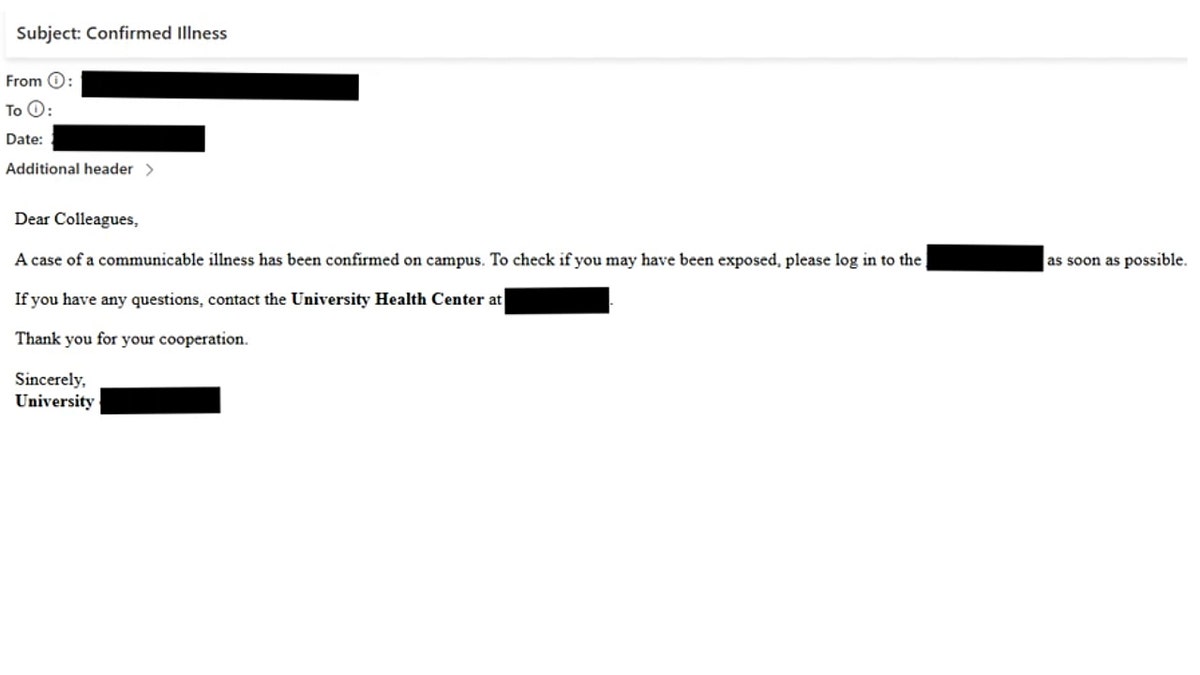
Scammers constantly look for financially active retirees. When rules like this change, fraudsters send out emails, calls, or letters pretending to be financial advisors, IRS agents, or plan administrators. Their goal? To trick you into giving away account numbers, Social Security details, or direct-deposit information.
Some common scam tactics to watch for:
- Fake “plan update” emails claiming you need to verify your 401(k) contributions due to the law change.
- Roth conversion scam calls claiming you can “avoid extra taxes” by transferring your account through a third-party “advisor.”
- Urgency and fear tactics, such as “Act now, or lose your retirement benefits!”
Even savvy retirees can be caught off guard, especially when the message sounds official and references real tax law changes.
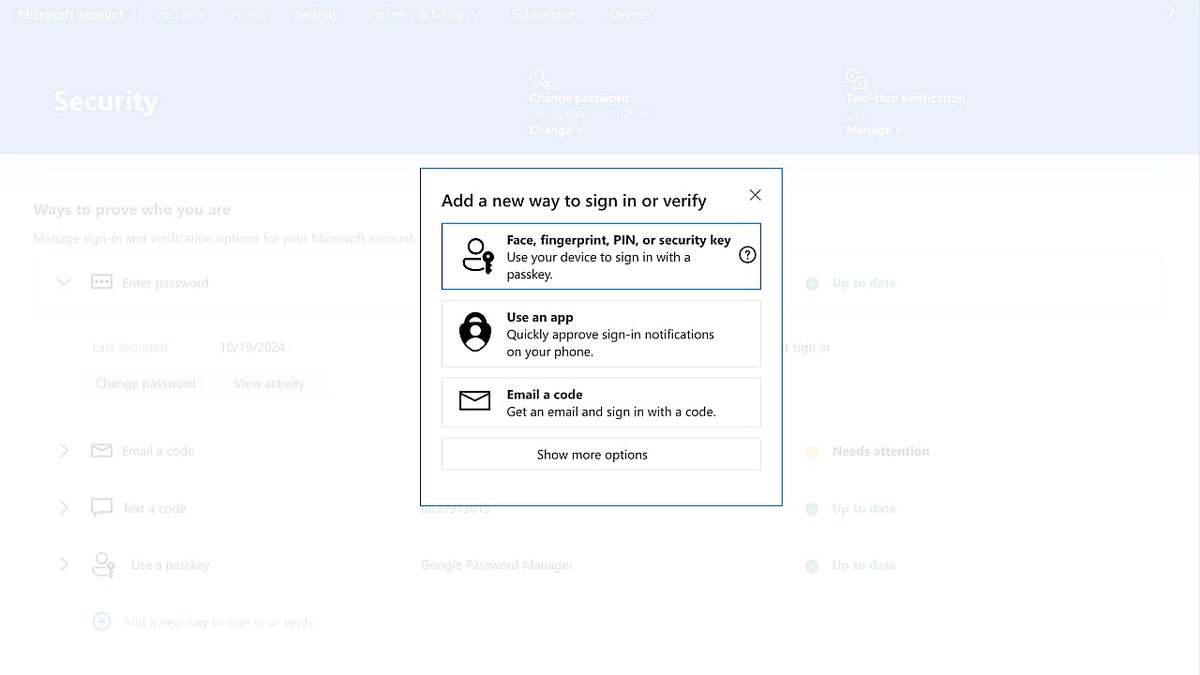
How to protect yourself from 401(k) scams and data theft
NATIONAL PROGRAM HELPS SENIORS SPOT SCAMS AS LOSSES SURGE
With new 401(k) rule changes taking effect, scammers are using the confusion to trick retirees and workers alike. Follow these steps to stay alert, safeguard your savings, and protect your personal data from being stolen or misused.
1) Know the legitimate changes
Start by understanding Secure 2.0 and how catch-up contributions will be taxed. Reliable sources include your plan administrator, the IRS website, or a licensed tax advisor. Staying informed helps you spot fake claims before they cause harm.
2) Use a personal data removal service
For retirees, this extra layer of protection keeps sensitive information out of reach from scammers who exploit tax changes, Roth conversions, and retirement updates. While you can manually opt out of data brokers and track your information, that process takes time and effort. A personal data removal service automates the task by contacting over 420 data brokers on your behalf. It also reissues removal requests if your data reappears and shows you a dashboard of confirmed removals.
While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com

Scammers are already targeting retirees with fake “account update” alerts. (Kurt “CyberGuy” Knutsson)
HOW TO SECURE YOUR 401(K) PLAN FROM IDENTITY FRAUD
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com
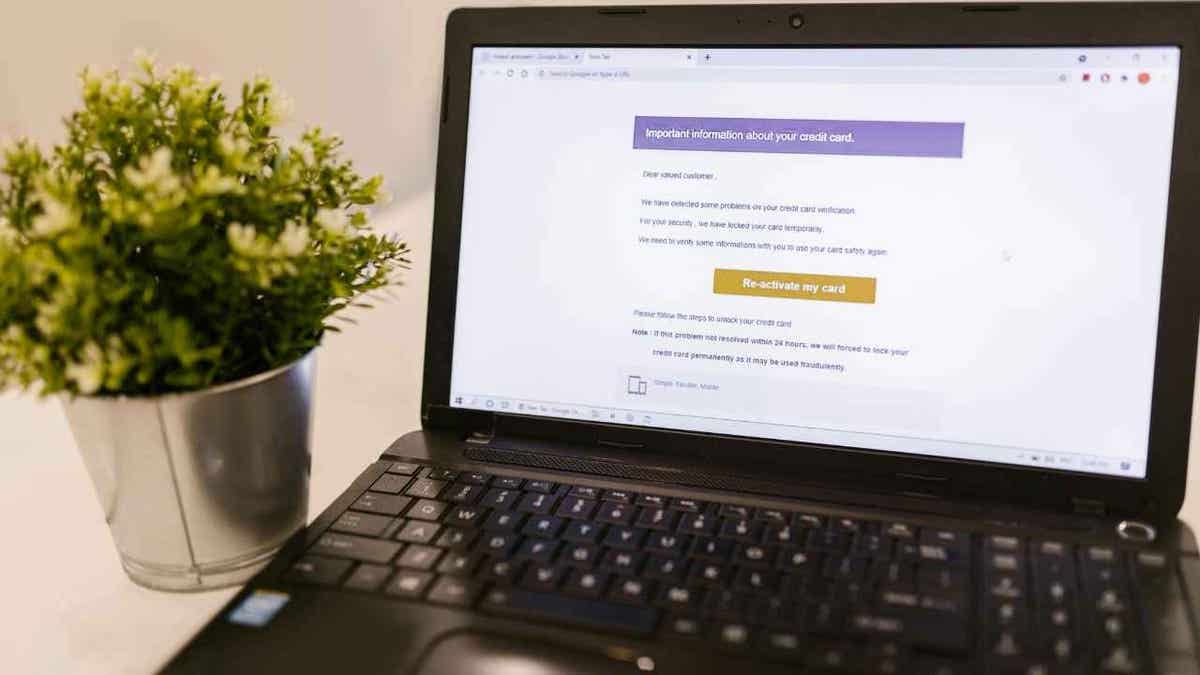
3) Verify every call and email, plus use antivirus software
If you get a call or email about your 401(k), don’t assume it’s real. Hang up or delete it, then contact your plan administrator directly using official contact details. Avoid clicking links or downloading attachments from unknown messages.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android & iOS devices at Cyberguy.com
4) Monitor your credit and accounts
Cybercriminals often use personal information from earlier data leaks or data brokers. Watch your credit reports and account activity closely. Early detection can stop suspicious transactions before they escalate.
HOW SCAMMERS EXPLOIT YOUR DATA FOR ‘PRE-APPROVED’ RETIREMENT SCAMS
5) Set up alerts and freezes if necessary
Ask your bank and retirement plan to enable transaction alerts. You can also temporarily freeze your credit to prevent anyone from opening new accounts in your name. This is especially useful during times of financial change.
6) Educate friends and family
Scammers often target retirees and their relatives who help manage finances. Remind your loved ones never to share account details over the phone or email. Protecting everyone in your household keeps scammers from finding weak links.
Stay safe by confirming any 401(k) changes directly with your plan provider. (uchar/Getty Images)
Kurt’s key takeaways
As 2026 approaches, the new 401(k) rule changes will reshape how millions of Americans manage their retirement savings. Staying informed, cautious, and proactive can protect your financial future. Scammers thrive on confusion, but by verifying information, monitoring your accounts, and removing your personal data from risky sites, you can stay one step ahead. Remember, the more control you take over your privacy, the harder it becomes for criminals to exploit it.
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
Have you taken steps to see where your personal data is exposed, and what did you find most surprising when you checked? Let us know by writing to us at Cyberguy.com
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts, and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
[ad_2]