[ad_1]
NEWYou can now listen to Fox News articles!
When you search Google for apps, it feels natural to trust the first results you see. They’re supposed to be the most reliable, right? Unfortunately, hackers know this too. They’re sneaking fake websites into search results that look just like the real thing. If you click and download from one of these sites, you could end up with malware instead of the app you wanted. In other words, the top search results aren’t always safe, and that’s exactly how scammers trick people.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
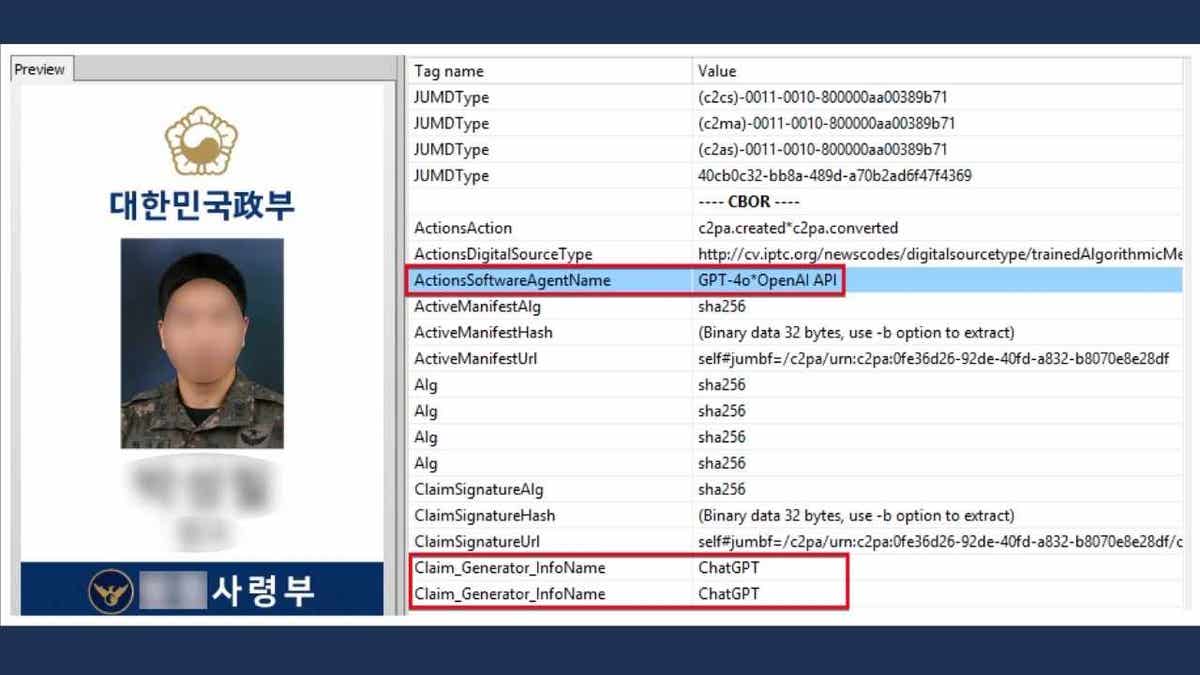
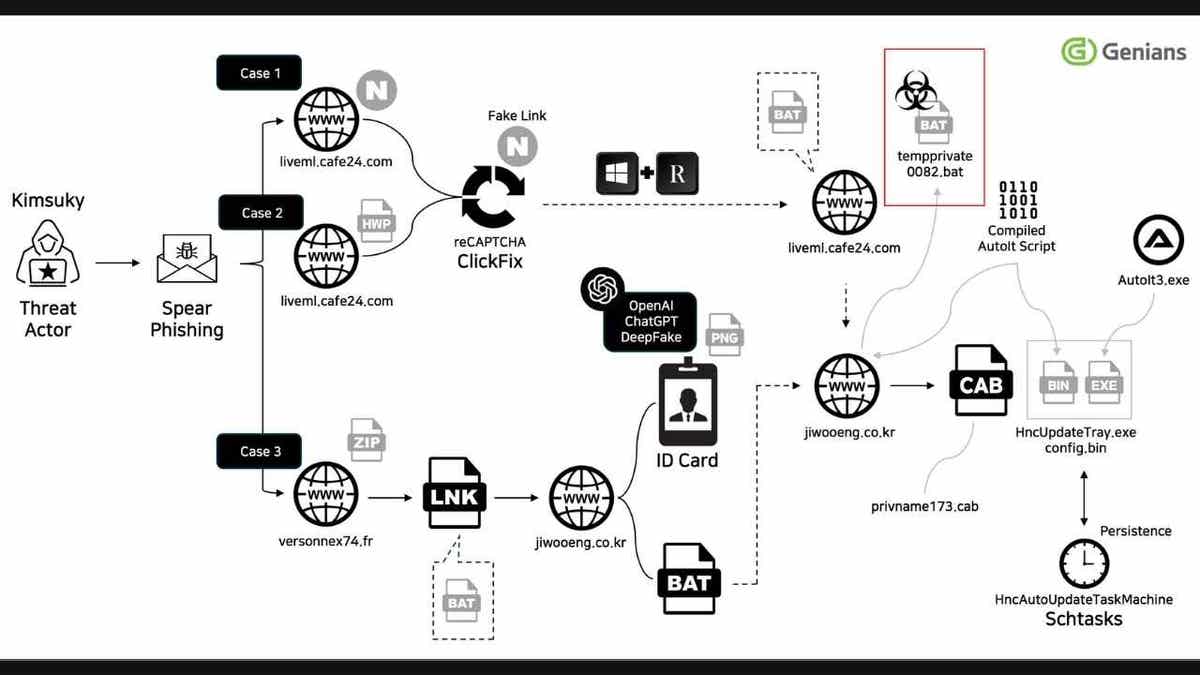
NORTH KOREAN HACKERS USE AI TO FORGE MILITARY IDS
What you need to know about malware in Google searches
Researchers at FortiGuard Labs found that attackers are setting up websites that look almost identical to trusted providers. These sites host installers for apps like Signal, WhatsApp, Deepl, Chrome, Telegram, Line, VPN services and WPS Office. The catch is that these downloads include both the real app and hidden malware.
Once you run one, the malware drops files into your system, asks for administrator access and quietly starts spying. It can collect personal information, log everything you type, monitor your screen and even disable your antivirus.
Hackers are planting fake apps in Google search results and they look just like the real thing. (Harun Ozalp /Anadolu via Getty Images)
Some versions were designed to snoop on Telegram messages. All of this is possible because hackers use a tactic called SEO poisoning, which manipulates Google’s search results so their fake websites appear near the top. Even if you stick to “safe-looking” search links, you could still land on a fraudulent page.
How hackers disguise fake apps as real ones
So how do these fake sites end up in your search results in the first place? The attackers use a technique called SEO poisoning. They register lookalike domains, use plugins to game search algorithms and then climb up Google’s rankings. That way, when you search for a trusted app, the fake site may appear as one of the first results.
According to FortiGuard Labs, this particular campaign mainly targeted Chinese-speaking users, but the method is being used everywhere. In fact, earlier reports from Cisco Talos showed ransomware groups pushing fake downloads of AI tools like ChatGPT or InVideo. Others used spoofed sites for PayPal, Microsoft, Netflix and Apple. Sometimes, attackers even buy sponsored ads so that their malicious links appear right at the top.
The scary part is that you might not even realize you installed something dangerous. Because the fake installer includes the real app, everything seems to work fine. Meanwhile, the hidden malware is already active on your device. That makes it harder to detect and much easier for attackers to steal your data.
6 ways you can stay safe from malware in Google Searches
I have listed some steps below that you can take to protect yourself from these fake apps and the malware they carry.
1) Download apps only from official sources
The safest way to avoid malware is to get software directly from the official website or verified app stores like Google Play or the Apple App Store. Avoid third-party download sites or search results that look suspicious, even if they appear at the top of Google.
2) Double-check website domains
Before clicking “download,” carefully inspect the domain name. Hackers often create lookalike domains that look nearly identical to real ones, adding small spelling changes or extra words. Even small differences can indicate a fake site designed to deliver malware.
TOP 5 OVERPAYMENT SCAMS TO AVOID

Cybercriminals are disguising malware as trusted apps, tricking users through poisoned search results. (Dilara Irem Sancar/Anadolu via Getty Images)
3) Install a reliable antivirus software
Malware can install itself quietly and avoid detection. Using a strong antivirus solution can help identify and block malicious files before they cause damage. Make sure your antivirus is always updated so it can recognize the latest threats, including Hiddengh0st and Winos variants.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices at Cyberguy.com.
4) Use a password manager
If malware tries to capture your passwords, a password manager can protect you. It generates strong, unique passwords for each account and stores them securely. Many password managers can also alert you if your credentials appear in a data breach.
Next, see if your email has been exposed in past breaches. Our No. 1 password manager pick includes a built-in breach scanner that checks whether your email address or passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at Cyberguy.com.
5) Be cautious with ads in search results
Attackers sometimes buy sponsored Google ads to push malware. Even if an ad looks like it comes from a trusted brand, verify it carefully before clicking. Stick to official websites whenever possible.
6) Keep your software and system updated
Outdated operating systems and applications can have vulnerabilities that malware exploits. Regularly updating your software ensures you have the latest security patches and reduces the risk of infection.
HOW RETIREES CAN STOP FAKE DEBT COLLECTOR SCAMS

SEO poisoning is letting hackers hijack Google results targeting user’s data. (Nicolas Economou/NurPhoto via Getty Images)
Kurt’s key takeaway
Hackers are turning Google search into their delivery system for malware. By blending real apps with hidden spyware, they can make almost anyone a victim. The rise of SEO poisoning shows that you cannot rely only on search rankings to stay safe. If you are careful about where you download your apps, you can keep your devices and data out of a hacker’s hands.
CLICK HERE TO GET THE FOX NEWS APP
How much do you trust Google to filter out malicious sites before you click? Let us know by writing to us at Cyberguy.com.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
[ad_2]