[ad_1]
Read this guide to learn how to set up self-service password reset for Active Directory users.
Step 0: Review Problem Background and Overview
Whenever users need to change their Active Directory password, they call the Service Desk team. This is time-consuming and unsustainable.
So, your manager asked you to configure a tool that allows users to change their passwords.
I will walk you through the steps to complete this task in this guide.
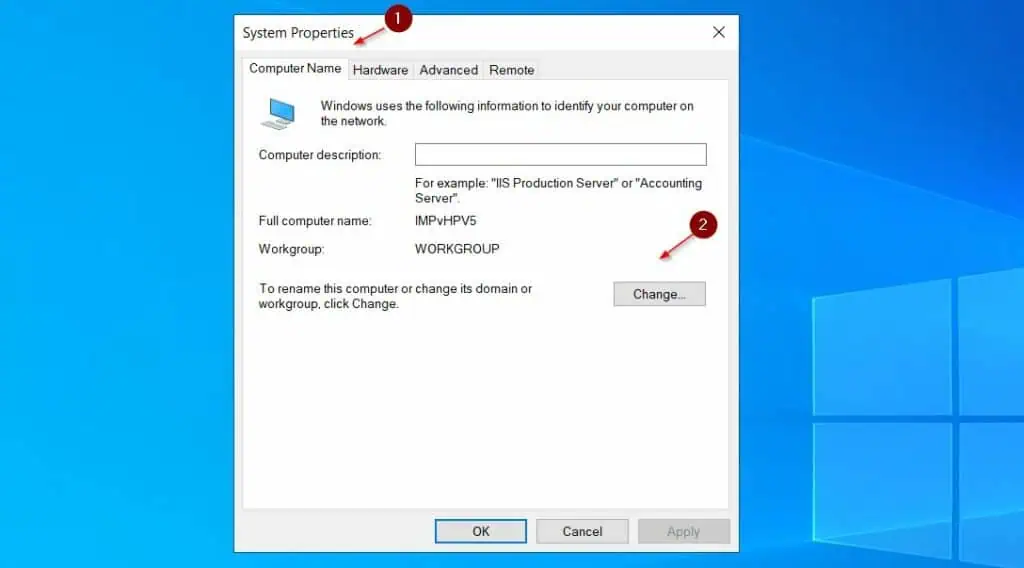
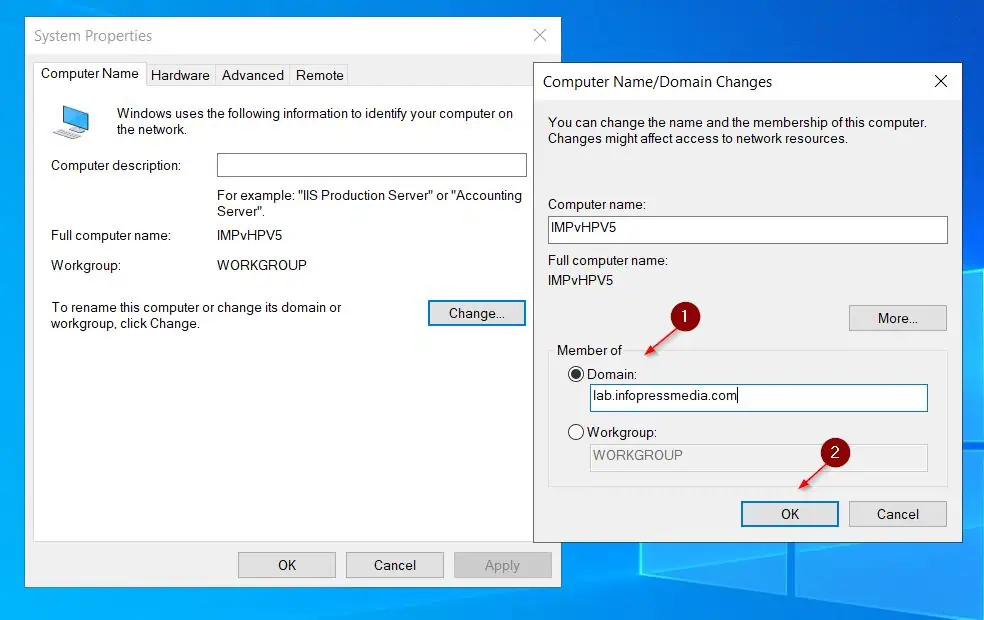
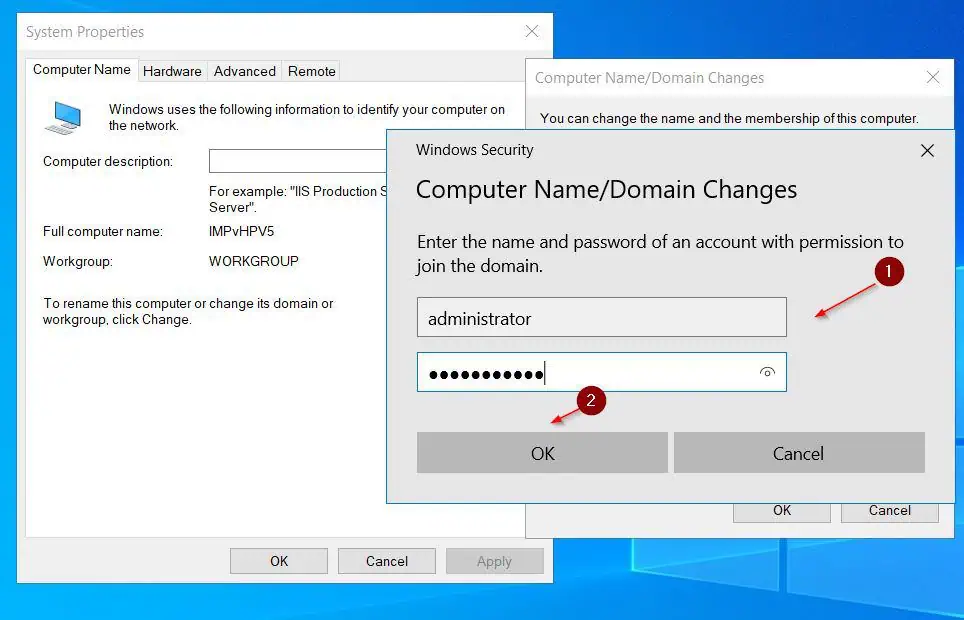
I’m using a Windows Server 2022 Standard server for my test configuration. The server must be a member of the domain, and you must sign in to it with your domain credentials.
Step 1: Install Remote Desktop Web Access and IIS Web Server
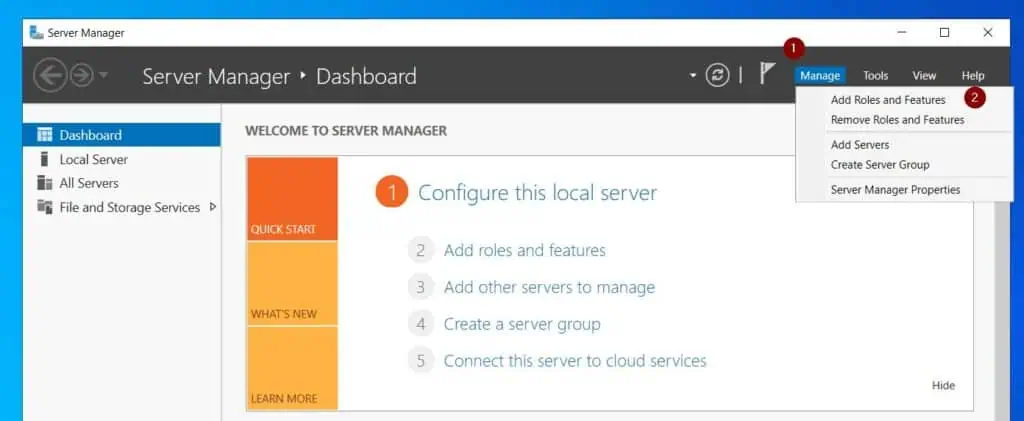
- From the Server Manager Manage menu, select Add Roles and Features.
- When the Add Roles and Features wizard opens, click Next until you get to the Server Roles page. Then, check Remote Desktop Services and Web Server (IIS). When you check Web Server (IIS), the wizard dispays a pop-up, select Add Features in the pop-up.
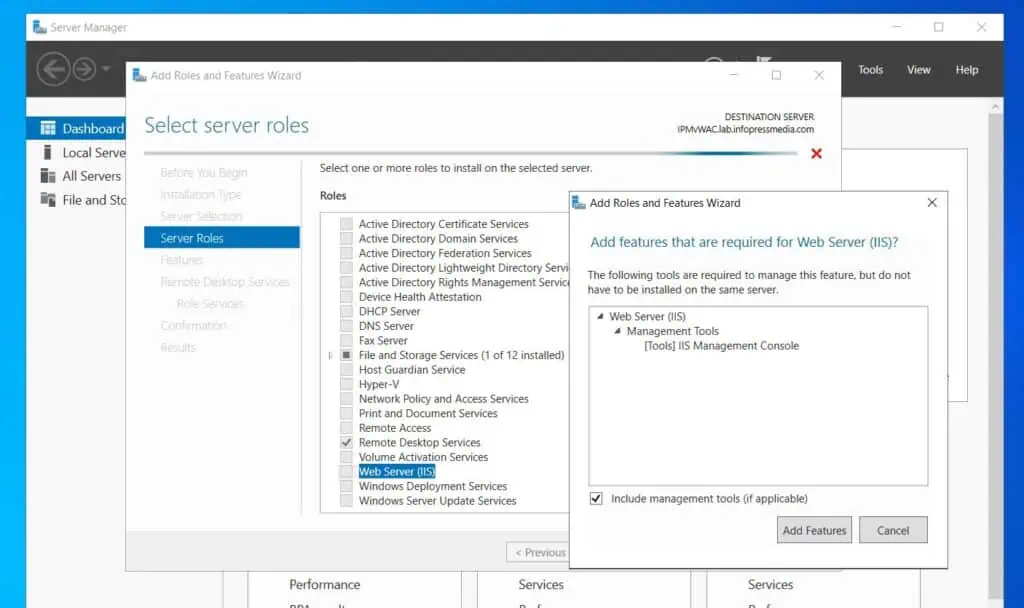
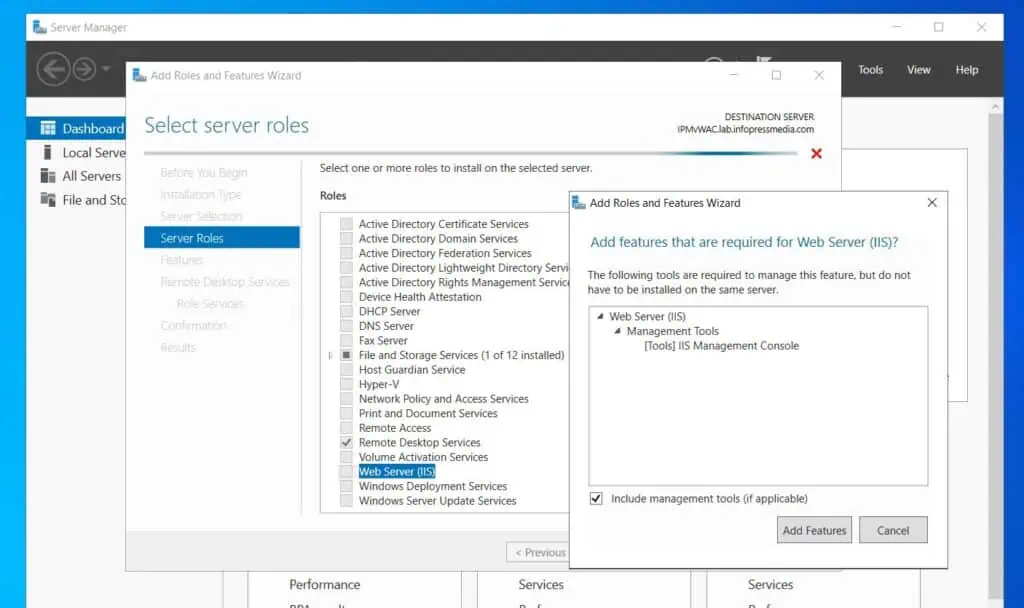
- Confirm that the two roles are checked. Then, click Next.


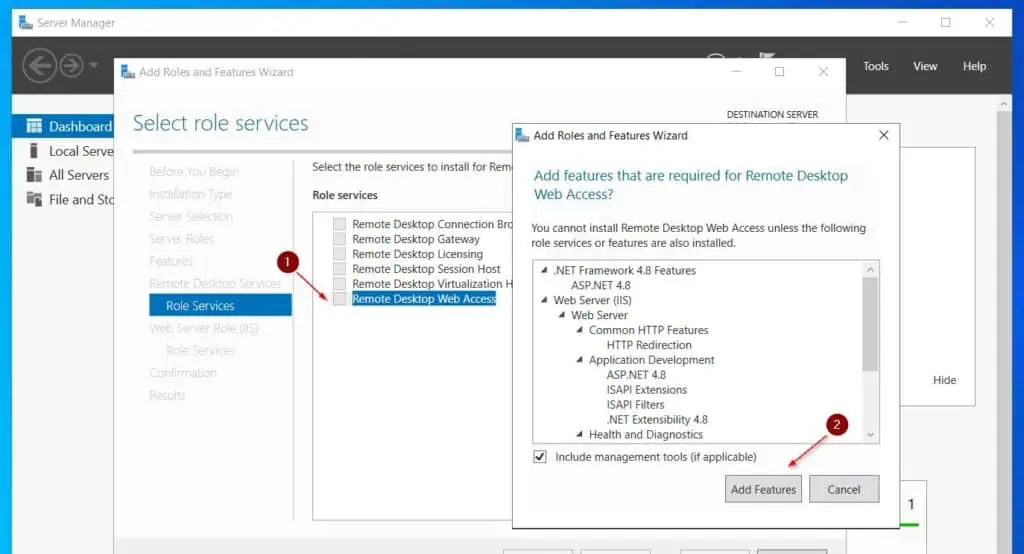
- Continue clicking Next until you get to Remote Desktop Services Role Services. Check Remote Desktop Web Services, then, click the Add Features button in the pop-up.
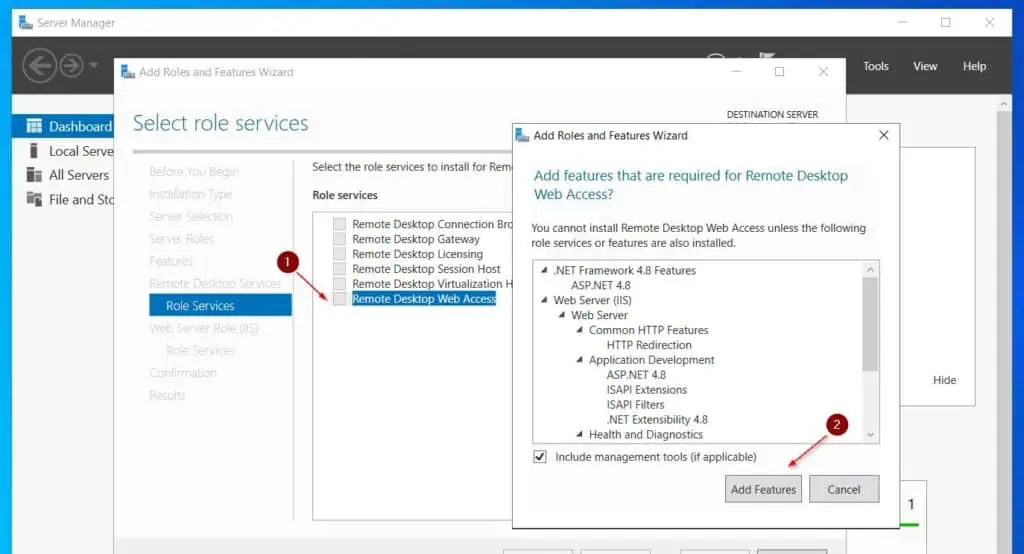
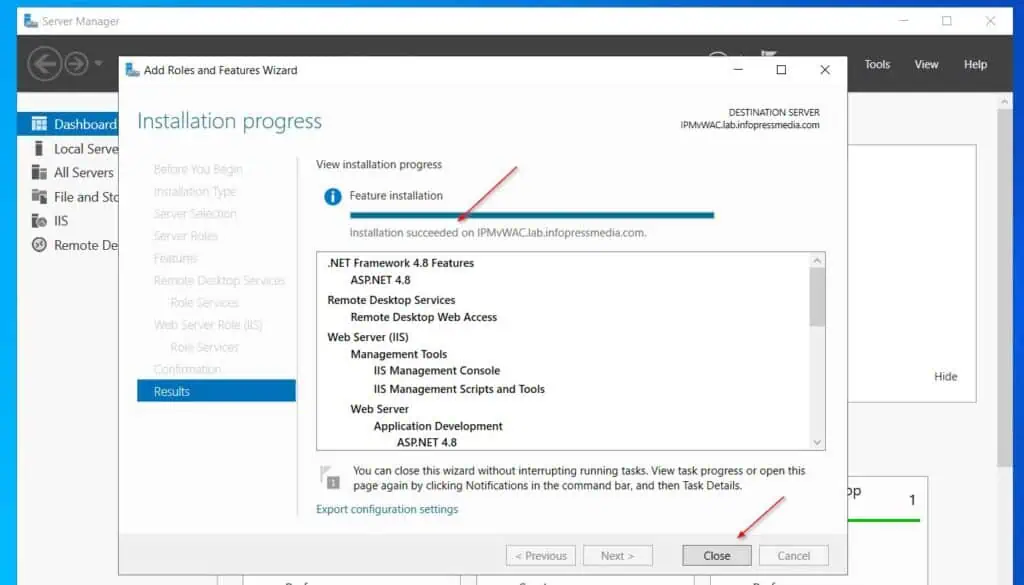
- After that, click Next several times until you get to the Confirmation page. Click Install to install the Windows Server roles.
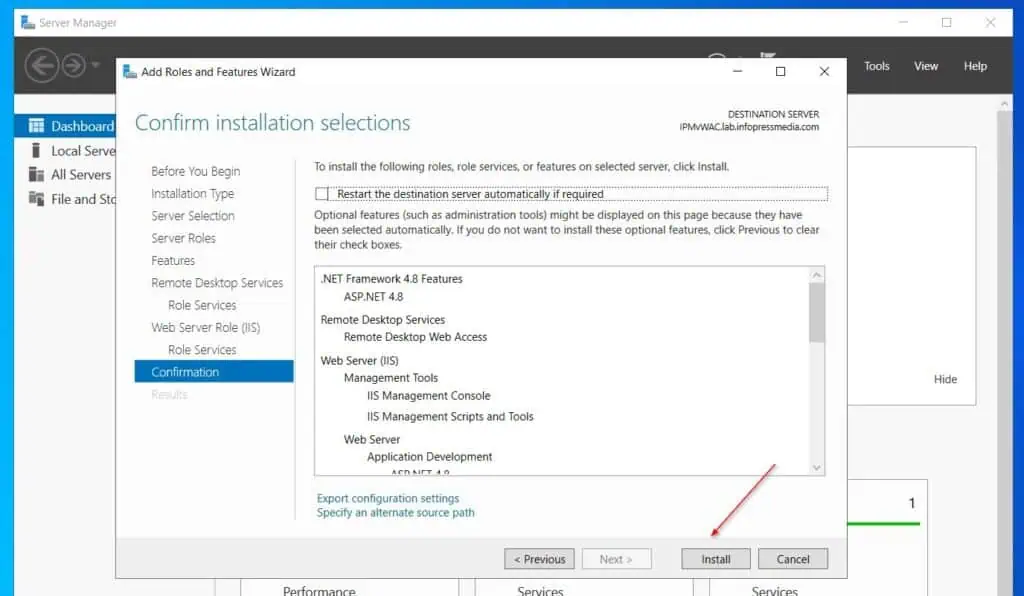
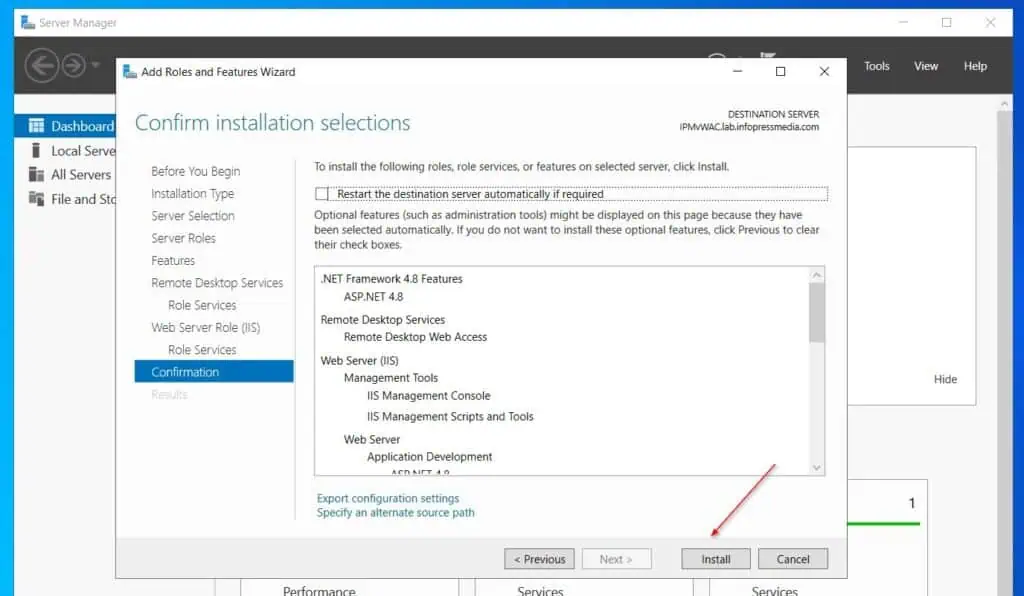
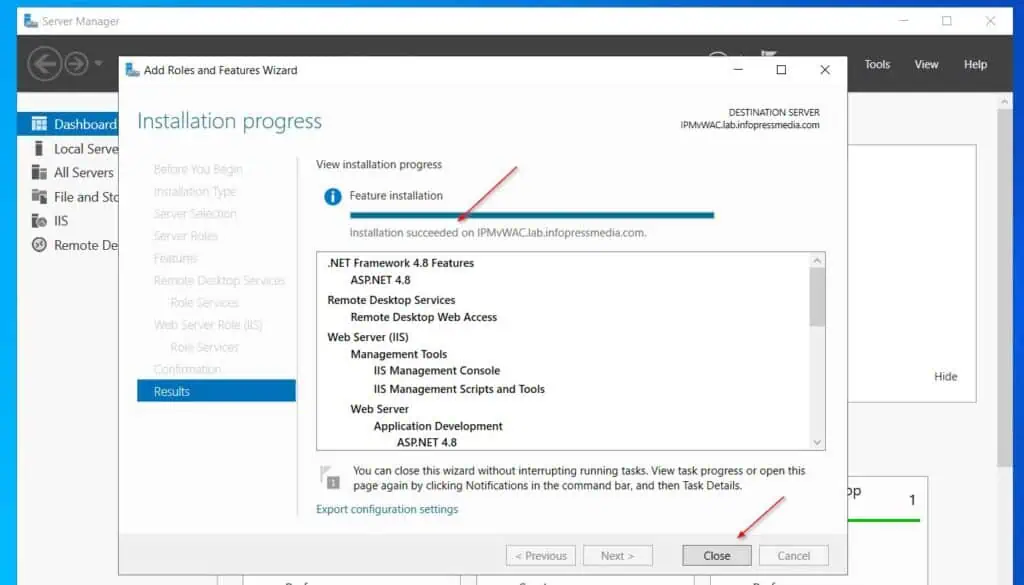
- Wait for the wizard to confirm that the roles have installed successfully, the close it.
Step 2: Enable the Password Reset Feature in IIS RDWeb
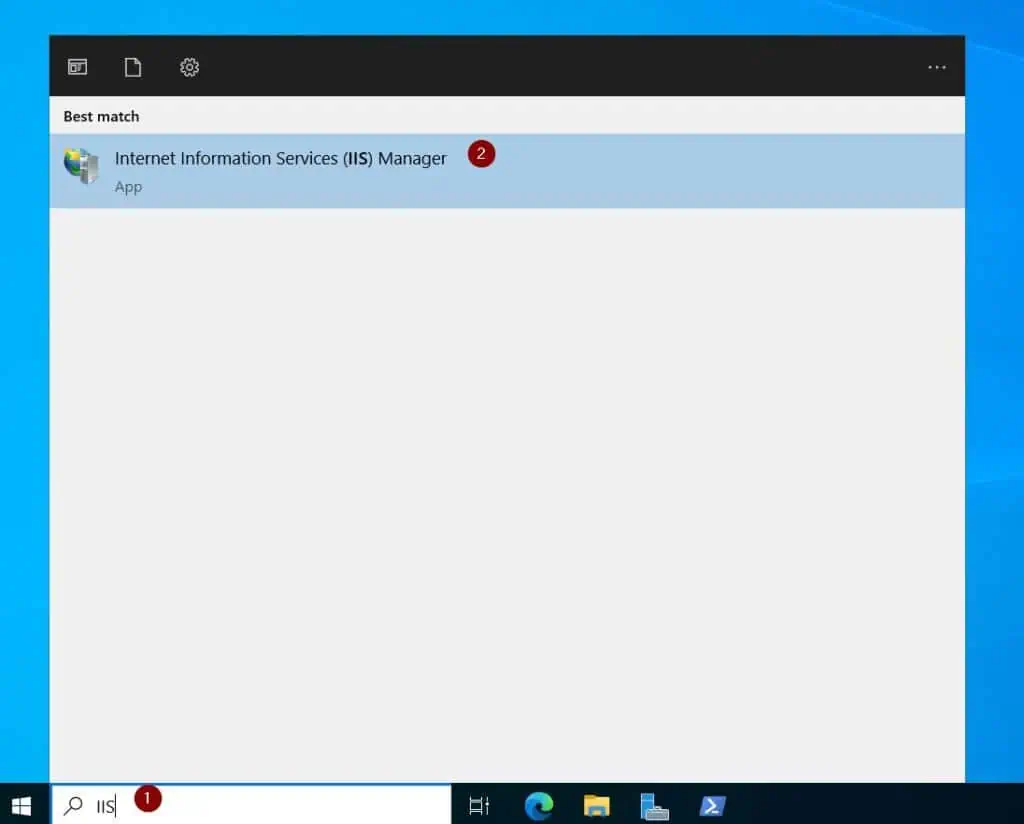
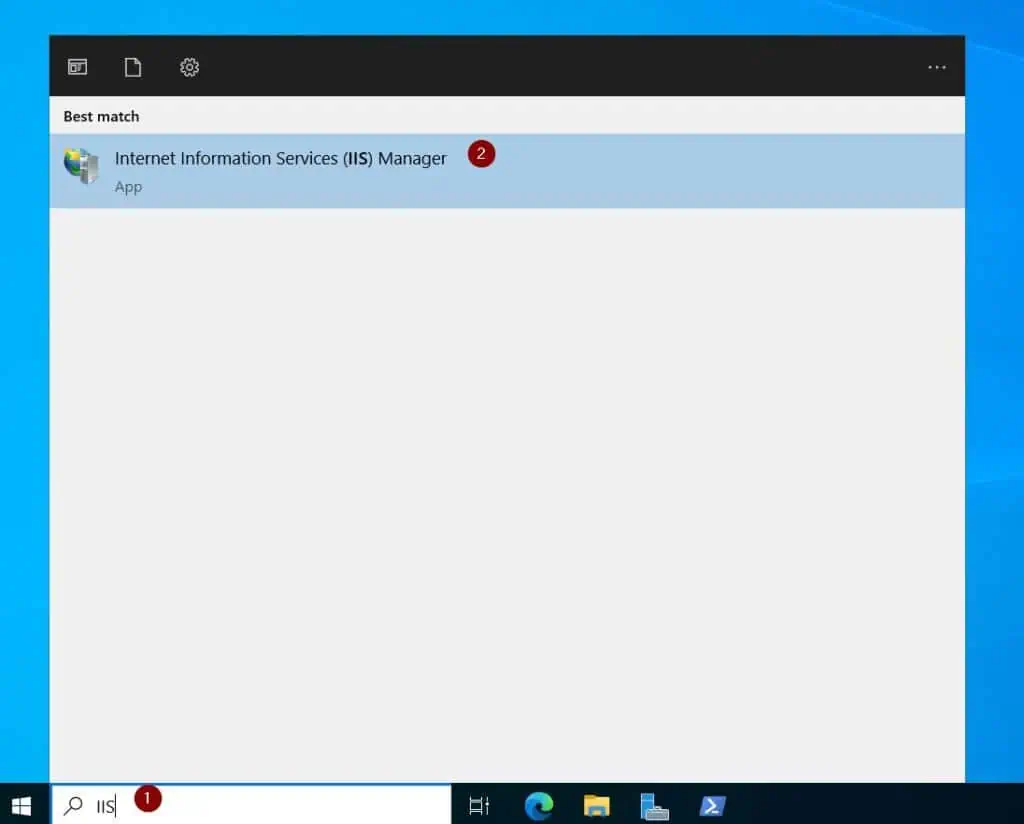
- Search for and open IIS.
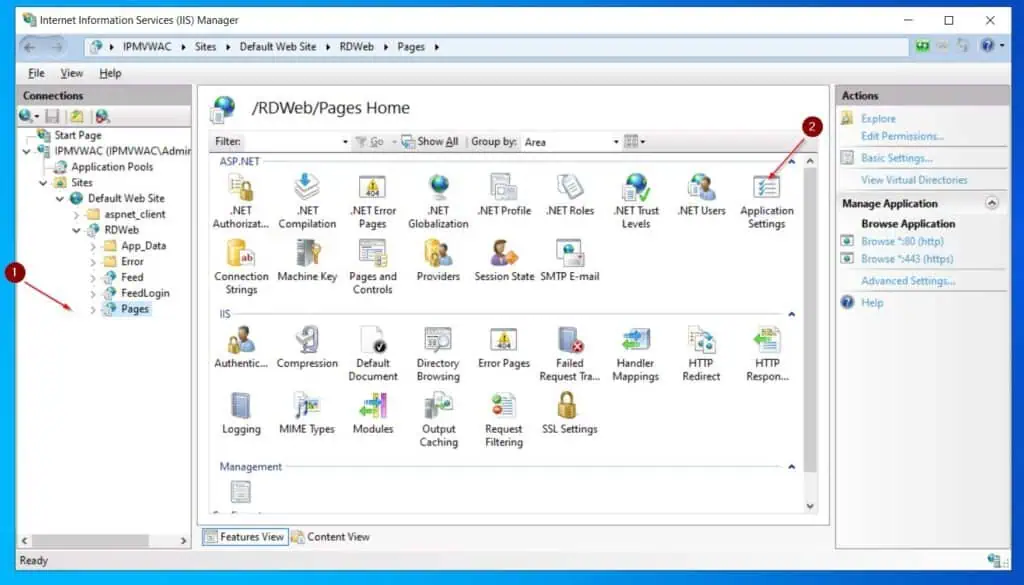
- In the IIS Manager, expand the Server name, then navigate to Sites > Default Web Site > RDWeb and left-click Pages. On the details pane, double-click Application Settings.
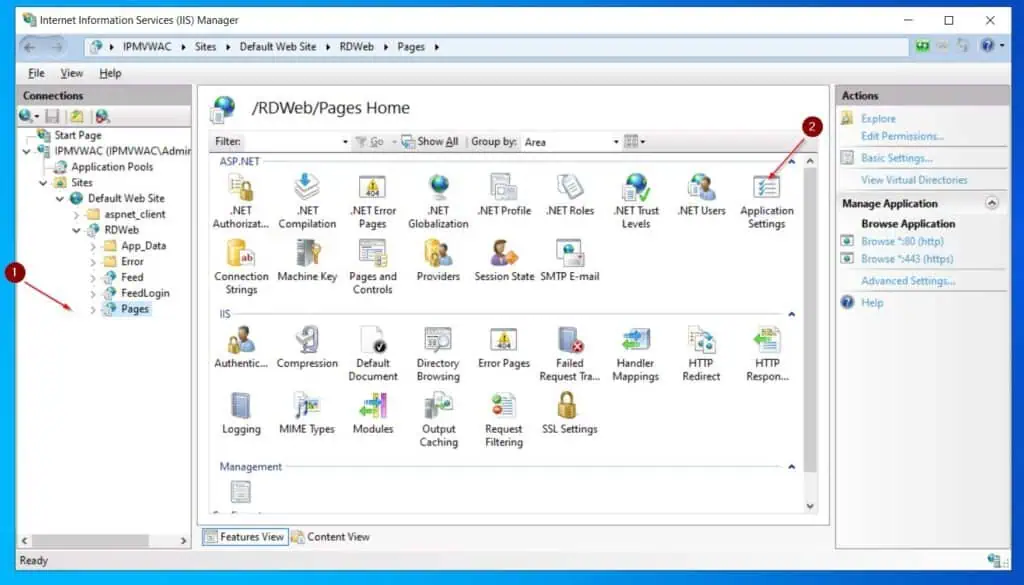
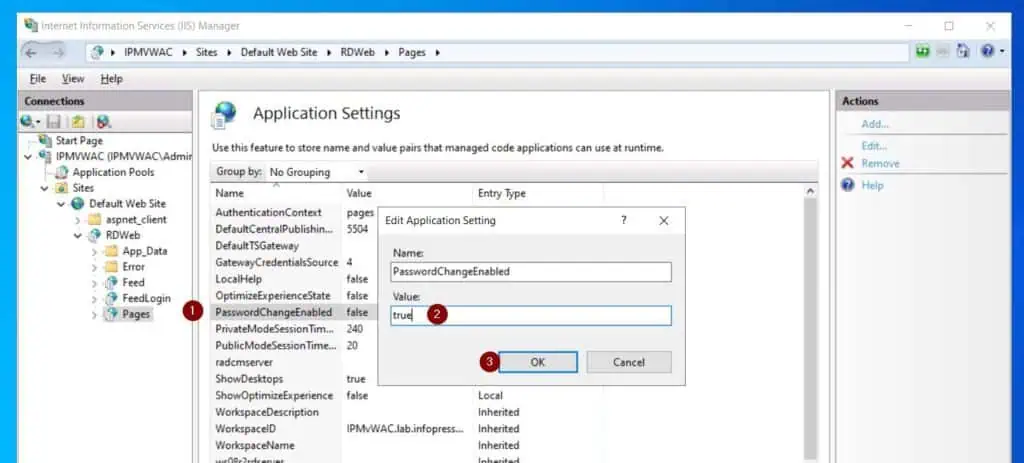
- On the Application Settings page, double-click PasswordChangeEnabled and change its Value from false to true.
Step 3: Configure HTTPS Binding in the Remote Desktop Web Site
By default, the Remote Desktop Web Site in IIS is configured to use HTTPS. Meanwhile, to use HTTPS, you require a certificate.
If you’re configuring self-service password reset for production use, I recommend purchasing a publicly signed certificate from a certificate authority.
Since I am configuring mine for test purposes, I will be creating and using a self-signed certificate.
Task 3.1: Create a Self-signed Certificate
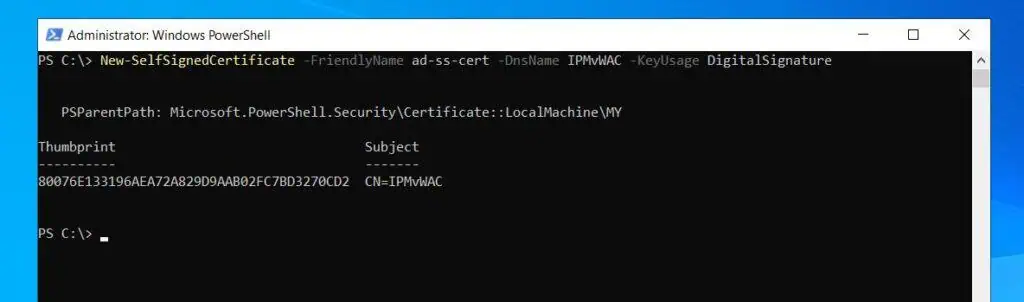
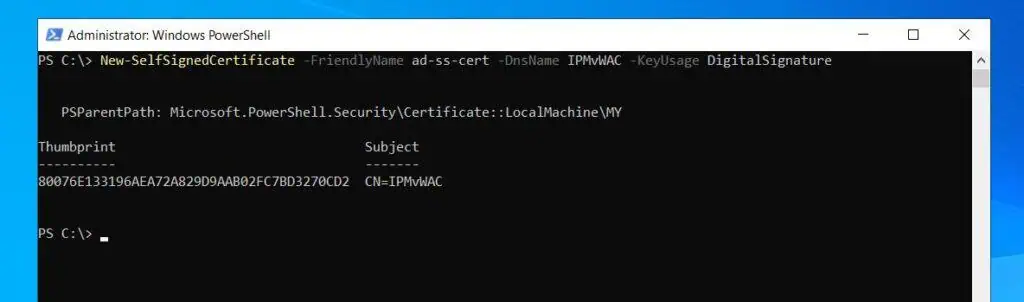
Open PowerShell as an administrator and run the command below to create a self-signed certificate.
Change the Dnsname, IPMvWAC, to your server name.
New-SelfSignedCertificate -FriendlyName ad-ss-cert -DnsName IPMvWAC -KeyUsage DigitalSignature
Task 3.2: Configure IIS HTTPS Binding to use the Certificate
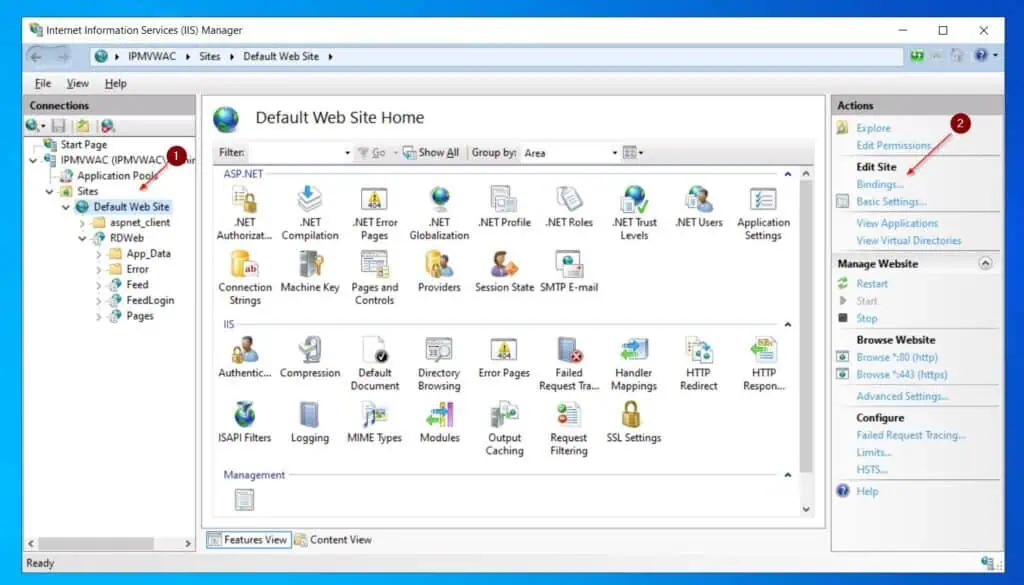
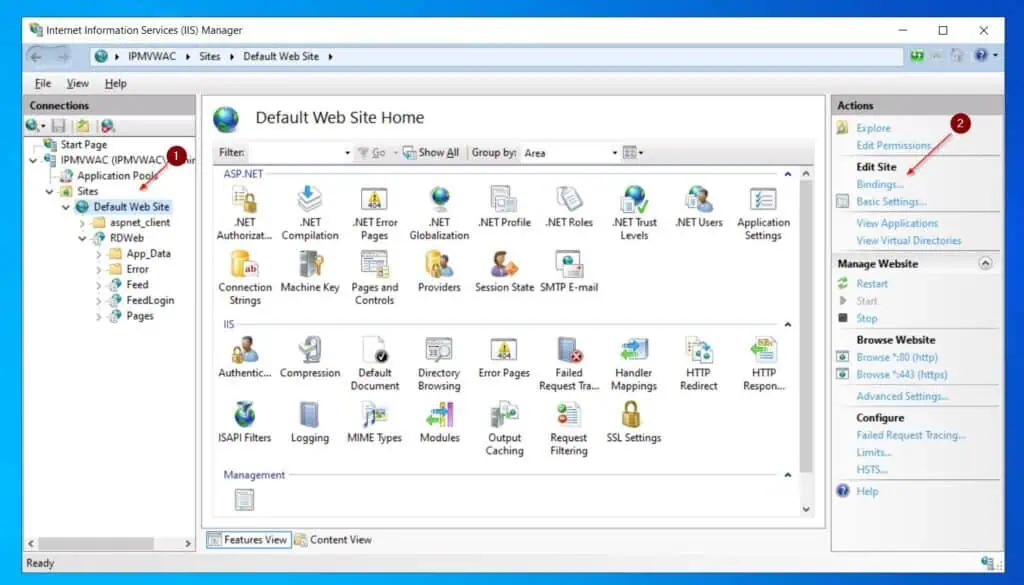
- Back in the IIS Manager, left-click Default Web Site, then in the Actions menu, select Bindings.
- Then, on the Site Bindings pop-up, left-click https and then Edit.
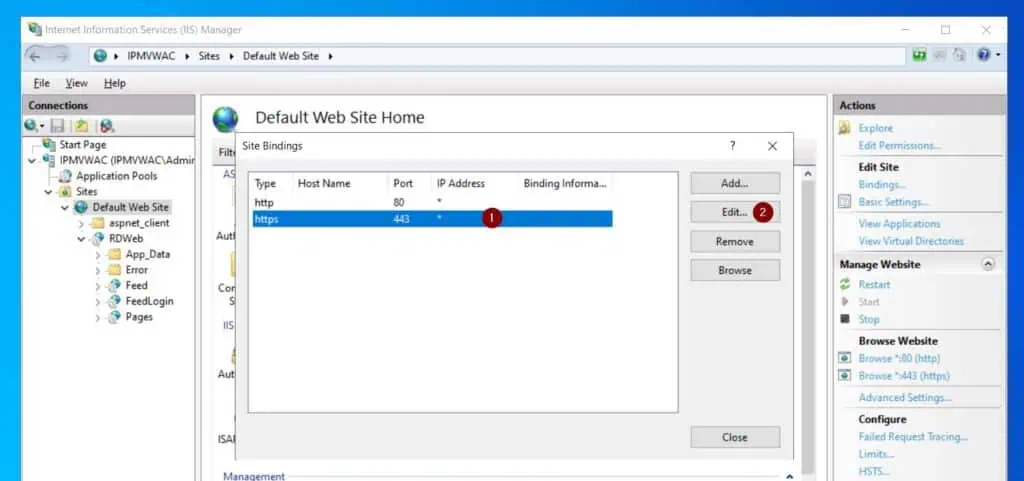
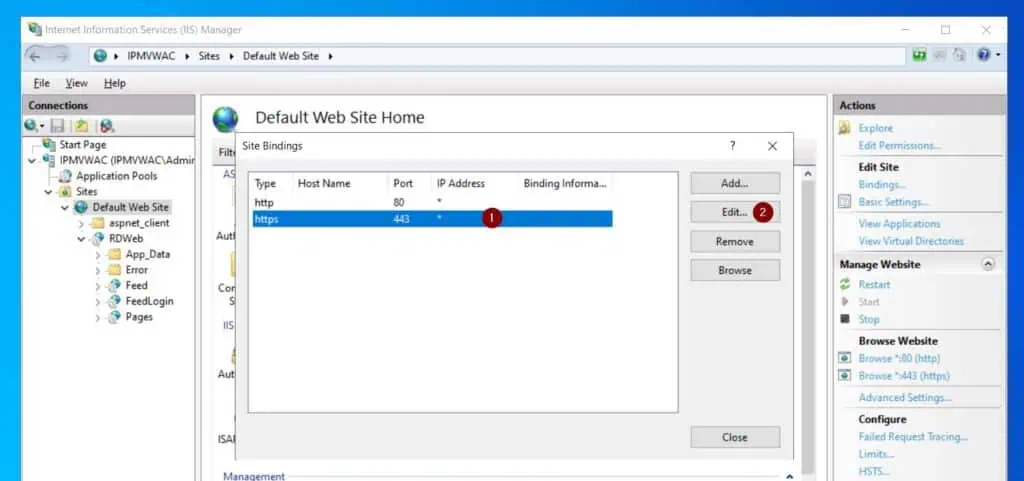
- Finally, on the Edit Site Bindings pop-up, select the self-signed certificate from the SSL Certificate drop-down and click OK. If you receive a confirmation pop-up, select yes.


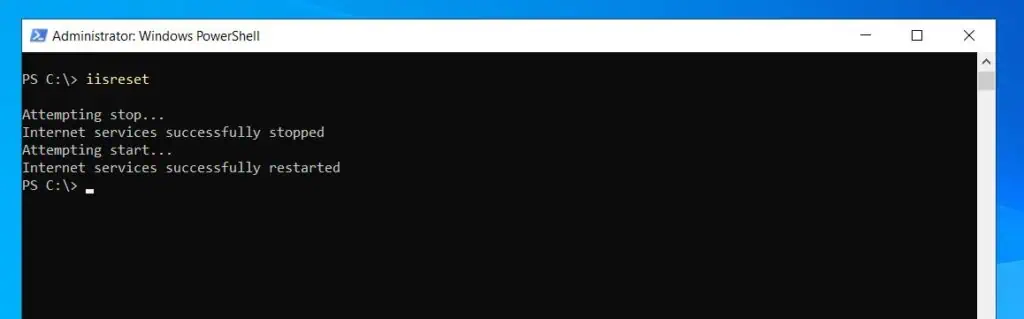
- Return to the PowerShell console and run the iisreset command.
Step 4: Test the Self-service Password Change Remote Desktop Web Site
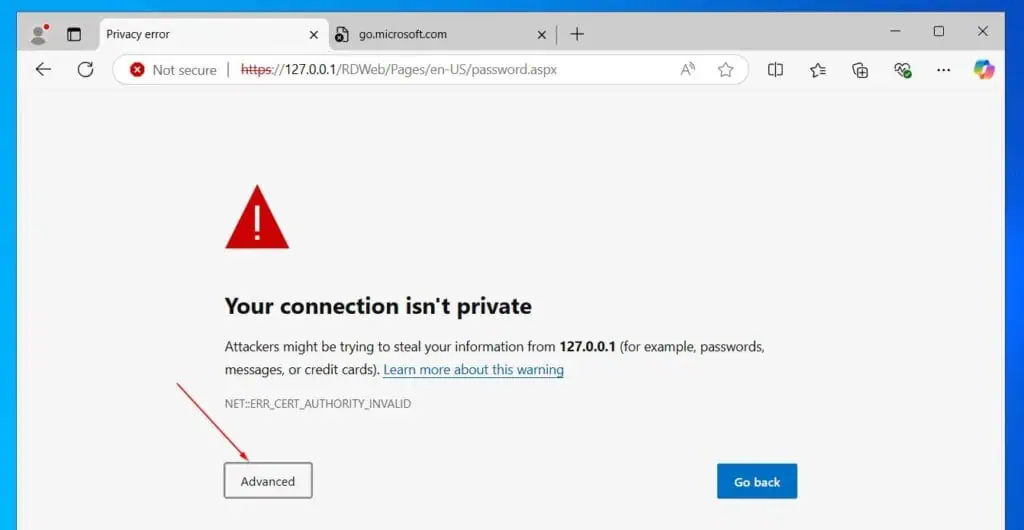
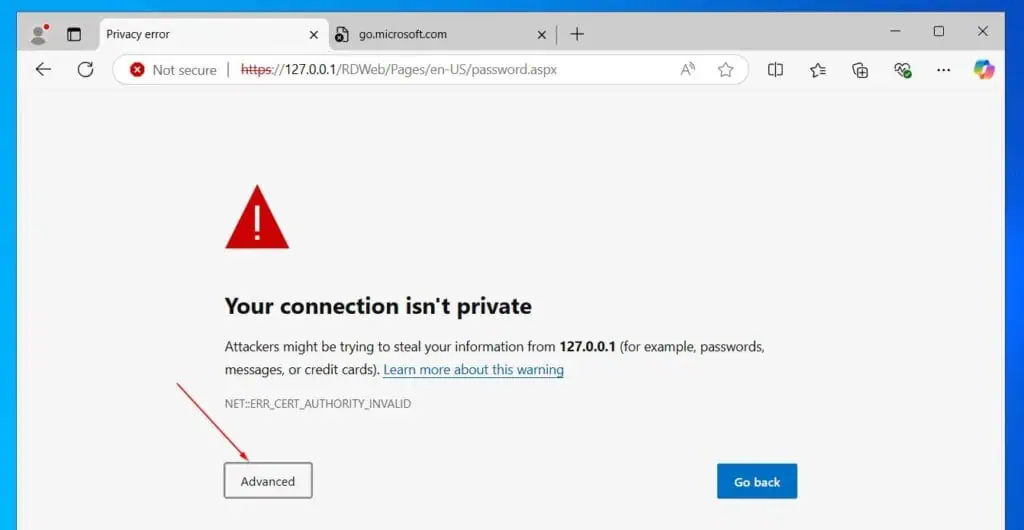
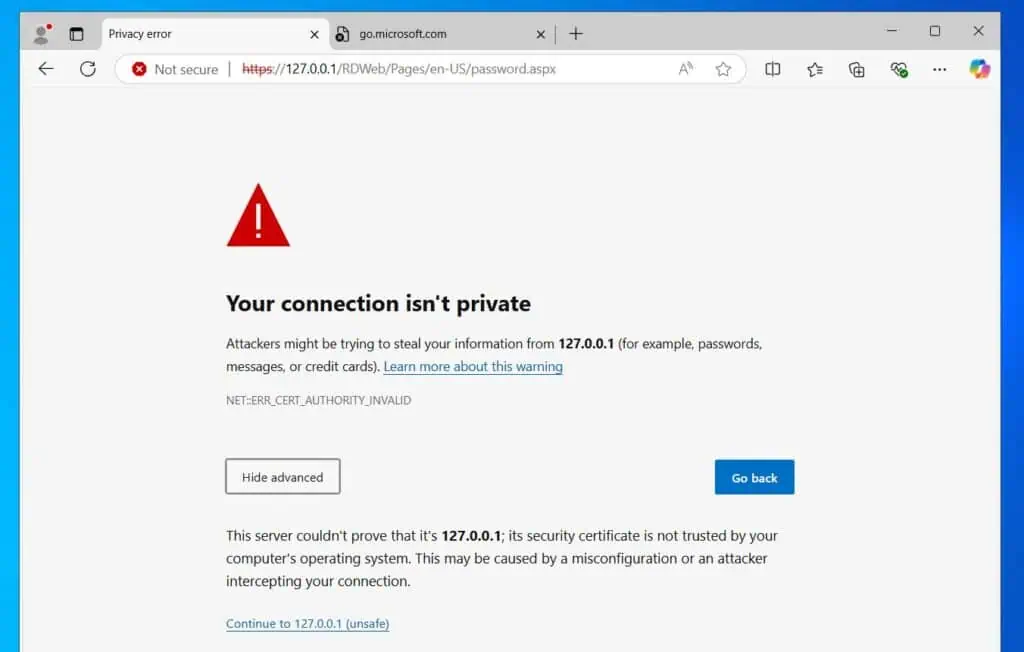
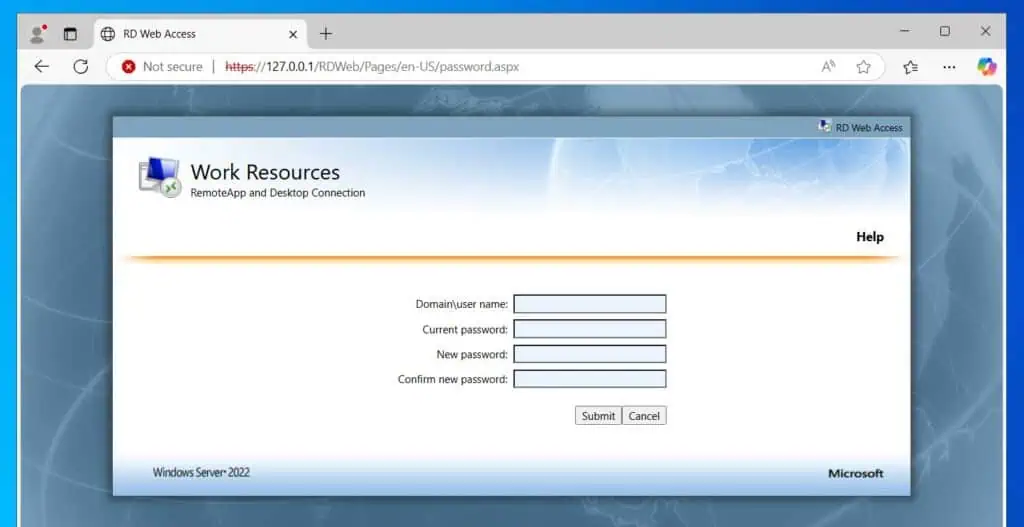
- From a browser on the local server where you configured the self-service password reset, open the URL below:
https://127.0.0.1/RDWeb/Pages/en-US/password.aspx
- You’ll receive a certificate warning. Click Advanced, then Continue.
The site displays the page for changing an AD password.
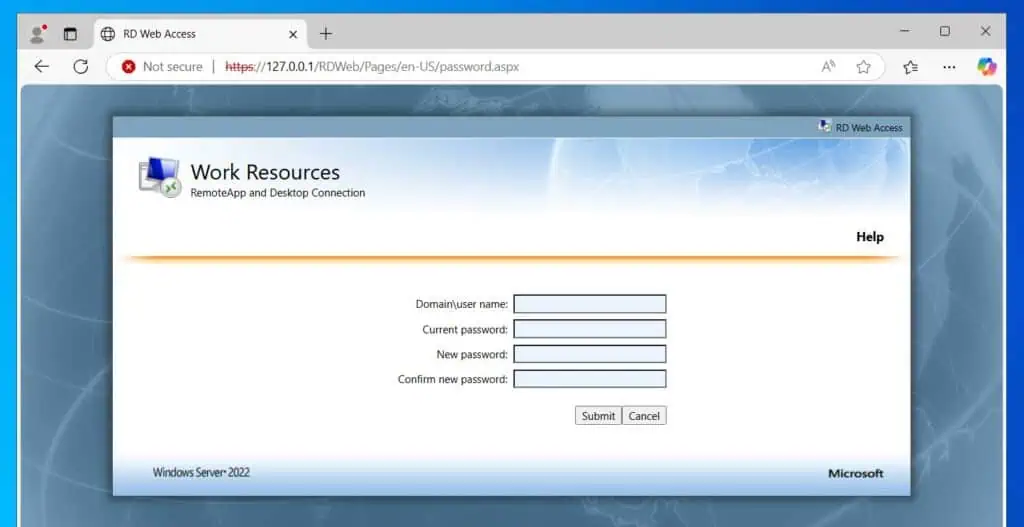
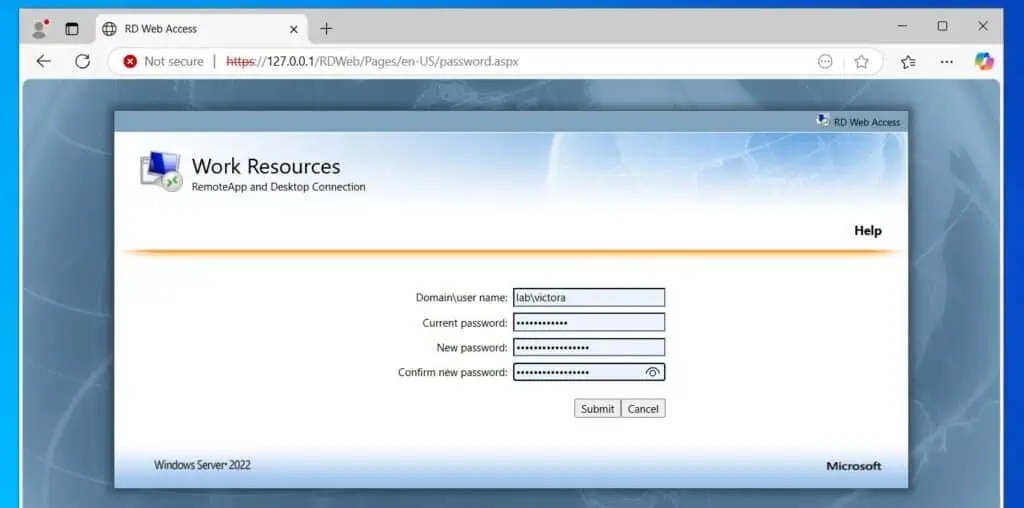
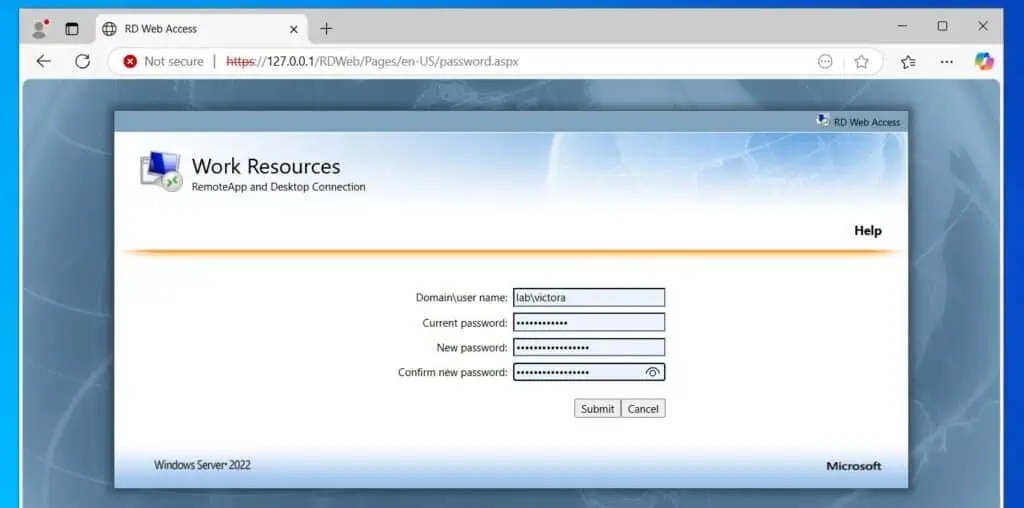
If your users receive the error message – “Your new password does not meet the length, complexity, or history requirements of your domain. Try choosing a different new password.” – modify your domain password policy.
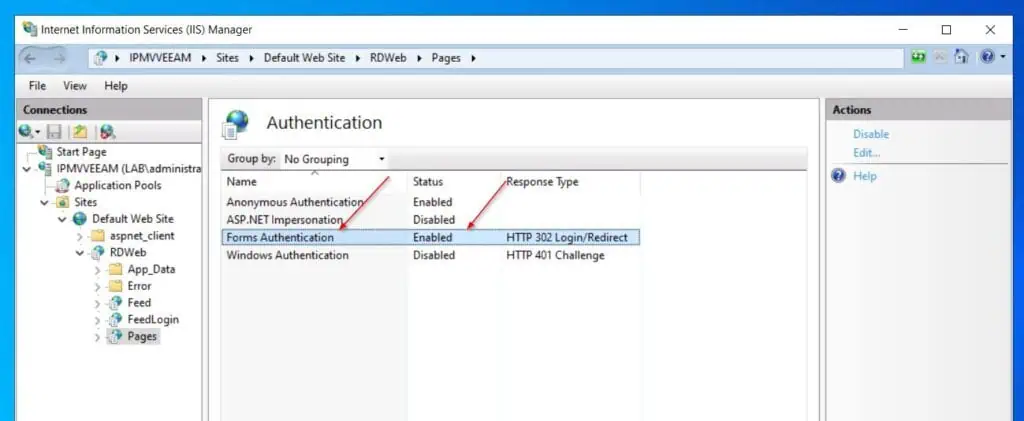
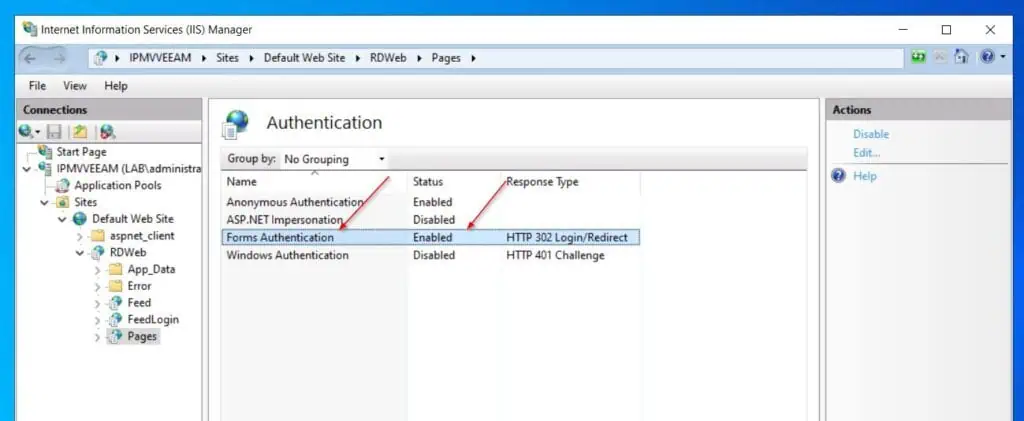
If the password reset does not work, ensure that the Forms Authentication in Sites > Default Web Sites > RDWeb > Pages is enabled.
Conclusion
Providing your users with a way to reset their passwords without contacting the Service Desk is a time saver. In this hands-on guide, I have explained the steps to enable self-service password reset using Remote Desktop Web services.
The first step is to install the IIS web server and the Remote Desktop Web Access Windows Server roles. After that, configure the PasswordChangeEnabled feature of the RDWeb site in IIS.
Finally, configure SSL and you’re good to go.
[ad_2]
Victor Ashiedu
Source link