[ad_1]
NEWYou can now listen to Fox News articles!
Christmas is around the corner, and so is the SantaStealer malware. While the name sounds jolly, this malware is more than capable of ruining your happiness this festive season. The worst part is that this new strain is available to almost anyone willing to pay a small fee. It essentially works as malware-as-a-service, letting buyers target people at scale, obviously not for any legitimate use.
SantaStealer is starting to make noise across Telegram channels and underground hacker forums. It is being marketed as a stealthy, memory-only information stealer that can quietly siphon data without leaving obvious traces on disk.
Memory-only does not mean undetectable. It simply reduces disk artifacts, which can delay detection rather than prevent it altogether. That promise alone is enough to attract cybercriminals, especially at a time when browser-stored passwords, session cookies and crypto wallets remain high-value targets.
MALICIOUS BROWSER EXTENSIONS HIT 4.3M USERS
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
SantaStealer malware is spreading ahead of Christmas, with cybercriminals marketing the data-stealing tool for hire across Telegram and underground forums. (Kurt “CyberGuy” Knutsson)
SantaStealer and how it actually works
SantaStealer operates as a malware-as-a-service, charging $175 per month for its basic tier and $300 per month for the premium plan. Researchers at Rapid7 say the operation rebrands an earlier project called BluelineStealer, with a Russian-speaking developer pushing toward a wider launch before the end of the year.
Despite bold claims about evading detection, Rapid7’s analysis paints a more grounded picture. The samples they examined were not particularly difficult to analyze and lacked the advanced anti-analysis techniques being advertised, which is good news for us. If it can be detected, security tools have a better chance of removing it before it can do serious damage.
Functionally, SantaStealer is still dangerous. It uses 14 separate data-collection modules that run in parallel, pulling information from browsers, messaging apps like Telegram and Discord, gaming platforms such as Steam, crypto wallet apps and extensions, and even local documents. The malware can also take screenshots of your desktop. Stolen data is written to memory, compressed into ZIP files and sent out in 10MB chunks to a hardcoded command-and-control server.
One notable capability is its use of an embedded executable to get around Chrome’s App-Bound Encryption, a security feature introduced in mid-2024. This workaround typically requires the malware to be executed at the user level and is not a remote bypass of Chrome’s security model. Similar tricks have already been used by other info-stealers, showing how quickly attackers test and adapt to new browser protections.
What this says about the current threat landscape
SantaStealer is not fully operational yet and has not been distributed at scale, but it reflects a broader trend in cybercrime. Modern info-stealers are modular, configurable and sold much like regular software. The affiliate panel that Rapid7 observed allows buyers to fine-tune exactly what data the malware steals, from full system sweeps to narrowly targeted attacks focused on specific apps or crypto wallets.
The malware also includes options to avoid infecting systems in certain regions and to delay execution, which can throw off both victims and security analysts. As for how SantaStealer might spread, researchers say recent campaigns increasingly rely on ClickFix-style attacks. These tricks push victims into pasting malicious commands directly into the Windows terminal, often disguised as steps to fix an issue or enable a feature.
More traditional methods are still very much in play. Phishing emails, pirated software, torrent downloads, malicious ads and even deceptive YouTube comments remain effective delivery channels. Once malware like this runs on a system, it needs very little time to grab saved passwords, session cookies and wallet data that can later be abused or sold.
7 steps you can take to stay safe from SantaStealer malware
A few sensible habits and the right tools can significantly reduce your risk, even if malware like this continues to evolve. Here are seven practical steps you can take to stay safe:
1) Use strong antivirus software
Modern antivirus tools don’t just look for known malware signatures. They also monitor suspicious behavior, such as programs trying to grab browser data or run hidden processes. Keep real-time protection enabled and take alerts seriously instead of dismissing them.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android & iOS devices at Cyberguy.com.

A new malware-as-a-service threat known as SantaStealer targets passwords, session cookies and crypto wallets while promoting itself as a stealthy, memory-only attack. (Thomas Trutschel/Photothek via Getty Images)
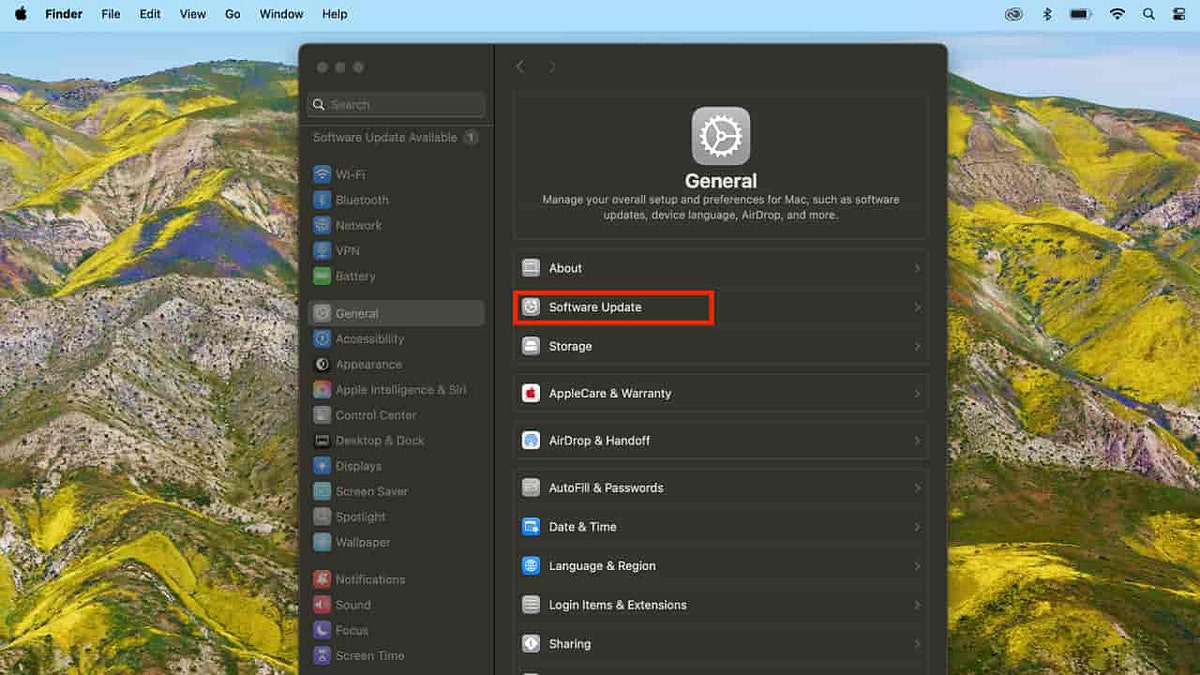
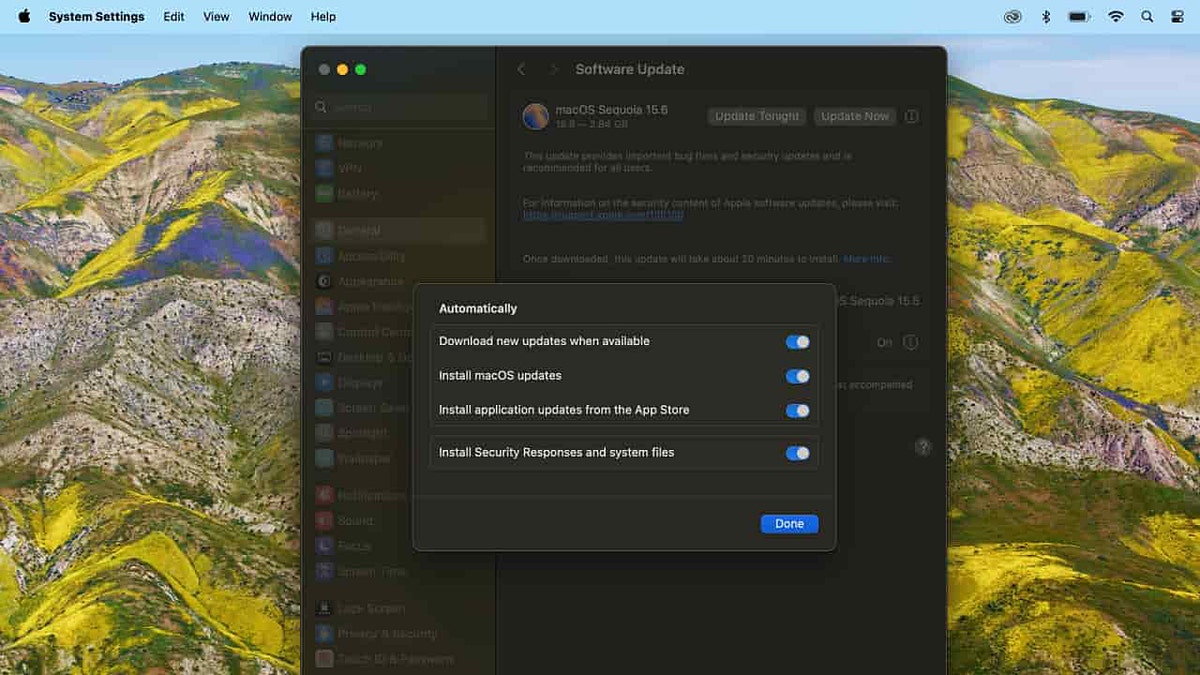
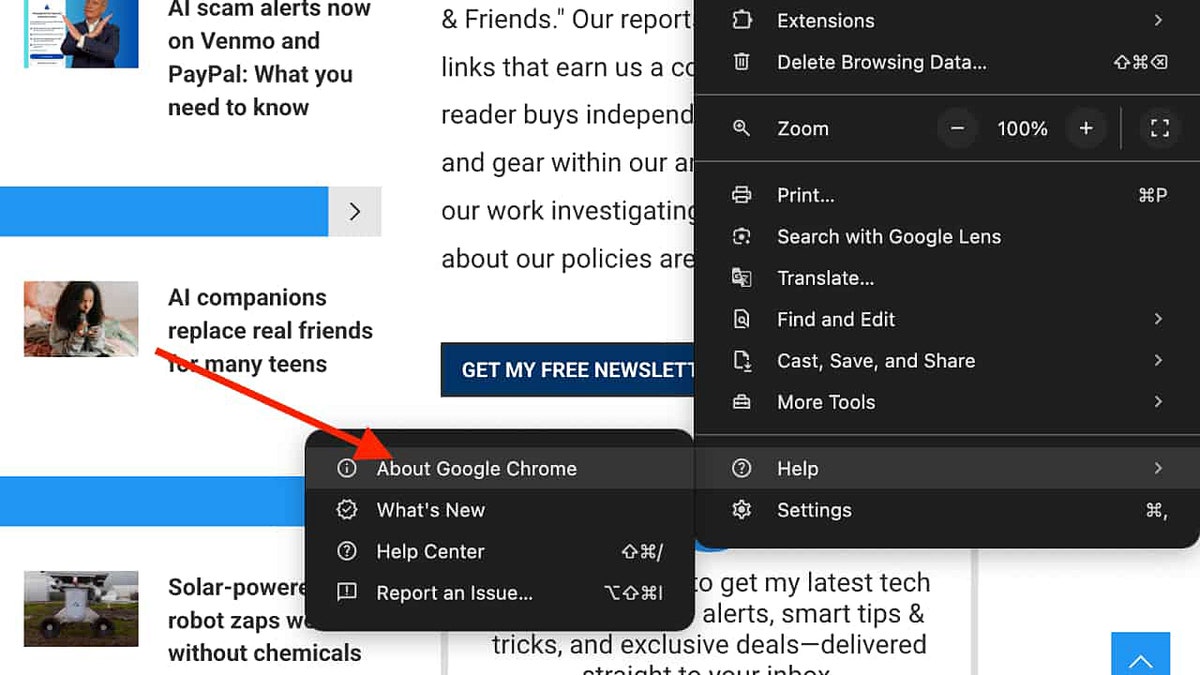
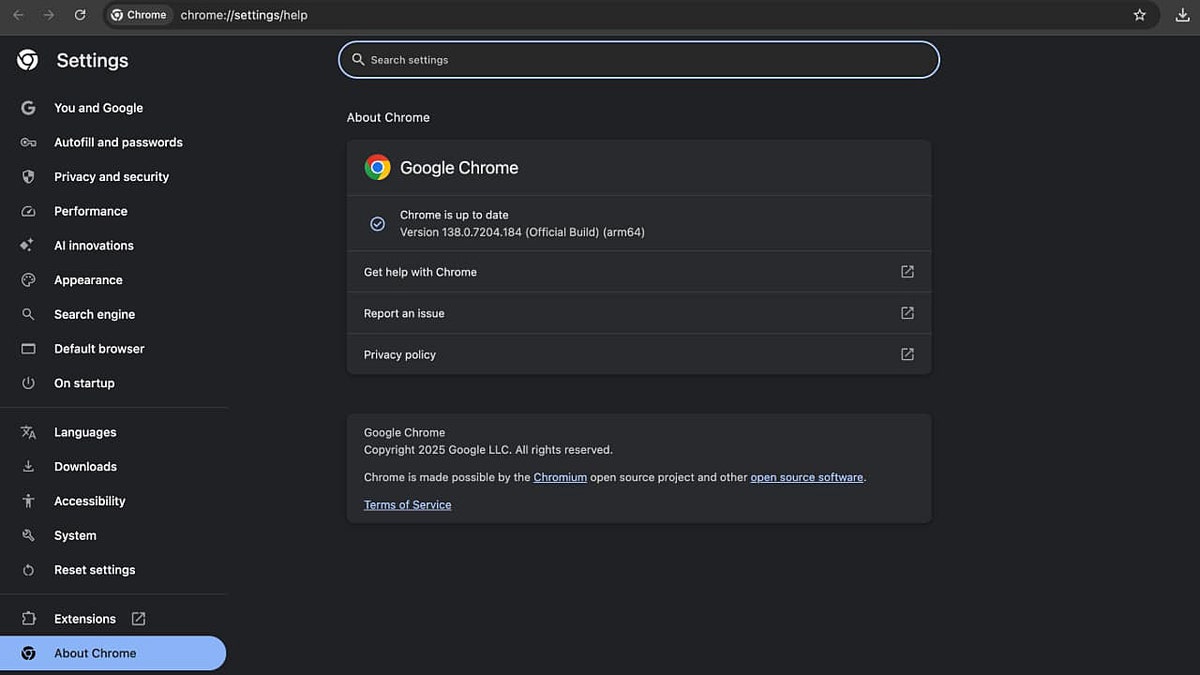
2) Keep your operating system and apps updated
Updates are not just about new features. They often patch security flaws that malware actively targets. This includes your OS, browser, browser extensions, crypto wallet apps and messaging tools. Delaying updates gives attackers a wider window to exploit known weaknesses.
3) Switch to a password manager
Info-stealers love browser-saved passwords because they are easy to grab. A password manager stores your credentials in an encrypted vault and reduces what your browser keeps locally. It also helps you use strong, unique passwords for every service without having to remember them.
Next, see if your email has been exposed in past breaches. Our No. 1 password manager pick includes a built-in breach scanner that checks whether your email address or passwords have appeared in known leaks. If you discover a match, immediately change any reused passwords and secure those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at Cyberguy.com.
FAKE WINDOWS UPDATE PUSHES MALWARE IN NEW CLICKFIX ATTACK
4) Turn on two-factor authentication wherever possible
Even if your password is stolen, 2FA can stop attackers from getting in. App-based authenticators are more secure than SMS codes and should be your first choice for email, crypto exchanges, cloud services and social media accounts.
5) Be extremely careful with commands and “quick fixes”
ClickFix-style attacks rely on trust and urgency. If a website, pop-up or video tells you to paste a command into the Windows terminal to fix something, stop. Unless you fully understand what that command does, assume it is dangerous.
6) Use a personal data removal service
When your email, phone number or other personal details are widely available online, attackers can target you more convincingly. Personal data removal services help take your information down from data broker sites, reducing the chances of targeted phishing or malware lures.
While no service can guarantee the complete removal of your data from the internet, a data removal service is really a smart choice. They aren’t cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically erasing your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to erase your personal data from the internet. By limiting the information available, you reduce the risk of scammers cross-referencing data from breaches with information they might find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting Cyberguy.com.
Get a free scan to find out if your personal information is already out on the web: Cyberguy.com.
HACKERS PUSH FAKE APPS WITH MALWARE IN GOOGLE SEARCHES
7) Avoid pirated software and unverified extensions
Cracked software, torrents and shady browser extensions remain some of the most reliable malware delivery methods. They often bundle info-stealers that run quietly in the background. Stick to official app stores, trusted developers and verified extensions, even if it means skipping a “free” download.

SantaStealer can quietly siphon sensitive data. (Kurt “CyberGuy” Knutsson)
Kurt’s key takeaway
SantaStealer may not yet live up to its own hype, but that should not make you complacent. Early-stage malware often improves quickly once developers patch obvious mistakes. Be cautious with links and attachments from unfamiliar emails, and think twice before running unverified code or browser extensions pulled from public repositories.
When was the last time you checked which extensions have access to your data? Let us know by writing to us at Cyberguy.com.
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
Sign up for my FREE CyberGuy Report
Get my best tech tips, urgent security alerts and exclusive deals delivered straight to your inbox. Plus, you’ll get instant access to my Ultimate Scam Survival Guide – free when you join my CYBERGUY.COM newsletter.
Copyright 2025 CyberGuy.com. All rights reserved.
[ad_2]