NEWYou can now listen to Fox News articles!
Your Mac holds a lot more than just files. It carries your personal information, payment data, messages and every online account you access. Keeping that information safe starts with how you sign in. For years, passwords have been the standard way to protect accounts, but they are also one of the weakest links in digital security. They can be guessed, stolen or reused across multiple sites.
Apple’s introduction of passkeys marks a major step forward. Instead of relying on something you need to remember, passkeys rely on something you have (your trusted Apple device) and something you are, like your fingerprint or face. Together with iCloud Keychain and two-factor authentication, passkeys create a seamless and much safer way to secure your Mac and your digital life.
What are passkeys?
Passkeys are a modern alternative to passwords. They use public key cryptography to let you sign in without ever creating or typing a password. When you register for an account using a passkey, your Mac creates two unique keys. One is public and stored by the website or app, and the other is private and stays securely on your device.
The public key is not sensitive information. The private key, on the other hand, never leaves your Mac and is protected behind your device’s security features. When you sign in, Touch ID or Face ID confirms your identity before your Mac uses the private key to authenticate you. This process prevents phishing and password leaks because no shared secret is ever transmitted to the website.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM newsletter.
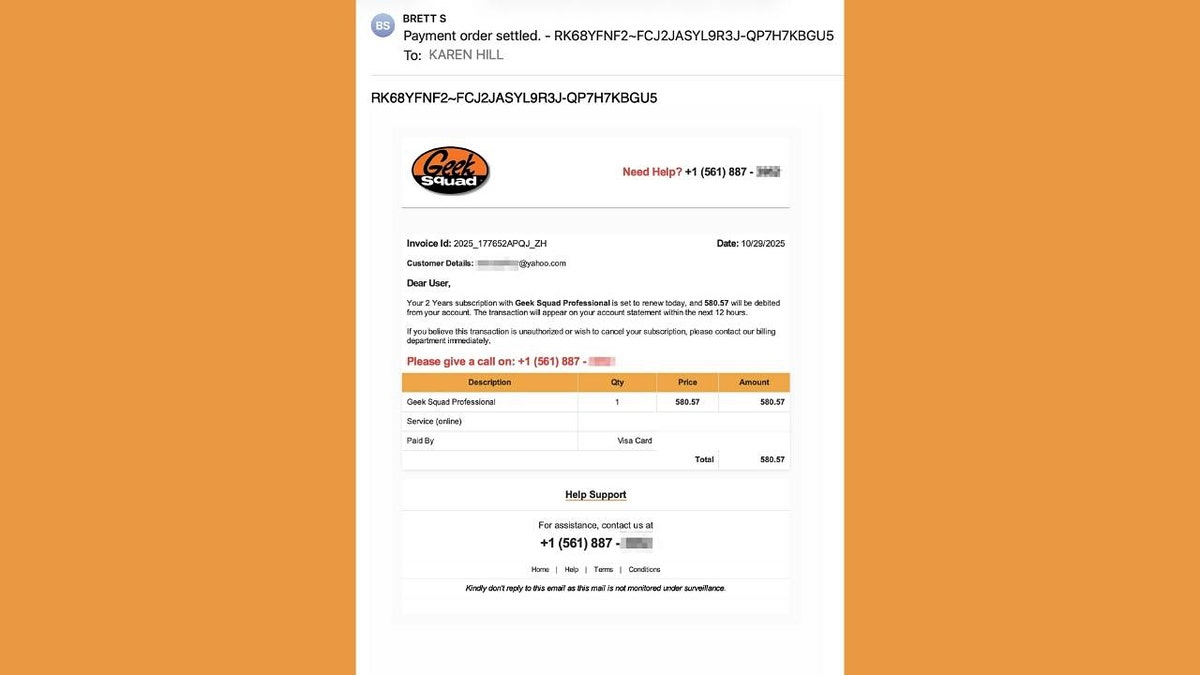
HOW TO USE PASSKEYS TO KEEP YOUR COMPUTER SAFE
A passkey on your Mac replaces passwords with a faster, more secure way to sign in. (Kurt “CyberGuy” Knutsson)
How Apple keeps passkeys secure
Passkeys are stored and synced across your devices through iCloud Keychain, which is protected by end-to-end encryption. This means that not even Apple can access your passkeys or passwords. iCloud Keychain also has built-in protection against brute force attacks, even if someone were to gain unauthorized access to Apple’s servers.
If you lose your devices, you can still recover your passkeys through iCloud Keychain recovery. To do this, you must sign in with your Apple ID and password, verify your identity with a code sent to your trusted number and confirm using your device passcode. The system limits the number of attempts, and if too many failed attempts occur, the recovery record is locked or destroyed to prevent misuse.
You can also set an account recovery contact to make sure you never lose access, even if you forget your Apple ID password or device passcode. This multi-layered design ensures that your data remains secure even in extreme scenarios, such as a compromised Apple account or cloud breach.
How to set up passkeys on your Mac
Setting up passkeys is simple and requires iCloud Keychain to be enabled.
- Choose the Apple menu, then select System Settings.
- Click your name, then click iCloud.
- Click Passwords. In macOS Sonoma or earlier, click Passwords & Keychain.
- Click Sync this Mac, then click Done.
- When you sign up for a website or app that supports passkeys, you’ll now see the option to create a passkey.
- If your Mac has Touch ID, place your finger on the sensor to confirm.
- If you are using an iPhone or iPad nearby, select Other Options and scan the QR code shown on your Mac to confirm with Face ID.
- You can also replace an existing password by visiting the account settings of a supported website or app and selecting the option to switch to a passkey.
Once created, your passkeys are automatically stored in iCloud Keychain and available on all devices signed in with the same Apple ID.
Major services that support passkeys
Passkey adoption is growing quickly across major tech platforms. As of now, many of the biggest online services already let you sign in without a password.
Some of the key ones include:
- Google
- Microsoft
- Apple
- Amazon
- PayPal
- GitHub
- Uber
- eBay
- WhatsApp
- Facebook
Support for passkeys continues to expand every month as more companies integrate the technology into their login systems. On most of these platforms, you can now create new accounts or switch your existing ones to passkeys for faster, more secure sign-ins.
Each passkey is unique to your account and safely stored in your device’s iCloud Keychain. (iStock)
6 additional steps to keep your Mac safe
Passkeys add a strong layer of protection, but good security habits still matter. Here are more steps to strengthen your Mac’s defenses.
1) Enable two-factor authentication
Two-factor authentication (2FA) adds another layer of protection to your Apple ID. It works by requiring two forms of verification: your password and a one-time code sent to a trusted device or phone number. This means that even if someone somehow gets your password, they still cannot access your account without also having your device.
10 WAYS TO SECURE YOUR OLDER MAC FROM THREATS AND MALWARE
2) Review your trusted devices and numbers
Regularly check which devices and phone numbers are linked to your Apple ID. On your Mac, click the Apple icon in the upper left of the screen. Then go to System Settings → Apple ID → Devices and remove anything you don’t recognize. Make sure your trusted phone number is still current, since it’s critical for account recovery.
3) Use a password manager
Even though passkeys are replacing passwords, many sites still rely on traditional logins. A password manager helps you create, store and fill in unique passwords for every account. iCloud Keychain can do this automatically across all your Apple devices, but if you want more flexibility, you might want to consider a third-party password manager.
Next, see if your email has been exposed in past breaches. Our No. 1 password manager pick includes a built-in breach scanner that checks whether your email address or passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at Cyberguy.com.
4) Be wary of phishing attempts and install strong antivirus software
Phishing remains one of the most common ways attackers try to steal personal information. They may send fake emails or messages pretending to be from Apple or other trusted companies, urging you to click links or provide login details. Always double-check the sender’s address and avoid clicking on links that seem suspicious. Instead, visit the website directly by typing the address into your browser.
While macOS has strong built-in defenses such as Gatekeeper and XProtect, installing strong antivirus software adds another layer of protection against malware, adware and potentially unwanted programs. Strong antivirus software continuously monitors your system for suspicious behavior and can alert you to threats before they cause damage. It is especially useful if you download files from outside the App Store or connect external drives frequently.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices at Cyberguy.com.
Using a passkey with Touch ID or Face ID keeps your information protected from phishing and leaks. (Kurt “CyberGuy” Knutsson)
5) Turn On FileVault disk encryption
FileVault protects everything stored on your Mac by encrypting the entire hard drive. That means if your computer is ever lost or stolen, your data stays locked away from prying eyes. Go to System Settings → Privacy & Security → FileVault to enable it.
6) Keep macOS updated automatically
Apple regularly releases software updates that include important security patches. Cybercriminals often target outdated systems because they contain known vulnerabilities. By keeping macOS and your apps up to date, you make it harder for attackers to exploit weaknesses. To make this effortless, turn on Automatic Updates under System Settings → General → Software Update → Automatic Updates.
7) Back up with time machine
Backing up your Mac is just as important as protecting it. Time Machine automatically backs up your files to an external drive or network disk, keeping your data safe from ransomware, hardware failure or accidental deletion. Make sure your backup drive is encrypted for extra protection.
HOW A SINGLE MACBOOK COMPROMISE SPREAD ACROSS A USER’S APPLE DEVICES
8) Use a data removal service
Even with passkeys, your personal information can still be exposed through data broker sites that collect and sell your details. Using a data removal service can help remove your private data from hundreds of these sites automatically. It’s an effective way to reduce your online footprint and protect your identity, especially when combined with Apple’s built-in security tools.
While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com.
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com.
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
Kurt’s key takeaway
Passwords have served us for decades, but they are no longer enough to protect our digital identities. Passkeys make signing in faster, easier and significantly more secure by removing the weaknesses of traditional passwords. Combined with Apple’s encryption, iCloud Keychain and two-factor authentication, they represent one of the safest ways to protect your Mac and everything on it.
Have you tried using passkeys yet on your Mac, and what was your experience like? Let us know by writing to us at Cyberguy.com.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt “CyberGuy” Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on “FOX & Friends.” Got a tech question? Get Kurt’s free CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.