NEWYou can now listen to Fox News articles!
We trust Macs to be reliable, secure, and mostly resistant to viruses. Apple’s software reputation has long been built around the idea that macOS is harder to compromise than Windows. And while there is some truth to that, it does not mean that Macs are immune. Modern malware is smarter, more targeted, and often designed to slip past built-in defenses quietly. Recently, I heard from Jeffrey from Phoenix, AZ, who’s been dealing with this exact situation.
“I used a MacBook at work and noticed it was performing oddly. I didn’t use an Apple ID on that machine per company protocol. But I had personal devices that I could work from that are now infected. The notepad, maps, and home, among others, seem to be getting hung up. I’ve tried to advise Apple but have had little success. It’s completely taken over my devices, and I don’t know how to resolve this.”
If your Mac has started acting strange, you are not alone, Jeffrey. Malware infections are more common than many Mac users realize, and spotting them early can make all the difference. Let us break down how to tell if your system is compromised, what protections Apple already provides, and the steps you should take to keep your data safe. If you’re a Windows user facing similar issues, check out our guide: What to do if you think your PC has a virus for step-by-step help.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts, and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM/NEWSLETTER
WHY IPHONE USERS ARE THE NEW PRIME SCAM TARGETS
Mac malware often hides in the background, making it hard to spot at first. (Kurt “CyberGuy” Knutsson)
Signs your Mac might be infected
Spotting malware on macOS is not always straightforward. Many threats are designed to stay hidden, running quietly in the background while collecting data or opening a backdoor for attackers. Still, there are a few red flags that usually signal something is wrong.
One of the first signs is slower performance or frequent overheating. If your Mac suddenly takes a long time to boot, runs hot during light tasks, or lags when performing simple actions, it might be doing more behind the scenes than you realize. Apps that crash or freeze more often than usual are another warning sign. Occasional app failures are normal, but if built-in tools like Safari, Notes, or Mail begin acting unstable, it may point to malicious interference.
It is also worth paying attention to what is happening under the hood. Checking Activity Monitor for unknown processes or unusually high CPU or memory usage can reveal malware that tries to hide itself with random or unfamiliar names. Redirected web traffic is another classic symptom. If your browser takes you to strange websites, shows pop-ups, or installs new extensions you never approved, adware or spyware might already be present.
Finally, unexplained changes to your security settings should always raise suspicion. If you notice your firewall turned off, privacy permissions modified, or login items appearing without your knowledge, something could have gained unauthorized control of your system.
SHAMOS MALWARE TRICKS MAC USERS WITH FAKE FIXES
Strange app behavior, pop-ups, or overheating may signal something’s wrong (Kurt “CyberGuy” Knutsson)
How macOS protects you by default
Apple has built several layers of defense into macOS, many of which run silently in the background to keep your system secure. Knowing how they work can help you understand what protections are already in place and where you might still need to add more safeguards.
Gatekeeper is one of the most important built-in security tools. It checks every app before it runs to make sure it comes from a verified developer, warning or blocking you if the app is not trusted. Another layer of defense is XProtect, Apple’s built-in malware scanner. It updates automatically and can stop many known threats from running, although it is not as thorough as specialized antivirus software.
System Integrity Protection, or SIP, is another important safeguard. It locks down critical system files and processes so that malware cannot tamper with them even if it gains access. macOS also uses sandboxing and strict permission controls to contain threats. Apps run in isolated environments and must explicitly request permission to access sensitive data such as your camera, files, or location.
Together, these features make it significantly harder for malicious software to infect your Mac or cause serious damage. However, they are not perfect. Attackers are constantly developing new techniques to bypass these protections, and many threats rely on human error rather than technical exploits. That is why taking additional precautions is still essential, even on a Mac.
10 WAYS TO SECURE YOUR OLDER MAC FROM THREATS AND MALWARE
Even Apple’s built-in protections can miss new or advanced threats (Kurt “CyberGuy” Knutsson)
What to do if your Mac is already infected
If you find yourself dealing with a Mac that’s already compromised these steps can help you get back in control:
1) Disconnect from the internet immediately
Unplug Ethernet or turn off Wi-Fi and Bluetooth. This prevents malware from sending more data out or pulling in additional malicious code.
2) Back up your important files safely
Use an external drive or cloud service you trust. Avoid copying entire system folders-just grab personal documents, photos, and files you can’t replace. You don’t want to back up the malware along with them.
3) Boot into Safe Mode
Restart your Mac and hold the Shift key. Safe Mode prevents some malware from launching and makes it easier to run cleanup tools.
4) Run a trusted malware removal tool
While macOS includes XProtect, you may need something more powerful. A strong antivirus program can detect and remove infections. Run a full system scan to catch hidden threats.
5 PHONE SETTINGS TO CHANGE RIGHT NOW FOR A SAFER SMARTPHONE
5) Check your login items and Activity Monitor
Review what apps are set to launch at startup and remove anything you don’t recognize. If you spot unfamiliar processes hogging resources, don’t just guess. Use our guides at Cyberguy.com/LockUpYourTech to compare what’s safe and learn how to shut down anything suspicious before it causes more trouble.
6) Consider a clean reinstall of macOS
If malware persists, wiping your system may be the only option. Erase your Mac’s drive and reinstall macOS from scratch. Restore only the clean files you backed up earlier.
7) Secure your other devices
If your iPhone, iPad, or other personal devices are showing strange behavior, run security scans, update their software, and reset key passwords. Malware can sometimes spread through shared Wi-Fi networks, cloud accounts, or files.
8) Reset key passwords and enable two-factor authentication
Even after cleanup, assume some of your data may have been exposed. Update your Apple ID, email, banking, and work accounts with strong, unique passwords. Turn on 2FA wherever possible.
9) Get professional help if needed
If you’re overwhelmed, you can bring your Mac to an Apple Store for in-person help at the Genius Bar, or schedule a free appointment with Apple Support.
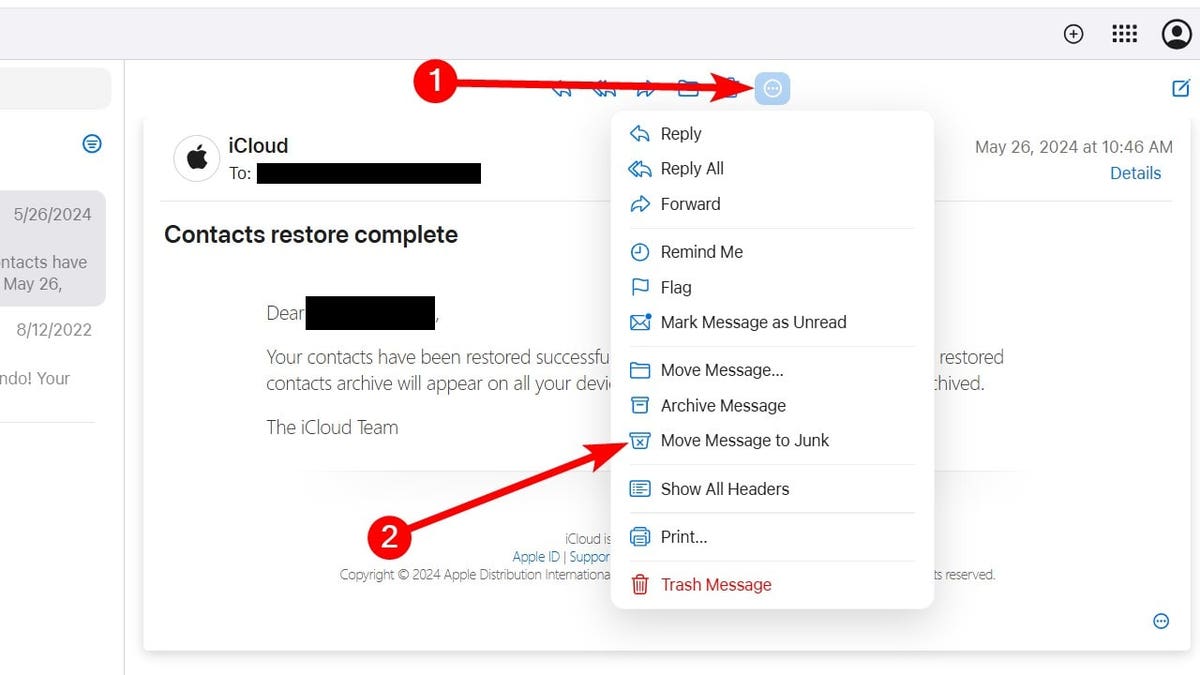
Simple steps like scanning, updating, and using strong passwords can keep your data safe (Kurt “CyberGuy” Knutsson)
7 ways to keep your Mac from getting infected
Some cyber threats do not reveal themselves immediately. Scammers often collect small bits of data over time or wait weeks before trying to use what they have stolen. These steps can help you strengthen your defenses and reduce the chances of future infections.
1) Install strong antivirus software
macOS’s built-in protections are useful but basic. A strong antivirus adds an extra layer by detecting threats in real time, blocking malicious downloads, and even identifying new types of malware before they spread. A strong antivirus also scans email attachments and browser activity, areas where many Mac users are most vulnerable.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android & iOS devices at Cyberguy.com/LockUpYourTech
2) Consider a personal data removal service
Many cyberattacks begin with information freely available online. A data removal service scrubs your personal details from broker sites, reducing the chances of targeted attacks or identity theft. While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com/Delete
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com/FreeScan
GOOGLE FIXES ANOTHER CHROME SECURITY FLAW BEING ACTIVELY EXPLOITED
3) Use a password manager
Many malware attacks rely on stolen credentials rather than technical exploits. A password manager stores unique, complex passwords for every account and can automatically flag weak or reused ones. It also helps protect you from phishing attempts because it will only autofill passwords on legitimate websites.
Next, see if your email has been exposed in past breaches. Our #1 password manager (see Cyberguy.com/Passwords) pick includes a built-in breach scanner that checks whether your email address or passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at Cyberguy.com/Passwords
4) Enable two-factor authentication
Even if someone steals your password, two-factor authentication (2FA) makes it much harder for them to access your accounts. It adds an extra step to the login process, requiring a code from your phone or a security key.
5) Keep macOS and apps updated
Outdated software is a common entry point for malware. Updates often patch vulnerabilities that attackers could exploit, so turning on automatic updates for both macOS and third-party apps is an easy but effective defense.
6) Review login items and background processes
Malware often tries to run at startup so it can operate undetected. Regularly check System Settings to make sure only trusted apps are launching automatically, and use Activity Monitor to investigate anything suspicious.
7) Use identity theft protection
If your personal data has already been exposed, an identity theft protection service can monitor for suspicious activity, alert you to breaches, and help you recover quickly if something does go wrong. Identity Theft companies can monitor personal information like your Social Security Number (SSN), phone number, and email address, and alert you if it is being sold on the dark web or being used to open an account. They can also assist you in freezing your bank and credit card accounts to prevent further unauthorized use by criminals.
See my tips and best picks on how to protect yourself from identity theft at Cyberguy.com/IdentityTheft
CLICK HERE TO GET THE FOX NEWS APP
Kurt’s key takeaway
Macs have a reputation for being safer than other computers, but that does not mean they are untouchable. Malware has evolved to target macOS more aggressively than ever, and many attacks now rely on tricking users rather than breaking through security software. If your device is behaving strangely, taking action early is the best way to prevent deeper damage.
How important is cybersecurity when choosing the devices you use every day? Let us know by writing to us at Cyberguy.com/Contact
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts, and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM/NEWSLETTER
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt “CyberGuy” Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on “FOX & Friends.” Got a tech question? Get Kurt’s free CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.