NEWYou can now listen to Fox News articles!
You might have recently noticed a wave of cyberattacks hitting companies whose services millions of Americans rely on every day. Among the victims are Google, Farmers Insurance, Allianz Life, Workday, Pandora, Cisco, Chanel and Qantas, all reporting breaches linked to Salesforce-connected applications.
Now, credit reporting firm TransUnion has confirmed its own major incident, with more than 4.4 million U.S. consumers affected. Attackers exploited weaknesses in third-party integrations, not Salesforce itself. Security researchers tie this technique to the extortion group ShinyHunters and its affiliated crews.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM/NEWSLETTER.
SCAMMERS ARE USING DOCUSIGN EMAILS TO PUSH APPLE PAY FRAUD
Hackers stole 13 million records, exposing data of 4.4 million Americans in the latest TransUnion cyberattack. (Christopher Dilts/Bloomberg)
What you need to know about the TransUnion data breach
TransUnion has disclosed a major data breach that impacted 4,461,511 individuals in the United States, according to a filing with the Maine Attorney General’s Office. The incident occurred on July 28, 2025, and was discovered two days later on July 30.
The breach resulted from unauthorized access to a third-party application used in TransUnion’s U.S. consumer support operations. The company stressed that its core credit database and credit reports were not compromised.
Although TransUnion characterized the exposed information as “limited,” the stolen data is highly sensitive. It includes names, dates of birth, Social Security numbers, billing addresses, email addresses, phone numbers, reasons for customer transactions (such as requests for a free credit report), and customer support tickets and messages.
Hackers claim they stole more than 13 million records in total, with about 4.4 million tied to U.S. consumers.
In response, TransUnion is providing all affected individuals with 24 months of free credit monitoring and identity theft protection services.
FARMERS INSURANCE DATA BREACH EXPOSES 1.1M AMERICANS
The breach at TransUnion follows several similar cyberattacks against tech companies, including Google and Cisco, and retail brands, such as Chanel and Adidas. (Mike Kemp/In Pictures)
Hackers target companies through Salesforce apps
The breach appears to be part of a broader wave of Salesforce-related attacks that is hitting organizations across sectors, from tech and finance to retail and aviation. Alongside Google, Farmers Insurance, Allianz Life, Workday, Pandora, Cisco, Chanel and Qantas, brands like Adidas, Louis Vuitton, Dior, Tiffany & Co., Cartier and Air France-KLM have also reported incidents tied to weaknesses in Salesforce-linked applications.
In most cases, attackers exploited malicious third-party integrations or OAuth-connected apps disguised as legitimate Salesforce tools to siphon sensitive records. This technique bypassed traditional login protections and gave intruders long-lasting access to customer relationship management data. The stolen information ranges from basic contact details and business notes to highly sensitive identifiers such as Social Security numbers, dates of birth and driver’s license information.
Researchers say these intrusions align with activity from the extortion group ShinyHunters, with some overlap in tactics and infrastructure linked to other threat actors like Scattered Spider. Campaigns tracked under names such as UNC6395 and UNC6040 point to a larger “extortion-as-a-service” model, where criminal crews collaborate and share stolen data across underground forums.
TransUnion’s response
CyberGuy reached out to TransUnion for a comment and received the following response:
“TransUnion recently experienced a cyber incident that affected a third-party application serving our U.S. consumer support operations. Upon discovery, we quickly contained the issue, which did not involve our core credit database or include credit reports.
The incident involved unauthorized access to limited personal information for a very small percentage of U.S. consumers. We are working with law enforcement and have engaged third-party cybersecurity experts for an independent forensics review. Additionally, we will notify affected consumers and provide credit monitoring services.”
As for the gap between when the breach occurred (July 28, 2025) and when it was officially recorded as “discovered” (July 30, 2025), a TransUnion spokesperson clarified that the company “identified and contained this event within hours” of it happening, but that it is common industry practice to designate a later “date of discovery” to reflect a more complete assessment following the initial response.
MARY KAY’S ICONIC PINK CADILLAC SHIFTS TO FULLY ELECTRIC
Researchers have linked the latest cybercrimes to extortion group ShinyHunters and its affiliated crews. (Kurt “CyberGuy” Knutsson)
8 ways you can stay safe from the TransUnion data breach
The TransUnion breach exposed millions of people’s data, but there are steps you can take to protect yourself. Here are eight ways to stay safe.
1) Delete personal data that puts you at risk
Go through old online accounts, shopping profiles or cloud storage that may still hold sensitive data. Deleting what you no longer use reduces the amount of information that could be stolen in future breaches or sold on dark web forums. You can also get help from a data removal service.
While no service promises to remove all your data from the internet, having a removal service is great if you want to constantly monitor and automate the process of removing your information from hundreds of sites continuously over a longer period of time.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com/Delete.
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com/FreeScan.
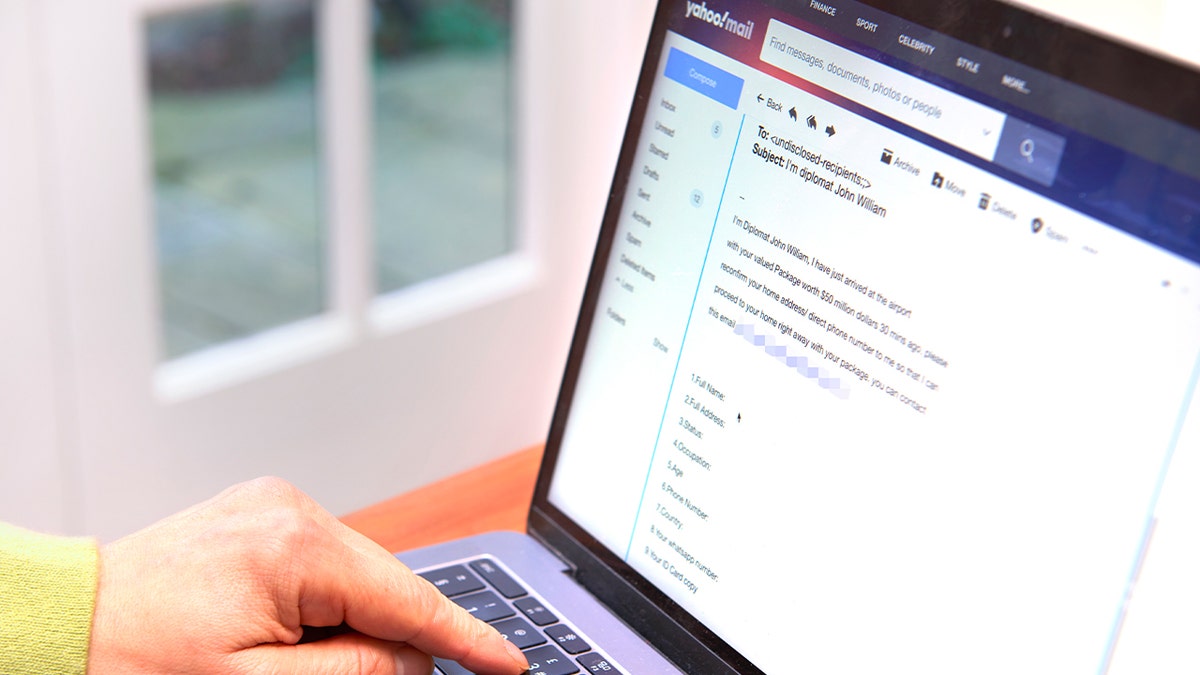
2) Avoid phishing scams and use strong antivirus software
Data stolen in breaches often ends up fueling phishing campaigns. Attackers may use your name, email or phone number to make messages look more convincing. If you get an email or text claiming to be from TransUnion, your bank or any service asking you to “verify” details, don’t click on the link. Instead, log in through the official website or call customer service directly.
The best way to safeguard yourself from malicious links is to have antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android & iOS devices at Cyberguy.com/LockUpYourTech.
3) Save passwords securely
If your login details were exposed, reusing the same password across sites puts multiple accounts at risk. Use a password manager to create and store strong, unique passwords for every service. Even if hackers get hold of one, they won’t be able to use it elsewhere. Consider using a password manager to generate and store complex passwords.
Next, see if your passwords have been exposed in past breaches. Our No. 1 password manager (see Cyberguy.com/Passwords) pick includes a built-in breach scanner that checks whether your passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at Cyberguy.com/Passwords.
HACKERS FOUND A WAY TO TURN OFF WINDOWS DEFENDER REMOTELY
4) Turn on two-factor authentication
Two-factor authentication (2FA) adds a critical extra step beyond just a password. If someone tries to break into your email, banking app or social media account, they’ll also need the one-time code from your authenticator app or text message. This makes stolen credentials much less useful.
5) Keep your devices updated
Hackers often rely on outdated software to spread malware or steal information. Installing the latest updates for your phone, computer and apps ensures security patches are in place, blocking known vulnerabilities that attackers might exploit.
6) Freeze your credit right away
One of the biggest risks after a breach is criminals opening new loans or credit cards in your name. A credit freeze with all three major bureaus, TransUnion, Equifax and Experian, prevents anyone from accessing your credit file without your approval. It’s free and can be temporarily lifted if you need to apply for credit.
7) Monitor your accounts regularly
Watch your bank and credit card statements for unfamiliar charges, no matter how small. Set up transaction alerts where available. You should also pull your free annual credit report to check for unauthorized accounts or inquiries, which could be signs of fraud.
8) Consider identity theft protection services
If your Social Security number, driver’s license or other sensitive identifiers were exposed, you may want to sign up for an identity theft protection service. These services monitor credit reports, dark web forums and financial activity for signs of misuse. Some also include insurance or recovery assistance if your identity is stolen, giving you added peace of mind beyond basic credit monitoring. If you’re one of the affected TransUnion users, make use of the 24 months of free credit monitoring and identity theft protection services. If not, you might get one yourself for the future.
See my tips and best picks on how to protect yourself from identity theft at Cyberguy.com/IdentityTheft.
CLICK HERE TO GET THE FOX NEWS APP
Kurt’s key takeaway
The reality is that the TransUnion breach isn’t just about stolen names and numbers. It’s about how exposed ordinary people are when a single company holds the keys to their financial identity. For years, consumers have had little choice but to trust credit bureaus they never opted into.
Should companies like TransUnion be held legally accountable when millions of people are exposed to fraud? Let us know by writing to us at Cyberguy.com/Contact.
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide — free when you join my CYBERGUY.COM/NEWSLETTER.
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt “CyberGuy” Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on “FOX & Friends.” Got a tech question? Get Kurt’s free CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.