[ad_1]
NEWYou can now listen to Fox News articles!
Social media makes it easy to connect with people, but it also makes it just as easy for fraudsters to pretend they are someone they are not. Fake accounts, misleading checkmarks and smooth-talking profiles are everywhere, and not everyone knows how to spot them. I recently received an email from Marie from Boynton Beach, Florida, with a similar concern:
“I have been on X, and it seems quite a few people turn out to be not who they say they are. Mostly the ones that are verified. I am not that good tech-wise. Is there a way other than me knowing immediately they are a fraud?? Thank God I am not the type to give personal information or money.”
It is a fair concern, Marie. With scams becoming more polished, the line between real and fake accounts is harder to see. Let’s break down why fraud is so common on social media, the red flags you should look out for, and the simple habits that can keep you from getting duped.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
WHATSAPP BANS 6.8M SCAM ACCOUNTS, LAUNCHES SAFETY TOOL
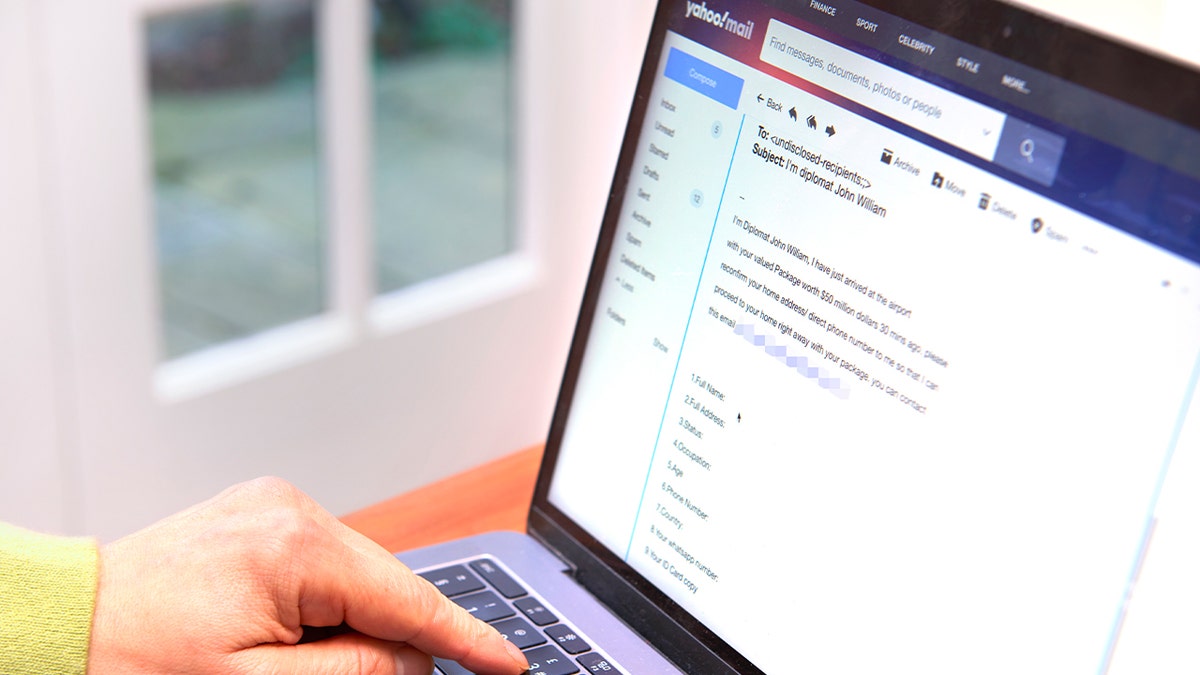
A man logs into his social media account on a laptop. Fraudsters often exploit online activity to trick users. (Kurt “CyberGuy” Knutsson)
Why social media is a playground for scammers
Social platforms are built for speed and visibility. Anyone can create an account in minutes, post content instantly and connect with strangers worldwide. This openness is what makes social media engaging, but it is also what makes it ripe for abuse. Fraudsters exploit the fact that posts, comments and messages are consumed quickly and often without much scrutiny.
Verification systems that were once meant to help users identify legitimate accounts have also lost some of their power. On platforms where checkmarks can be purchased, scammers can buy credibility without earning it. Add in the algorithms that reward viral content and sudden spikes in engagement, and you get the perfect environment for fraud to spread unnoticed.
Scammers know people often lower their guard on social media. In these spaces, users share personal details, build emotional ties with influencers and trust posts that look familiar. As a result, the combination of speed, trust and visibility creates an ideal environment for fraud to spread rapidly.
META DELETES 10 MILLION FACEBOOK ACCOUNTS THIS YEAR, BUT WHY?

A woman browses social media on her laptop. Scammers use fake accounts and misleading profiles to lure victims. (Kurt “CyberGuy” Knutsson)
The cost of falling for a scam
When people think of scams, they often imagine losing a one-time sum of money. The reality is far more damaging. Clicking a bad link or handing over credentials can snowball into long-term consequences. Once scammers get access to your information, it can be sold on dark web marketplaces, used to open fraudulent accounts or leveraged for identity theft.
There is also the reputational cost. If your social media account is hijacked, scammers can use it to trick your friends, family or followers, spreading fraud even further under your name. Cleaning up that mess can take weeks and may permanently damage your credibility.

Social media apps are prime hunting grounds for scammers who rely on speed and trust to deceive victims. (Kurt “CyberGuy” Knutsson)
Practical steps you can take to stay safe on social media
There are simple ways to protect yourself without needing technical expertise. I have listed some of the crucial steps below.
1) Scrutinize profiles before engaging
Fake accounts often have clear giveaways. Look at how long the account has existed, whether it posts original content and the kind of followers it has. Scammers usually recycle generic profile photos or steal images from real people. Reverse image searches can help you confirm if a photo belongs to someone else.
Even with verification, be skeptical. On platforms where checkmarks can be purchased, anyone can appear “official” without being trustworthy. Treat every new interaction with caution until proven otherwise.
FACEBOOK CRYPTO ADS LEAD TO DANGEROUS MALWARE SCAMS
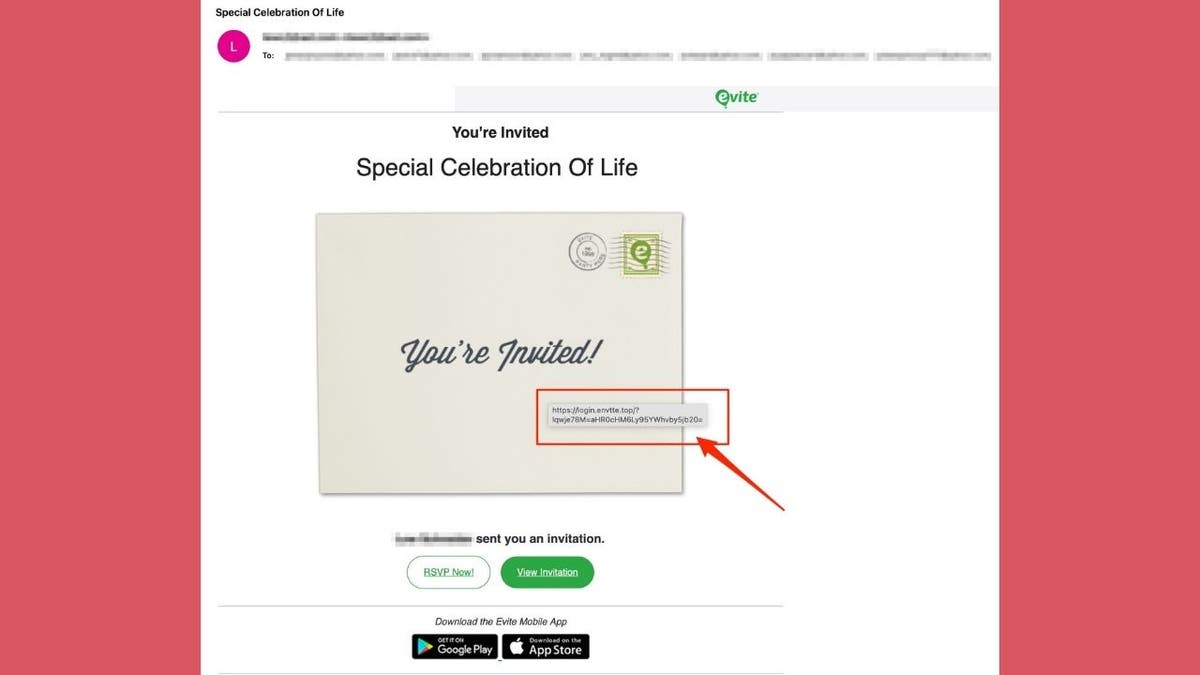
2) Avoid clicking on random links
Fraudsters often send links over DMs, comments or even ads. These links may lead to phishing sites designed to steal your credentials or malware that installs silently on your device. One careless click can expose your information.
This is where having strong antivirus software comes in. Even if you accidentally land on a malicious site, a strong antivirus can block harmful downloads and warn you before malware runs. Think of it as a safety net for moments when curiosity gets the better of you.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices at Cyberguy.com/.
3) Protect your logins
Phishing scams frequently mimic login screens for X, Instagram or Facebook. They are designed to trick you into typing your username and password into a fake form. Once you do, the scammer immediately takes over your account.
A password manager can be a lifesaver here. It only fills in your login details on the genuine site you have saved. If it does not recognize the page, that is a red flag that you are looking at a fake. On top of that, a password manager makes it easier to use strong, unique passwords for each account, which limits damage if one gets compromised.
Next, see if your email has been exposed in past breaches. Our No. 1 password manager pick includes a built-in breach scanner that checks whether your email address or passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at Cyberguy.com/.
4) Keep personal info under wraps
The less information fraudsters can find about you, the weaker their scams become. Many impersonators use details like your hometown, job or relatives to build trust. If your email, phone number or address is floating around the web, scammers can weaponize that too.
A personal data removal service can help here by scrubbing your details from people-search sites and data brokers. While not foolproof, reducing your digital footprint makes you a harder target for impersonation or social engineering scams. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com.
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com/.
SOCIAL SECURITY ADMINISTRATION PHISHING SCAM TARGETS RETIREES
5) Stay alert to impersonation scams
Fraudsters often pretend to be well-known figures, influencers or even customer support staff. They use urgency like “limited offer,” “you have won” or “your account will be closed” to pressure you into responding fast.
When money, gift cards or personal details are involved, slow down. Contact the real brand or person through official channels to verify. If you are unsure, simply ignore the request.
6) Trust your instincts
One of the strongest defenses you have is your gut feeling. If a verified profile is asking for money, if a giveaway sounds too good to be true or if someone’s tone feels off, it probably is. Scammers rely on you ignoring that little voice that says something is not right.
Take a breath, pause and think before you act. That moment of hesitation often makes the difference between staying safe and becoming a victim.
CLICK HERE TO GET THE FOX NEWS APP
Kurt’s key takeaway
Social media can be entertaining, informative and even empowering, but it is also one of the easiest hunting grounds for fraudsters. They thrive on speed, trust and distraction, hoping you will react before you think. While no tool or habit can guarantee absolute safety, combining skepticism with smart protective steps puts you in a much stronger position.
Do you think paid verification badges make it harder to spot scammers? Let us know by writing to us at Cyberguy.com/Contact
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
[ad_2]