[ad_1]
While driving to a new restaurant, your car’s satellite navigation system tracks your location and guides you to the destination. Onboard cameras constantly track your face and eye movements. When another car veers into your path, forcing you to slam on the brakes, sensors are assisting and recording. Waiting at a stoplight, the car notices when you unbuckle your seat belt to grab your sunglasses in the backseat.
Modern cars are computers on wheels that are becoming increasingly connected, enabling innovative new features that make driving safer and more convenient. But these systems are also collecting reams of data on our driving habits and other personal information, raising concerns about data privacy.
Here is what to know about how your car spies on you and how you can minimize it:
How cars collect data
It’s hard to figure out exactly how much data a modern car is collecting on you, according to the Mozilla Foundation, which analyzed privacy practices at 25 auto brands in 2023. It declared that cars were the worst product category that the group had ever reviewed for privacy.
AP AUDIO: One Tech Tip: Modern cars are spying on you. Here’s what you can do about it
Modern cars are spying on you. AP’s Kelvin Chan reports.
The data points include all your normal interactions with the car — such as turning the steering wheel or unlocking doors — but also data from connected onboard services, like satellite radio, GPS navigation systems, connected devices, telematics systems as well as data from sensors or cameras.
Vehicle telematics systems started to become commonplace about a decade ago, and the practice of automotive data collection took off about five years ago.
The problem is not just that data is being collected but who it’s provided to, including insurers, marketing companies and shadowy data brokers. The issue surfaced earlier this year when General Motors was banned for five years from disclosing data collected from drivers to consumer reporting agencies.
The Federal Trade Commission accused GM of not getting consent before sharing the data, which included every instance when a driver was speeding or driving late at night. It was ultimately provided to insurance companies that used it to set their rates.
Be aware
The first thing drivers should do is be aware of what data their car is collecting, said Andrea Amico, founder of Privacy4Cars, an automotive privacy company.
In an ideal world, drivers would read through the instruction manuals and documentation that comes with their cars, and quiz the dealership about what’s being collected.
But it’s not always practical to do this, and manufacturers don’t always make it easy to find out, while dealership staff aren’t always the best informed, Amico said.
Privacy4Cars offers a free auto privacy labeling service at vehicleprivacyreport.com that can summarize what your car could be tracking.
Owners can punch in their car’s Vehicle Identification Number, which then pulls up the automaker’s data privacy practices, such as whether the car collects location data and whether it’s given to insurers, data brokers or law enforcement.
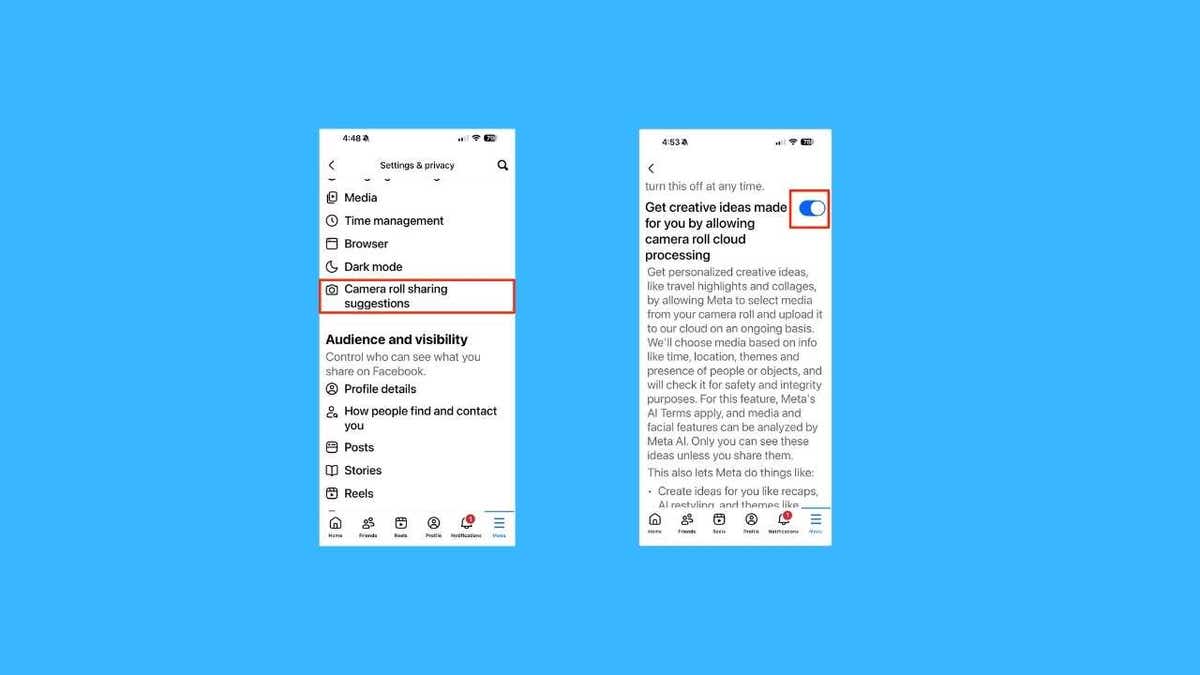
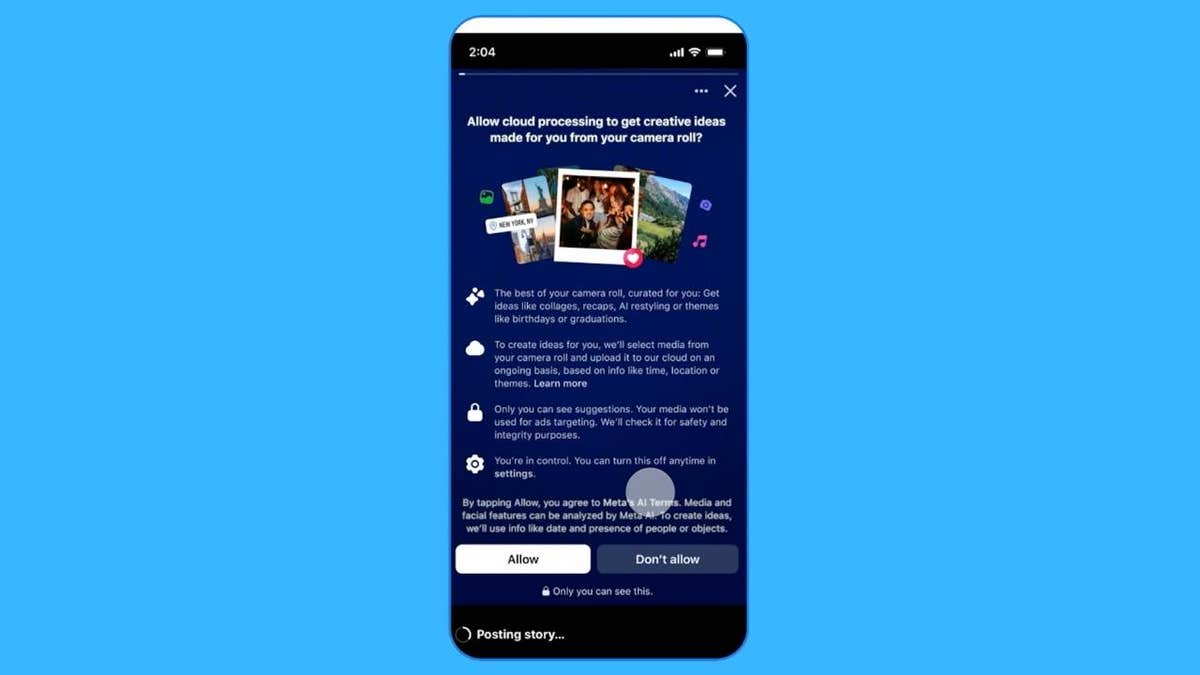
Tweak your settings
Data collection and tracking start as soon as you drive a new car off the dealership lot, with drivers unwittingly consenting when they’re confronted with warning menus on dashboard touch screens.
Experts say that some of the data collection is baked into the system, you can revoke your consent by going back into the menus.
“There are permissions in your settings that you can make choices about,” said Lauren Hendry Parsons of Mozilla. “Go through on a granular level and look at those settings where you can.”
For example, Toyota says on its website that drivers can decline what it calls “Master Data Consent” through the Toyota app. Ford says owners can opt to stop sharing vehicle data with the company by going through the dashboard settings menu or on the FordPass app.
BMW says privacy settings can be adjusted through the infotainment system, “on a spectrum between” allowing all services including analysis data and none at all.
You can opt out
…
Drivers in the U.S. can ask carmakers to restrict what they do with their data.
Under state privacy laws, some carmakers allow owners across the United States to submit requests to limit the use of their personal data, opt out of sharing it, or delete it, Consumer Reports says. Other auto companies limit the requests to people in states with applicable privacy laws, the publication says.
You can file a request either through an online form or the carmaker’s mobile app.
You can also go through Privacy4Cars, which provides a free online service that streamlines the process. It can either point car owners to their automaker’s request portal or file a submission on behalf of owners in the U.S., Canada, the European Union, Britain and Australia.
… but there will be trade-offs
Experts warn that there’s usually a trade-off if you decide to switch off data collection.
Most people, for example, have switched to satellite navigation systems over paper maps because it’s “worth the convenience of being able to get from point A to point B really easily,” said Hendry Parsons.
Turning off location tracking could also halt features like roadside assistance or disable smartphone app features like remote door locking, Consumer Reports says.
BMW advises that if an owner opts to have no data shared at all, “their vehicle will behave like a smartphone in flight mode and will not transmit any data to the BMW back end.”
When selling your car
When the time comes to sell your car or trade it in for a newer model, it’s no longer as simple as handing over the keys and signing over some paperwork.
If you’ve got a newer car, experts say you should always do a factory reset to wipe all the data, which will also include removing any smartphone connections.
And don’t forget to notify the manufacturer about the change of ownership.
Amico said that’s important because if you trade in your vehicle, you don’t want insurers to associate it with your profile if the dealer is letting customers take it for test drives.
“Now your record may be affected by somebody else’s driving — a complete stranger that you have no relationship with.”
____
Is there a tech topic that you think needs explaining? Write to us at [email protected] with your suggestions for future editions of One Tech Tip.
___
This story has been corrected to show that the Mozilla representative’s first name is Lauren, not Laura.
[ad_2]